Quick Fix: vCloud Director SP None of the Cells have a vCenter Proxy Service Running. SSL Protocol Fix
![]() vCloud Director SP 8.20 was (http://anthonyspiteri.net/released-vcloud-director-sp-8-20-with-html5-goodness/) and I wanted to highlight an issue I ran into while testing of the BETA. I hadn’t come across this issue in previous versions of vCD and even though it relates to the fact I had a vCenter 5.5 I thought it worth a post now that 8.20 has GA’ed.
After I upgraded my cells I got the fairly common error message under the Cloud Cells section of the Manage & Monitor menu telling me that I didn’t have a vCenter Proxy service running. It’s something all vCD administrators would have seen over the years, so I did the usual troubleshooting step of going of reconnecting the vCenter under vSphere Resources. This didn’t work, so I did what comes naturally and cleared the Quartz Tables in the vCD database without any success.
Failed to connect to the vCenter. Please check if this is a valid vCenter server and the credentials are correct.
The NestedESXi lab was running vCenter 5.5 U3b and after a bit of searching I came across a post in the vCloud BETA forums relating to this issue:
vCloud Director SP 8.20 was (http://anthonyspiteri.net/released-vcloud-director-sp-8-20-with-html5-goodness/) and I wanted to highlight an issue I ran into while testing of the BETA. I hadn’t come across this issue in previous versions of vCD and even though it relates to the fact I had a vCenter 5.5 I thought it worth a post now that 8.20 has GA’ed.
After I upgraded my cells I got the fairly common error message under the Cloud Cells section of the Manage & Monitor menu telling me that I didn’t have a vCenter Proxy service running. It’s something all vCD administrators would have seen over the years, so I did the usual troubleshooting step of going of reconnecting the vCenter under vSphere Resources. This didn’t work, so I did what comes naturally and cleared the Quartz Tables in the vCD database without any success.
Failed to connect to the vCenter. Please check if this is a valid vCenter server and the credentials are correct.
The NestedESXi lab was running vCenter 5.5 U3b and after a bit of searching I came across a post in the vCloud BETA forums relating to this issue:
Starting with VDC 8.20, the SSL protocol ‘TLSv1’ is no longer supported by default in the product for security reasons (as a server to serve the REST API request, but also as a client when talking to vCenter). The version of vCenter you are running (please confirm which version), is older and probably only supports TLSv1.
Which explains the errors I also had been observing. Note that from 5.5 Update 3e and 6.0 Update 3 and later TLS v1.0 has been disabled and should be disabled.
Due to security concerns in the TLSv1.0 protocol, both Payment Card Industry (PCI) and BSI organizations have suggested to implement and enable TLSv1.1 or TLSv1.2, and move away from the use of TLSv1.0 as soon as possible
Even though it’s not suggested I needed to enable TLS v1 so that vCD SP 8.20 could connect to the vCenter. The following steps where done to enable TLSv1 which was based off (https://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2112282) outlining why cells no longer enable SSL v3 by default and talks about a cell management tool command that configures the allowed SSL Protocols vCD uses during the handshake process with vCenter.
The SSL V3 protocol has serious vulnerability, described in CVE-2014-3566. As of vCloud Director 5.5.3, cells no longer enable SSL V3 by default for internal and external HTTPS connections. The vCloud Director cell management tool has been updated with a new subcommand that enables the system administrator to configure the set of SSL protocols that the cell offers to use during the SSL handshake process. This new subcommand has been made available in vCloud Director 5.5.3
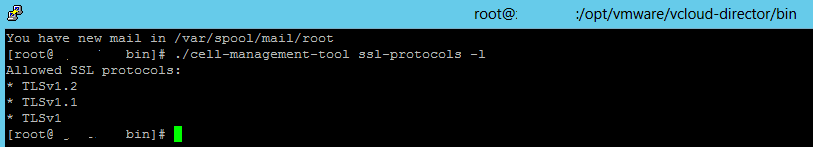
Run the following command on the vCD cell in /opt/vmware/vcloud/bin/
./cell-management-tool ssl-protocols -d SSLv3,SSLv2Hello
After that is done restart the cell and check to make sure you have a listener and that vCenter is connected. If you run the ssl-protocols command with a -l flag it will show you what ssl-protocols are allowed. By default you should now only have TLS v1.1 and 1.2 enabled, but in my case I also needed v1.
 Finally, it’s worth repeating that TLS v1 shouldn’t be used in production, but if you are still running older versions of 5.5 and 6.0 in your labs then this will help.
References:
https://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2112282
https://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2145796
Finally, it’s worth repeating that TLS v1 shouldn’t be used in production, but if you are still running older versions of 5.5 and 6.0 in your labs then this will help.
References:
https://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2112282
https://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2145796