NSX Edge vs vShield Edge: Part 5 – SSL VPN-PLUS
Overview:
The SSL VPN-Plus feature has been around since the VSE 5.x days and as I’ve found out was possibly the best underused feature of the VSE. Contributing to it’s lack of use was the fact that the functionality was not exposed via vCloud Director so one of the best use cases for the SSL VPN remained hidden to those that might have taken advantage of it the most.
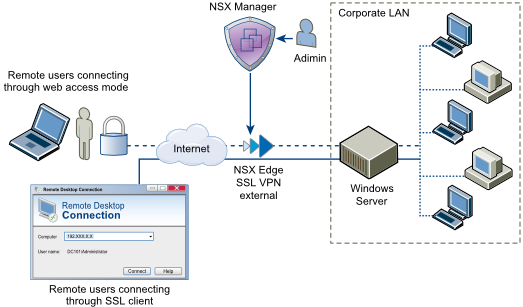
With the SSL VPN-PLUS remote users can connect securely to private networks behind VSE and NSX Edges allowing remote users to access servers and applications in the private networks or Virtual Datacenters.
 The graphic above is pulled from the NSX Online Documentation and shows the basic logical overview of what the SSL VPN-Plus feature enables. Windows is used in the example above but there are also clients for MacOS (Tiger, Leopard, Snow Leopard, Lion, Mountain Lion, and Maverick) or Linux (TCL-TK is required for UI to work. If not present, Linux client can be used using CLI).
The graphic above is pulled from the NSX Online Documentation and shows the basic logical overview of what the SSL VPN-Plus feature enables. Windows is used in the example above but there are also clients for MacOS (Tiger, Leopard, Snow Leopard, Lion, Mountain Lion, and Maverick) or Linux (TCL-TK is required for UI to work. If not present, Linux client can be used using CLI).
Configuring SSL VPN-Plus From Web Client: As a pre-requisite the VSE or NSX Edge requires a Certificate to be available in the edge config. To see how to create a Self Signed SSL Certificate click (http://anthonyspiteri.net/nsx-edge-vs-vshield-edge-part-4-generating-self-signed-ssl-certificates/) to view Part 4. The steps to configure and enable the SSL VPN are listed below with each step expanded out through the rest of the post.
- Add SSL VPN-Plus Server Settings
- Add an IP Pool
- Add a Private Network
- Add Authentication
- Add a User
- Add Installation Package
- Enable the SSL VPN-Plus Service
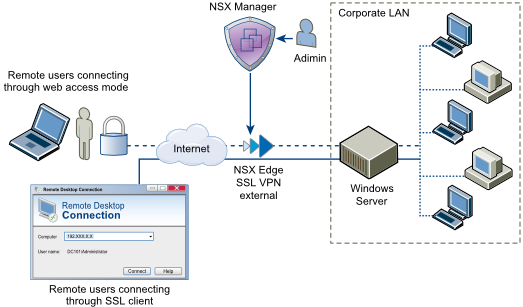
To enable the SSL VPN you need to go to Networking & Security -> NSX Edges, double click on the edge in question and go to the SSL VPN-Plus Tab and then go to Server Settings and click on Change
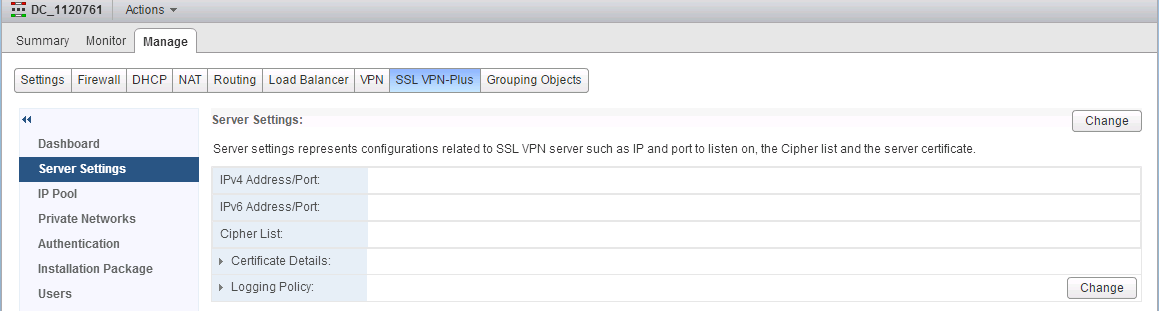 Select the Primary IPv4 Address and choose the SSL Certificate (for the purpose of this example the default should be ok) and click ok. Note that if you are going to be hosting SSL Enabled services off the Edge it’s probably a good idea to use a non standard HTTP Port such as 9443 so as not to have issue binding web services later on.
