Dealing with a Revoked vCenter SSL Certificate
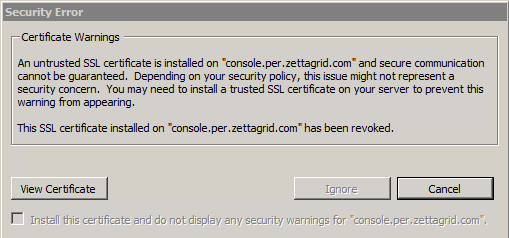
Certificates and VMware (https://www.google.com.au/webhp?sourceid=chrome-instant&ion=1&espv=2&ie=UTF-8#q=vcenter%20ssl%20certificates)… And while I’ve never really had a major issue with SSL certs in VMware mainly because on a personal level I am ok with using self signed or default certificates (queue security nuts) I was forced recently to change a publicly signed vCenter SSL Certificate which also doubled as the Web Client SSL Certificate. This was due to VeriSign revoking the certificate that had been purchased on a per year renewal plan…the vCenter Client doesn’t like revoked certs. !(/images/2016/01/ssl_revoke.png) Prior to vSphere 5.5 my usual trick of simply replacing the rui.crt and rui.key files in the vCenter/Web Client SSL folder and restarting vCenter didn’t work…in fact the vCenter Service (5.5 Update 2) won’t start if its done that way anymore…this is mainly due to the reliance on the SSO and Inventory services that don’t like the SSL thumbprint to be changed underneath them. To resolve this I had to read through and learn how to use the VMware SSL Certificate Automation Tool. Once mastered it’s a great tool and lets you change/update all relevant vSphere SSL Certificates. Below is the quick and easy command line walkthrough to get the job done…note that you need to build up the SSL Certificate Chain correctly and make one small modification the ssl-environment.bat file set ssl_tool_no_cert_san_check=1
C:\ssl-certificate-updater-tool-1308332>ssl-updater.bat
==================================================================
Main menu
Enter the action you want to run
1. Plan your steps to update SSL certificates(Update Steps Planner)
2. Generate Certificate Signing Requests
3. Update Single Sign-On
4. Update Inventory Service
5. Update vCenter Server
6. Update vCenter Orchestrator(vCO)
7. Update vSphere Web Client and Log Browser
8. Update vSphere Update Manager(VUM)
9. End the update process and exit
The chosen action is: 5==================================================================
5. Update the vCenter Server SSL Certificate
1. Update the vCenter Server Trust to Single Sign-On
2. Update the vCenter Server SSL Certificate
3. Update the vCenter Server Trust to Inventory Service
4. Rollback to the previous vCenter Server SSL Certificate
5. Return to the main menu to update other services
The chosen service is: 2
[Tue 19/01/2016 - 13:24:52.46]: The services that are restarted as a part of this operation are: VMware VirtualCenter Server, VMware VirtualCenter Management Webservices and VMware vSphere Profile-Driven Storage Service.
Enter location to the new vCenter Server SSL chain: c:\rui.crt
Enter location to the new vCenter Server private key: c:\rui.key
Enter vCenter Server administrator user name: adm.anthony.spiteri
Enter vCenter Server administrator password (will not be echoed):
"Important: Enter the password carefully. The Certificate Automation Update Tool does not check the validity of the vCenter Server database password."
"A blank or incorrect password will leave the system in an inconsistent state, which will cause the vCenter Server to become unavailable. "
"If the system becomes unstable due to a bad password, see the Troubleshooting Section of KB 2041600."
Enter the vCenter Server original database password (will not be echoed):
Enter Single Sign-On Administrator user: [email protected]
Enter Single Sign-On Administrator password (will not be echoed):
[.] The supplied certificate chain is valid.
Loading 'screen' into random state - done
"Restarting services... (This can take some time)"
"Stopping vCenter Web Services..."
"Stopping vCenter Server..."
"Starting vCenter Server and other services..."
[Tue 19/01/2016 - 13:29:51.41]: Last operation update vCenter Server SSL certificate completed successfully.
[Tue 19/01/2016 - 13:29:51.42]: Go to the next step in the plan that was received from Update Steps Planner.==================================================================
5. Update the vCenter Server SSL Certificate
1. Update the vCenter Server Trust to Single Sign-On
2. Update the vCenter Server SSL Certificate
3. Update the vCenter Server Trust to Inventory Service
4. Rollback to the previous vCenter Server SSL Certificate
5. Return to the main menu to update other services
The chosen service is: 5==================================================================
Main menu
Enter the action you want to run
1. Plan your steps to update SSL certificates(Update Steps Planner)
2. Generate Certificate Signing Requests
3. Update Single Sign-On
4. Update Inventory Service
5. Update vCenter Server
6. Update vCenter Orchestrator(vCO)
7. Update vSphere Web Client and Log Browser
8. Update vSphere Update Manager(VUM)
9. End the update process and exit
The chosen action is: 7==================================================================
7. Update the vSphere Web Client and Log Browser SSL Certificates
1. Update the Web Client Trust to Single Sign-On
2. Update the Web Client Trust to Inventory Service
3. Update the Web Client Trust to vCenter Server
4. Update the Web Client SSL Certificate
5. Update the Log Browser Trust to Single Sign-On
6. Update the Log Browser SSL Certificate
7. Rollback to the previous Web Client SSL Certificate
8. Rollback to the previous Log Browser SSL Certificate
9. Return to the main menu to update other services
The chosen service is: 4
[Tue 19/01/2016 - 15:06:39.60]: The services that are restarted as a part of this operation are: vSphere Web Client
Enter location to the new Web Client SSL chain: c:\rui.crt
Enter location to the new Web Client private key: c:\rui.key
Enter Single Sign-On Administrator user (default value is: [email protected]): [email protected]
Enter Single Sign-On Administrator password (will not be echoed):
[.] The supplied certificate chain is valid.
Stopping the vSphere Web Client...
vSphere Web Client stopped.
Starting vSphere Web Client... (this may take some time)
vSphere Web Client started.
[Tue 19/01/2016 - 15:14:48.21]: Last operation update vSphere Web Client SSL certificate completed successfully.
[Tue 19/01/2016 - 15:14:48.22]: Go to the next step in the plan that was received from Update Steps Planner.A Couple of vCenter and Web Client service restarts later and the SSL Certificate has been replaced. While there are a lot more options there I only needed two steps to replace the original publicly signed certificate as all other certificates where the internally generated certs…As a specific heads up from the KB, these where the issues I ran into
-
SSL Certificate Update fails if vCenter Single Sign-On Password contains spaces or special characters such as &, ^, %, <.If the vCenter Single Sign-On password has a space or any special characters, such as &, ^, %, or <, the configuration of the Inventory service fails.To work around this issue, change the vCenter Single Sign-On password so it does not contain a space or any of the special characters &, ^, %, < in it.
-
If the certificate chain file for vCenter Single Sign-On is out-of-order, you see an error similar to:
Certificate chain is incomplete: the root authority certificate is not present and could not be detected automatically. The presence of the root certificate is required so the other service can establish trust to this service. Try adding the authority certificate manually.To resolve this issue, ensure that the certificate chain file for vCenter Single Sign-On is created in the correct order. For more information, see Generating certificates for use with the VMware SSL Certificate Automation Tool (2044696).
References: http://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2057340 https://my.vmware.com/group/vmware/details?productId=351&downloadGroup=SSLTOOL550
1 Commentarchived