Quick Post: Using Terraform to Deploy an Ansible Control Node on vSphere
In the continuing spirit of Terraforming all things, when I started to look into Ansible I wanted a way to have the base Control Node installed in a repeatable and consistent way. The setup and configuration of Ansible can be tricky and what I learnt in configuring the Ansible Control Node is that there can be a few dependencies that need to be in sync to line everything up. I also wanted to include some other modules and dependancies specifically related to the work that i’ll be doing with Windows Servers.
Requirements:
CentOS Template prepared and ready for deployment form vCenter - see example configuration http://everything-virtual.com/2016/05/06/creating-a-centos-7-2-vmware-gold-template/ The Terraform templates included in this repository requires Terraform to be available locally on the machine running the templates. Before you begin, please verify that you have the following information:
- Download Terraform (tested version 0.12.07) binary to your workstation.
- Terraform vSphere Provider
- Gather the VMware credentials required to communicate to vCenter
- Update the variable values in the
terraform.tfvarsfile. - Update the resource values in the
main.tffile.
I borrowed some of the steps off Markus Kraus’s great work around configuring his Ansible Development environment. But also had to work against some complications that I had working with my CentOS 7 VMware Template due to Python 2.7x being the default version that comes with that distribution build. I also included the modules for Kerberos authentication when working with Windows Servers connected to Active Directory Domains.
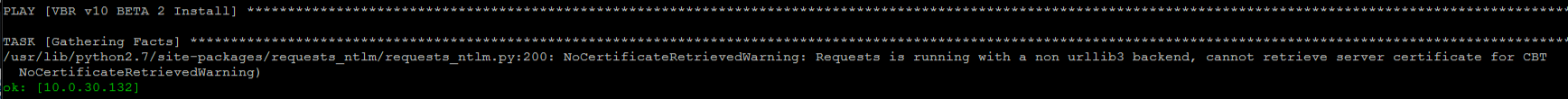
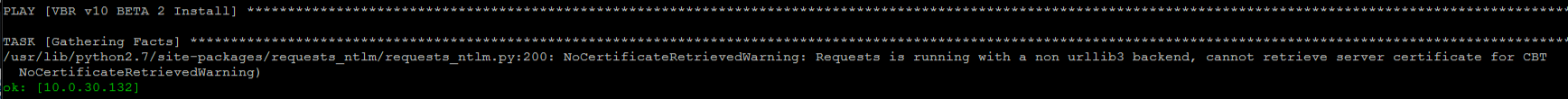
While it wasn’t directly impacting the Playbook’s I was running, I was getting the following warning while running NTLM or Kerberos authentication against any Windows server:
 Given that Python 2.7 was set to be unsupported early next year, I was determined to have Ansible running off Python3. The combination and order of Linux packages and dependencies to get that working wasn’t straight forward and as you can see below in the main VM Terraform resource declaration, there are a lot of commands to make that happen.
Terraform Breakdown:
Given that Python 2.7 was set to be unsupported early next year, I was determined to have Ansible running off Python3. The combination and order of Linux packages and dependencies to get that working wasn’t straight forward and as you can see below in the main VM Terraform resource declaration, there are a lot of commands to make that happen.
Terraform Breakdown:
+---deploy_ansible_CentOS
|
| anisible-control-vm.tf
| configure.sh
| configure2.sh
| main.tf
| output.tf
| README.md
| terraform.tfvars
| variables.tf
| versions.tfThere isn’t a lot to the Terraform code, other than deploying a cloned CentOS 7 Virtual Machine with the configured network setup via the Terraform Guest Customizations. Once the VM has been deployed and configured, the initial package deployment takes place…there are then two seperate configuration scripts which are uploaded and executed via SSH via the remote-exec blocks.The last remote-exec block is the list of commands that works to install Ansible with PIP and using Phython3.
#Install PIP, WinRM and Ansible
provisioner "remote-exec" {
inline = [
"python3 -m pip install --upgrade --force-reinstall pip",
"pip3 install pyvmomi",
"pip3 install pywinrm",
"pip3 install pywinrm>=0.3.0",
"pip3 install --ignore-installed pywinrm>=0.3.0",
"python3 -m pip install --upgrade pip",
"pip3 install ansible",
"ansible --version",
]The final command of the Terraform Plan execution is to list the installed Ansible version.
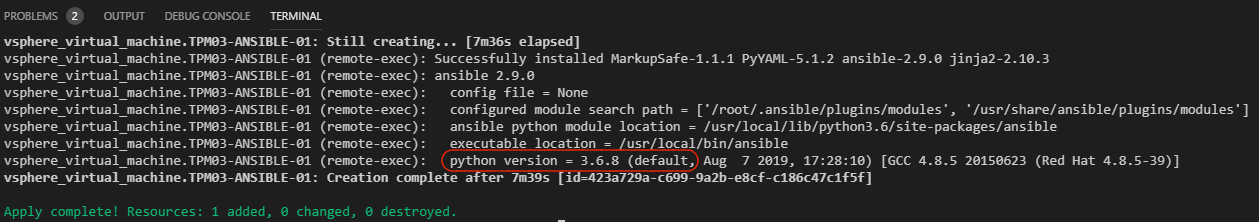 End to end the deployment takes about 7-8 minutes depending on your storage… Once done we have a fully functional Ansible Control Node ready for automation goodness!
This might seem like a little chicken or the egg… but Terraform and Ansible represent both sides of the IaC spectrum. As I mention in the README.md … time to try work out this Ansible thing out a little more!
https://github.com/anthonyspiteri/terraform
References:
Ansible Development environment
End to end the deployment takes about 7-8 minutes depending on your storage… Once done we have a fully functional Ansible Control Node ready for automation goodness!
This might seem like a little chicken or the egg… but Terraform and Ansible represent both sides of the IaC spectrum. As I mention in the README.md … time to try work out this Ansible thing out a little more!
https://github.com/anthonyspiteri/terraform
References:
Ansible Development environment