Select the Primary IPv4 Address and choose the SSL Certificate (for the purpose of this example the default should be ok) and click ok. Note that if you are going to be hosting SSL Enabled services off the Edge it’s probably a good idea to use a non standard HTTP Port such as 9443 so as not to have issue binding web services later on.
 Head to the IP Pool Menu and add an IP Pool. The remote user is assigned a virtual IP address from the IP pool that you create.
Head to the IP Pool Menu and add an IP Pool. The remote user is assigned a virtual IP address from the IP pool that you create.
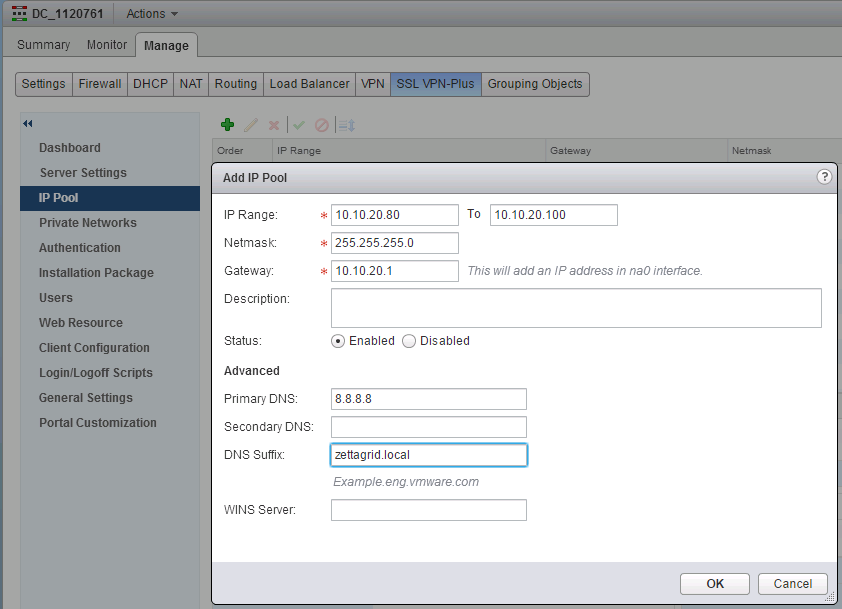 The IP Pool should be on a different Subnet to the configured VNICs
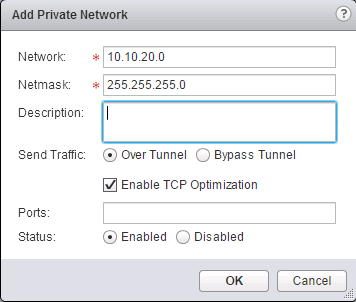
On the Private Networks Menu Add the network that you want the remote user to be able to access.
The IP Pool should be on a different Subnet to the configured VNICs
On the Private Networks Menu Add the network that you want the remote user to be able to access.
- Type the private network IP address.
- Type the netmask of the private network.
- Type a description for the network. (Optional)
- Specify whether you want to send private network and internet traffic over the SSL VPN-Plus enabled NSX Edge or directly to the private server by bypassing the NSX Edge.
- If you selected Send traffic over the tunnel, select Enable TCP Optimization to optimize the internet speed.
- Conventional full-access SSL VPNs tunnel sends TCP/IP data in a second TCP/IP stack for encryption over the internet. This results in application layer data being encapsulated twice in two separate TCP streams. When packet loss occurs (which happens even under optimal internet conditions), a performance degradation effect called TCP-over-TCP meltdown occurs. In essence, two TCP instruments are correcting a single packet of IP data, undermining network throughput and causing connection timeouts. TCP Optimization eliminates this TCP-over-TCP problem, ensuring optimal performance.
