
NSX Bytes: Critical Update for NSX-v and vCNS
I generally don’t post around security releases but after going through the notes on CVE-2016-2079 I thought it was important enough to dedicate a post aroun...
Tag
5 posts

I generally don’t post around security releases but after going through the notes on CVE-2016-2079 I thought it was important enough to dedicate a post aroun...
As mentioned last week VMware released vCloud Director SP 8.10 and with it a list of significant new features and improvements. In this series I'll go throug...

For a while now we have known that vCloud Networking and Security's days where numbered ...with the release of NSX as a replacement+ product it had been comm...
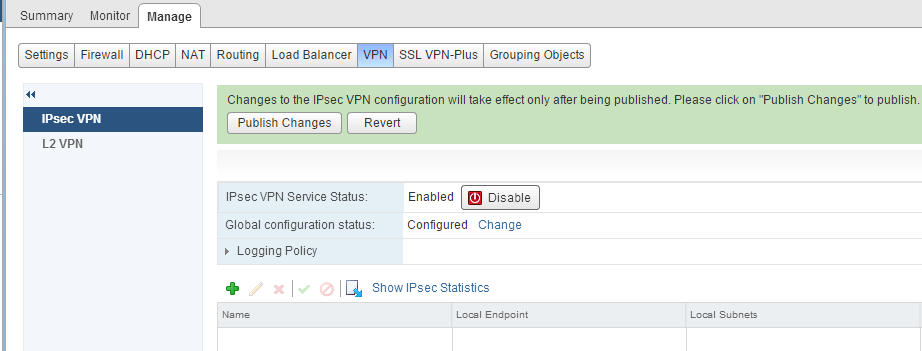
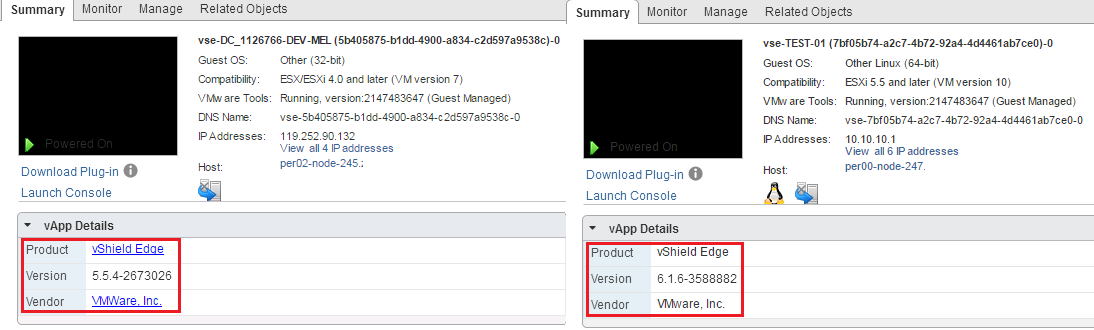
Overview : NSX and vShield Edges support site to site IPSec VPN between Edge instances and remote sites. Behind each remote VPN router, you can configure mul...
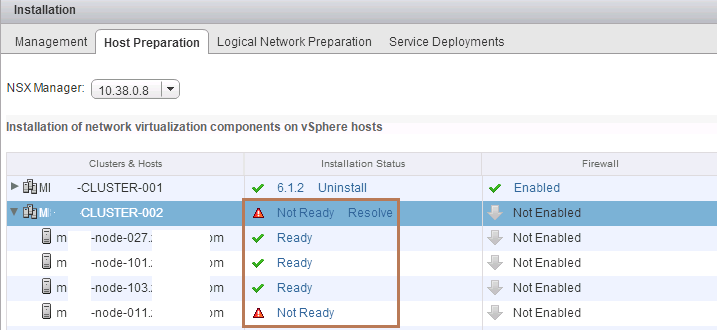
I came across a situation today while going through an NSX Setup and Configuration where I came across a Cluster under the Host Preparation Tab that was repo...