NSX vCloud Retrofit: Overlapping Networks in vCD with NSX Virtual Wires
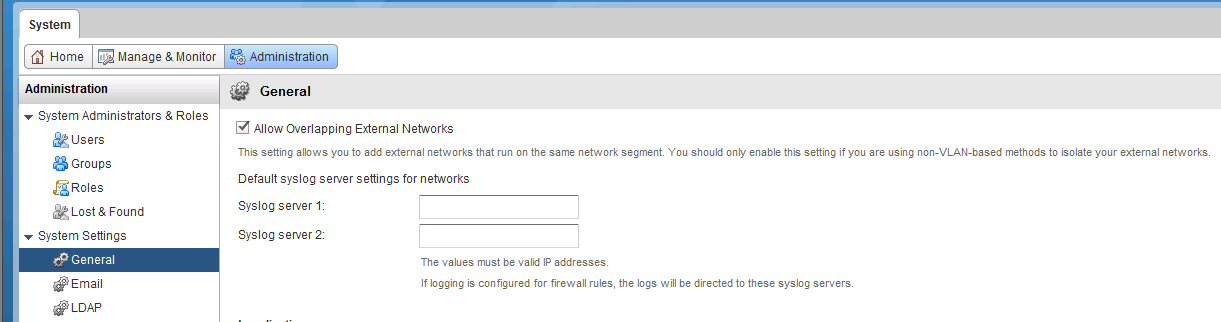
Part 4: vCloud Director Overlapping Networks: vCloud Director has the ability to allow Overlapping Network segments configurable from the Administration Tab of the vCD UI. Traditionally for those using VLAN backed External Networks and Network Pools this would represent a potential risk to clients if admins where not careful provisioning network resources. If the same VLAN was mistakenly configured there could be the possibility for client networks to see each other meaning a really bad day for providers of multi-tenancy platforms. Where this is required is when VXLAN is in play…The VXLAN Transport network is configured on the one VLAN which then carries all the Logical Switch Network Segments or VNI’s. Even though vCD is not aware of NSX you can still connect up Virtual Datacenter vApps and VMs to NSX Edge Gateways via VXLAN virtual wires. To achieve that you need to check the Allow Overlapping External Networks box as shown below. !(/images/2015/05/vCD_overlap.png) If this isn’t Checked you will get the following error in the vCD UI !(/images/2015/05/vCD_overlap_2.png) With Overlapping Networks in place your network pools are also able to be VXLAN backed and used in conjunction with retrofitted External Networks connected to NSX Edges for advanced Edge Gateway Services. Bonus Tip: vCloud Director filters certain PortGroups based on their name of which NSX Created Virtual Wire Portgroups are one of those filtered. To have an NSX Virtual Wire appear in the vCD UI you need to rename the PortGroup similar to what’s shown below. !(/images/2015/05/vCD_overlap_4.png)!(/images/2015/05/vCD_overlap_5.png) This blog series extends my NSX Bytes Blog Posts to include a more detailed look at how to deploy NSX 6.1.x into an existing vCloud Director Environment. Initially we will be working with vCD 5.5.x which is the non SP Fork of vCD, but as soon as an upgrade path for 5.5.2 -> 5.6.x is released I’ll be including the NSX related improvements in that release.
- Part 1: Intro and VSM to NSX Manager Upgrade
- Part 2: NSX Manager Configuration and vCD VSE Deployment Validation
- Part 3: Controller Deployment, Host Preparation and VXLAN Config
- Part 4: Overlapping Networks in vCD with NSX Virtual Wires
2 Commentsarchived