- Type the port numbers that you want to open for the remote user to access the corporate internal servers/machines like 3389 for RDP, 20/21 for FTP, and 80 for http. If you want to give unrestricted access to the user, you can leave the Ports field blank.
- Enable the Private Network
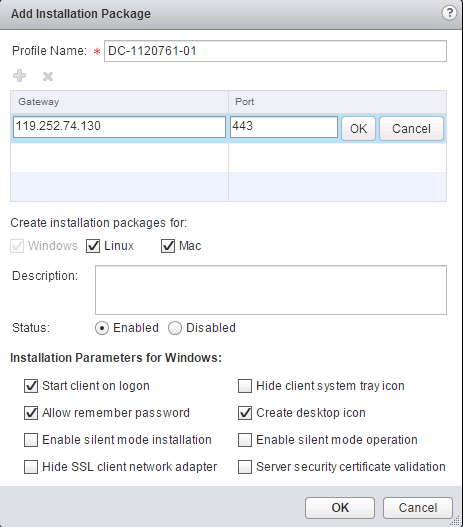
On the Authentication Menu you have the option to add the Authentication method. Instead of a local user, you can add an external authentication server (AD, LDAP, Radius, or RSA) which is bound to the SSL gateway. For this example we will configure Local Authentication…In the Add Authentication Server select Local and configure the following options and click ok. 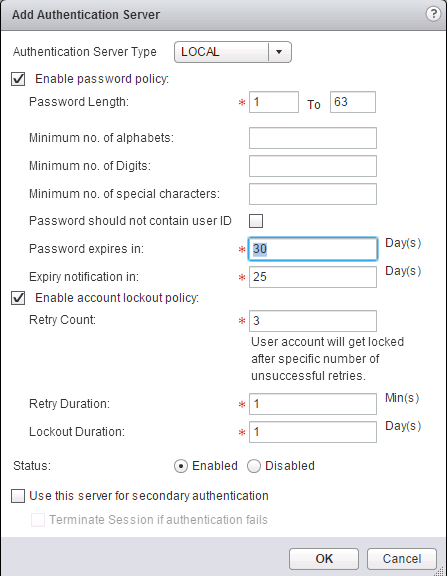 The installation Package is downloaded from the SSL VPN Web UI and installed on remote machine connecting up to the remote network. Go to Installation Package and here you create an installation package of the SSL VPN-Plus client for the remote user. As a default the following needs to be configured.
The installation Package is downloaded from the SSL VPN Web UI and installed on remote machine connecting up to the remote network. Go to Installation Package and here you create an installation package of the SSL VPN-Plus client for the remote user. As a default the following needs to be configured.
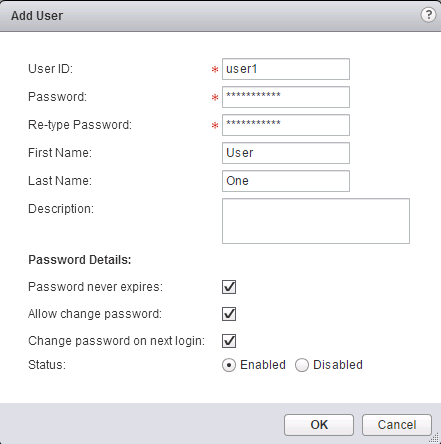
 Go to the Users Page to create a default user account.
Go to the Users Page to create a default user account.
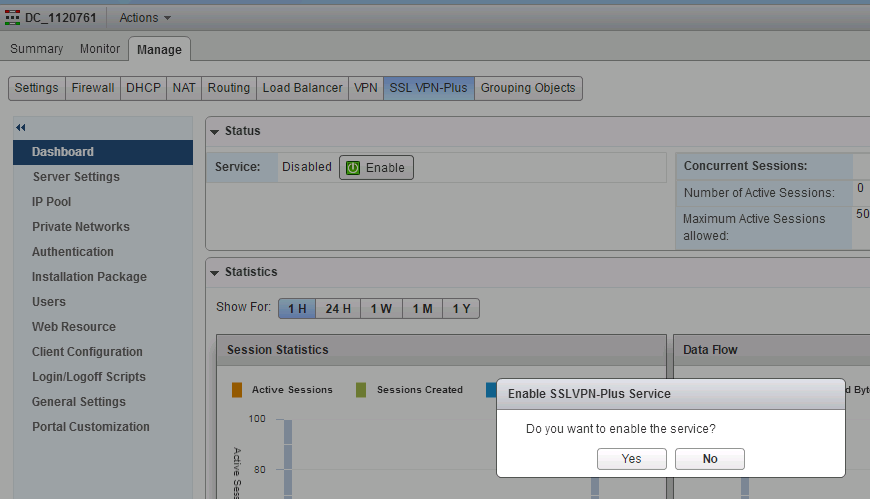
 Head back to the Dashboard Menu and Click on the Enable Button.
Head back to the Dashboard Menu and Click on the Enable Button.
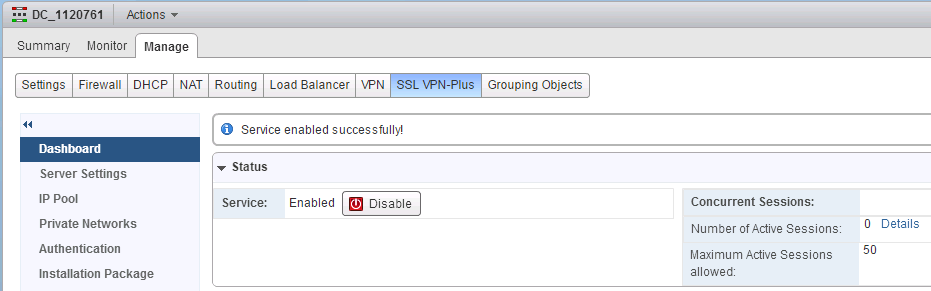
 The Service is now Enabled with the configuration items specified above.
The Service is now Enabled with the configuration items specified above.
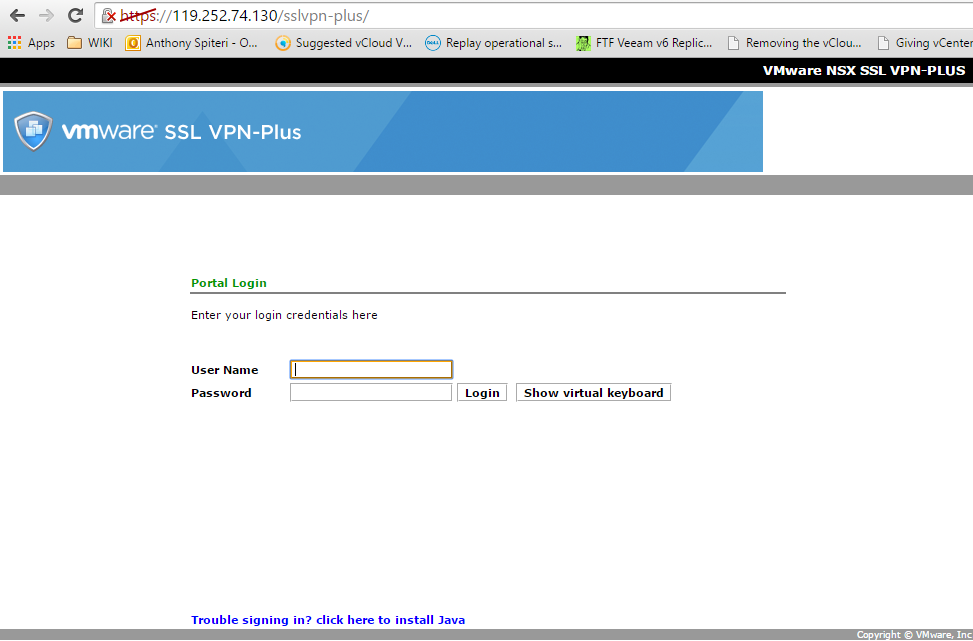
 To test out that the SSL VPN is enabled and accessible you can use a web browser to hit the IP Address and Port selected in the config.
To test out that the SSL VPN is enabled and accessible you can use a web browser to hit the IP Address and Port selected in the config.
 Configuring SSL VPN-Plus With NSX API:
Below are the key API commands to configure and manage SSL VPN-Plus.
Configuring SSL VPN-Plus With NSX API:
Below are the key API commands to configure and manage SSL VPN-Plus.
#
# Viewing SSLVPN Details
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/?enableService=true|False
# METHOD: POST
#ENABLE
https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/?enableService=true
#DISABLE
https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/?enableService=false#
# CONFIGURE IP POOL
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/client/networkextension/ippools/
# METHOD: POST
# CONTENT-TYPE: application/xml
#BASIC EXAMPLE
<?xml version="1.0" encoding="UTF-8"?>
<ipAddressPool>
<description>description</description>
<ipRange>10.10.21.80-10.10.21.100</ipRange>
<netmask>255.255.255.0</netmask>
<gateway>10.10.21.1</gateway>
<primaryDns>8.8.8.8</primaryDns
><dnsSuffix>zettagrid.local</dnsSuffix>
<enabled>true</enabled>
</ipAddressPool>
#ALL OPTIONS
<?xml version="1.0" encoding="UTF-8"?>
<ipAddressPool>
<description>description</description>
<ipRange>10.112.243.11-10.112.243.57</ipRange>
<netmask>255.0.0.0</netmask>
<gateway>192.168.1.1</gateway>
<primaryDns>192.168.10.1</primaryDns <!--optional. -->
<secondaryDns>4.2.2.2</secondaryDns> <!--optional. -->
<dnsSuffix></dnsSuffix>
<winsServer>10.112.243.201</winsServer>
<enabled>true</enabled> <!--optional. Default is true-->
</ipAddressPool>#
# GET ALL IP POOLS
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/client/networkextension/ippools/
# METHOD: GET
#EXAMPLE OUTPUT
<?xml version="1.0" encoding="UTF-8" ?>
<ipAddressPools>
<ipAddressPool>
<objectId>ippool-2</objectId>
<ipRange>10.10.21.80-10.10.21.100</ipRange>
<netmask>255.255.255.0</netmask>
<gateway>10.10.21.1</gateway>
<primaryDns>8.8.8.8</primaryDns>
<secondaryDns />
<dnsSuffix>zettagrid.local</dnsSuffix>
<winsServer />
<description />
<enabled>true</enabled>
</ipAddressPool>
</ipAddressPools>#
# MODIFY IP POOL
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/client/networkextension/ippools/ippool-id
# METHOD: PUT
# CONTENT-TYPE: application/xml
#ALL OPTIONS
<?xml version="1.0" encoding="UTF-8"?>
<ipAddressPool>
<description>description</description>
<ipRange>10.112.243.11-10.112.243.57</ipRange>
<netmask>255.0.0.0</netmask>
<gateway>192.168.1.1</gateway>
<primaryDns>192.168.10.1</primaryDns
<secondaryDns>4.2.2.2</secondaryDns>
<dnsSuffix></dnsSuffix>
<winsServer>10.112.243.201</winsServer>
<enabled>true</enabled>
</ipAddressPool>#
# CONFIGURE SERVER SETTINGS
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/server
# METHOD: PUT
# CONTENT-TYPE: application/xml
#BASIC EXAMPLE
<?xml version="1.0" encoding=”UTF-8”?>
<serverSettings>
<serverAddresses>
<ipAddress>119.252.74.130</ipAddress>
</serverAddresses>
<port>443</port>
<cipherList>
<cipher>RC4-MD5</cipher>
<cipher>AES128-SHA</cipher>
<cipher>AES256-SHA</cipher>
<cipher>DES-CBC3-SHA</cipher>
</cipherList>
</serverSettings>
#ALL OPTIONS
<?xml version="1.0" encoding=”UTF-8”?>
<serverSettings>
<serverAddresses>
<ipAddress>10.112.243.109</ipAddress> <!-- Ipv4 or IPV6 address of any of the external vnic. ipv4 and ipv6 both can not
configured. -->
</serverAddresses>
<port>443</port> <!--optional. Default is 60003 -->
<!-- Certificate has to be generated using certificate REST API and id returned should be mentioned here-->
<!-- <certificateId>certificate-1</certificateId> --> <!-- optional. -->
<cipherList>
<!-- any one or more of the following ciphers can be part of configuration -->
<!—RC4-MD5|AES128-SHA|AES256-SHA|DES-CBC3-SHA-->
<cipher>RC4-MD5</cipher>
<cipher>AES128-SHA</cipher>
<cipher>AES256-SHA</cipher>
<cipher>DES-CBC3-SHA</cipher>
</cipherList>
</serverSettings>
# GET SERVER SETTINGS
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/server
# METHOD: GET
#EXAMPLE OUTPUT
<?xml version="1.0" encoding="UTF-8" ?>
<serverSettings>
<serverAddresses>
<ipAddress>119.252.74.130</ipAddress>
</serverAddresses>
<port>443</port>
<cipherList>
<cipher>RC4-MD5</cipher>
</cipherList>
<sslVersionList />
</serverSettings>#
# ADD A USER
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/auth/localserver/users/
# METHOD: POST
# CONTENT-TYPE: application/xml
#BASIC EXAMPLE
<?xml version="1.0" encoding="UTF-8"?>
<user>
<userId>USER02</userId>
<password>password$12</password>
<firstName>Test</firstName>
<lastName>User</lastName>
<description></description>
<passwordNeverExpires>true</passwordNeverExpires>
</user>
#ALL OPTIONS
<?xml version="1.0" encoding="UTF-8"?>
<user>
<userId>stalin</userId>
<password>apple@123</password>
<firstName>STALIN</firstName>
<lastName>RAJAKILLI</lastName>
<description>This user belong to vsm team</description>
<disableUserAccount>false</disableUserAccount> <!--optional. Default is false-->
<passwordNeverExpires>true</passwordNeverExpires> <!--optional. Default is false-->
<allowChangePassword>
<changePasswordOnNextLogin>false</changePasswordOnNextLogin> <!--optional. Default is false-->
</allowChangePassword>
</user>
# MODIFY A USER
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/auth/localserver/users/
# METHOD: PUT
#BASIC EXAMPLE
<?xml version="1.0" encoding="UTF-8"?>
<user>
<userId>USER02</userId>
<password>password$12</password>
<firstName>Test</firstName>
<lastName>Change</lastName>
<description></description>
<passwordNeverExpires>true</passwordNeverExpires>
</user>
# QUERY USERS
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/auth/localserver/users/
# METHOD: GET
#EXAMPLE OUTPUT
<?xml version="1.0" encoding="UTF-8" ?>
<usersInfo>
<user>
<objectId>user-2</objectId>
<userId>USER02</userId>
<firstName>Test</firstName>
<lastName>User</lastName>
<description />
<disableUserAccount>true</disableUserAccount>
<passwordNeverExpires>true</passwordNeverExpires>
</user>
<user>
<objectId>user-1</objectId>
<userId>user1</userId>
<firstName>User</firstName>
<lastName>One</lastName>
<description />
<disableUserAccount>false</disableUserAccount>
<passwordNeverExpires>true</passwordNeverExpires>
<allowChangePassword>
<changePasswordOnNextLogin>false</changePasswordOnNextLogin>
</allowChangePassword>
</user>
</usersInfo>
# DELETE USERS
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/auth/localserver/users/user-id
# METHOD: DELETE
#EXAMPLE
https://10.38.0.8/api/4.0/edges/edge-264/sslvpn/config/auth/localserver/users/user-2#
# Add INSTALL PACKAGE
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/client/networkextension/installpackages/
# METHOD: POST
# CONTENT-TYPE: application/xml
#BASIC EXAMPLE
<?xml version="1.0" encoding="UTF-8"?>
<clientInstallPackage>
<profileName>DC_2893-PKG01</profileName>
<gatewayList>
<gateway>
<hostName>119.252.74.130</hostName>
<port>443</port>
</gateway>
</gatewayList>
<rememberPassword>true</rememberPassword>
<createDesktopIcon>true</createDesktopIcon>
<createLinuxClient>true</createLinuxClient>
<createMacClient>true</createMacClient>
<description></description>
<enabled>true</enabled>
</clientInstallPackage>
#ALL OPTIONS
<?xml version="1.0" encoding="UTF-8"?>
<clientInstallPackage>
<profileName>client</profileName>
<gatewayList>
<gateway>
<hostName>10.112.243.123</hostName>
<port>443</port> <!--optional. Default is 443-->
</gateway>
</gatewayList>
<startClientOnLogon>false</startClientOnLogon> <!--optional. Default is false-->
<hideSystrayIcon>true</hideSystrayIcon> <!--optional. Default is false-->
<rememberPassword>true</rememberPassword> <!--optional. Default is false-->
<silentModeOperation>true</silentModeOperation> !--optional. Default is false-->
<silentModeInstallation>false</silentModeInstallation> <!--optional. Default is false-->
<hideNetworkAdaptor>false</hideNetworkAdaptor> <!--optional. Default is false-->
<createDesktopIcon>true</createDesktopIcon> <!--optional. Default is true-->
<enforceServerSecurityCertValidation>false</enforceServerSecurityCertValidation> <!--optional. Default is true-->
<createLinuxClient>false</createLinuxClient> <!--optional. Default is false-->
<createMacClient>false</createMacClient> <!--optional. Default is false-->
<description>windows client</description>
<enabled>true</enabled> <!--optional. Default is true-->
</clientInstallPackage>
# QUERY CLIENT INSTALLER
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/client/networkextension/installpackages/
# METHOD: GET
#EXAMPLE OUTPUT
<?xml version="1.0" encoding="UTF-8" ?>
<clientInstallPackages>
<clientInstallPackage>
<objectId>clientinstallpackage-1</objectId>
<profileName>DC-1120761-01</profileName>
<gatewayList>
<gateway>
<hostName>119.252.74.130</hostName>
<port>443</port>
</gateway>
</gatewayList>
<createLinuxClient>true</createLinuxClient>
<createMacClient>true</createMacClient>
<startClientOnLogon>true</startClientOnLogon>
<hideSystrayIcon>false</hideSystrayIcon>
<rememberPassword>true</rememberPassword>
<silentModeOperation>false</silentModeOperation>
<silentModeInstallation>false</silentModeInstallation>
<hideNetworkAdaptor>false</hideNetworkAdaptor>
<createDesktopIcon>true</createDesktopIcon>
<enforceServerSecurityCertValidation>false</enforceServerSecurityCertValidation>
<description />
<enabled>true</enabled>
</clientInstallPackage>
<clientInstallPackage>
<objectId>clientinstallpackage-2</objectId>
<profileName>DC_2893-PKG01</profileName>
<gatewayList>
<gateway>
<hostName>119.252.74.130</hostName>
<port>443</port>
</gateway>
</gatewayList>
<createLinuxClient>true</createLinuxClient>
<createMacClient>true</createMacClient>
<startClientOnLogon>false</startClientOnLogon>
<hideSystrayIcon>false</hideSystrayIcon>
<rememberPassword>true</rememberPassword>
<silentModeOperation>false</silentModeOperation>
<silentModeInstallation>false</silentModeInstallation>
<hideNetworkAdaptor>false</hideNetworkAdaptor>
<createDesktopIcon>true</createDesktopIcon>
<enforceServerSecurityCertValidation>false</enforceServerSecurityCertValidation>
<description />
<enabled>true</enabled>
</clientInstallPackage>
</clientInstallPackages>
# DELETE CLIENT INSTALLER
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config/client/networkextension/installpackages/clientinstallpackage-x
# METHOD: DELETE
#EXAMPLE
https://10.38.0.8/api/4.0/edges/edge-264/sslvpn/config/auth/localserver/users/clientinstallpackage-1#
# Viewing SSLVPN Details
# API CALL: https://NSX-MGR-IP/api/4.0/edges/edge-id/sslvpn/config
# METHOD: GET
#OUTPUT EXAMPLE
<?xml version="1.0" encoding="UTF-8" ?>
<sslvpnConfig>
<version>17</version>
<enabled>true</enabled>
<logging>
<enable>false</enable>
<logLevel>info</logLevel>
</logging>
<advancedConfig>
<enableCompression>false</enableCompression>
<forceVirtualKeyboard>false</forceVirtualKeyboard>
<randomizeVirtualkeys>false</randomizeVirtualkeys>
<preventMultipleLogon>false</preventMultipleLogon>
<clientNotification />
<enablePublicUrlAccess>false</enablePublicUrlAccess>
<timeout>
<forcedTimeout>0</forcedTimeout>
<sessionIdleTimeout>10</sessionIdleTimeout>
</timeout>
</advancedConfig>
<clientConfiguration>
<autoReconnect>true</autoReconnect>
<upgradeNotification>false</upgradeNotification>
</clientConfiguration>
<layoutConfiguration>
<portalTitle>VMware NSX SSL VPN-PLUS</portalTitle>
<companyName>Zettagrid</companyName>
<logoExtention>jpg</logoExtention>
<logoUri>/api/4.0/edges/edge-264/sslvpn/config/layout/images/portallogo</logoUri>
<logoBackgroundColor>FFFFFF</logoBackgroundColor>
<titleColor>009900</titleColor>
<topFrameColor>000000</topFrameColor>
<menuBarColor>999999</menuBarColor>
<rowAlternativeColor>FFFFFF</rowAlternativeColor>
<bodyColor>FFFFFF</bodyColor>
<rowColor>F5F5F5</rowColor>
</layoutConfiguration>
<ipAddressPools>
<ipAddressPool>
<objectId>ippool-2</objectId>
<ipRange>10.10.21.80-10.10.21.100</ipRange>
<netmask>255.255.255.0</netmask>
<gateway>10.10.21.1</gateway>
<primaryDns>8.8.8.8</primaryDns>
<secondaryDns />
<dnsSuffix>zettagrid.local</dnsSuffix>
<winsServer />
<description />
<enabled>true</enabled>
</ipAddressPool>
</ipAddressPools>
<privateNetworks>
<privateNetwork>
<objectId>privatenetwork-1</objectId>
<network>10.10.20.0/24</network>
<sendOverTunnel>
<optimize>true</optimize>
</sendOverTunnel>
<description />
<enabled>true</enabled>
</privateNetwork>
</privateNetworks>
<users>
<user>
<objectId>user-1</objectId>
<userId>user1</userId>
<firstName>User</firstName>
<lastName>One</lastName>
<description />
<disableUserAccount>false</disableUserAccount>
<passwordNeverExpires>true</passwordNeverExpires>
<allowChangePassword>
<changePasswordOnNextLogin>false</changePasswordOnNextLogin>
</allowChangePassword>
</user>
</users>
<clientInstallPackages>
<clientInstallPackage>
<objectId>clientinstallpackage-1</objectId>
<profileName>DC-1120761-01</profileName>
<gatewayList>
<gateway>
<hostName>119.252.74.130</hostName>
<port>443</port>
</gateway>
</gatewayList>
<createLinuxClient>true</createLinuxClient>
<createMacClient>true</createMacClient>
<startClientOnLogon>true</startClientOnLogon>
<hideSystrayIcon>false</hideSystrayIcon>
<rememberPassword>true</rememberPassword>
<silentModeOperation>false</silentModeOperation>
<silentModeInstallation>false</silentModeInstallation>
<hideNetworkAdaptor>false</hideNetworkAdaptor>
<createDesktopIcon>true</createDesktopIcon>
<enforceServerSecurityCertValidation>false</enforceServerSecurityCertValidation>
<description />
<enabled>true</enabled>
</clientInstallPackage>
</clientInstallPackages>
<authenticationConfiguration>
<passwordAuthentication>
<authenticationTimeout>1</authenticationTimeout>
<primaryAuthServers>
<localAuthServer>
<authServerType>local</authServerType>
<objectId>authserver-1</objectId>
<order>1</order>
<isSecondaryAuthServer>false</isSecondaryAuthServer>
<terminateSessionOnAuthFails>false</terminateSessionOnAuthFails>
<enabled>true</enabled>
<passwordPolicy>
<minLength>1</minLength>
<maxLength>63</maxLength>
<minAlphabets>0</minAlphabets>
<minDigits>0</minDigits>
<minSpecialChar>0</minSpecialChar>
<allowUserIdWithinPassword>true</allowUserIdWithinPassword>
<passwordLifeTime>30</passwordLifeTime>
<expiryNotification>25</expiryNotification>
</passwordPolicy>
<accountLockoutPolicy>
<retryCount>3</retryCount>
<retryDuration>1</retryDuration>
<lockoutDuration>1</lockoutDuration>
</accountLockoutPolicy>
</localAuthServer>
</primaryAuthServers>
<secondaryAuthServer />
</passwordAuthentication>
</authenticationConfiguration>
<serverSettings>
<serverAddresses>
<ipAddress>119.252.74.130</ipAddress>
</serverAddresses>
<port>443</port>
<cipherList>
<cipher>RC4-MD5</cipher>
</cipherList>
<sslVersionList />
</serverSettings>
</sslvpnConfig>