
Happy 10th Birthday VMware Cloud Director!
It is crazy to think that we could celebrate (those of us brave enough to admit it) the birthday of the piece of software. Throughout modern history, softwar...
Tag
38 posts

It is crazy to think that we could celebrate (those of us brave enough to admit it) the birthday of the piece of software. Throughout modern history, softwar...

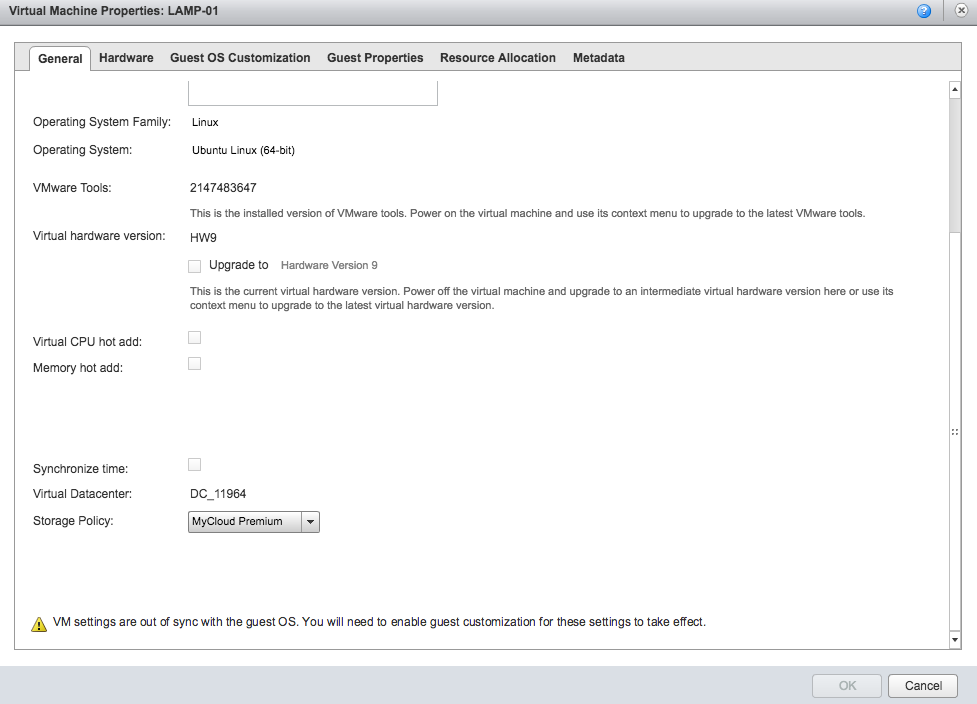
That is probably the longest title i've ever had on this blog, however I wanted to highlight everything that is contained in this solution. Everything above ...
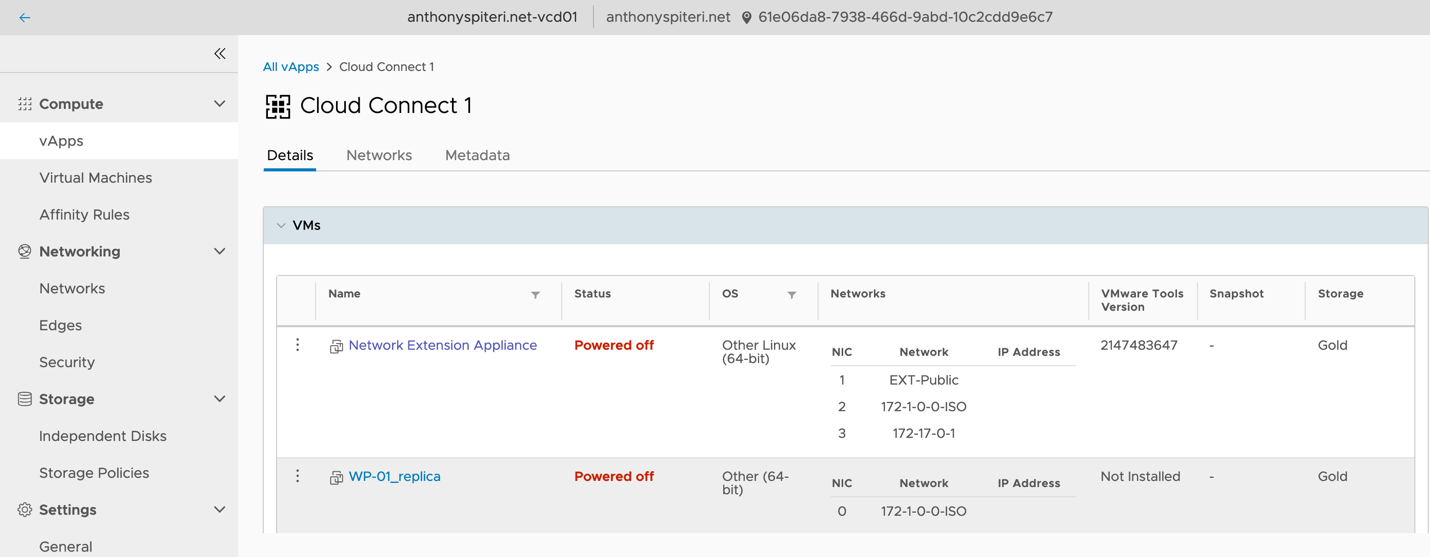
When Veeam Backup & Replication 9.5 Update 4 went Generally Available in late January I posted a What’s in it for Service Providers blog. In that post I brie...
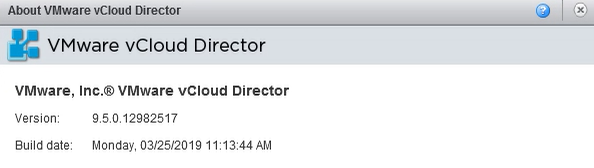
Late last week, on the same day as vCloud Director 9.7 was released to GA, an update was also released for vCloud Director 9.5.x which has been marked are cr...
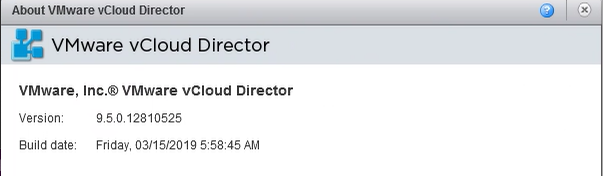
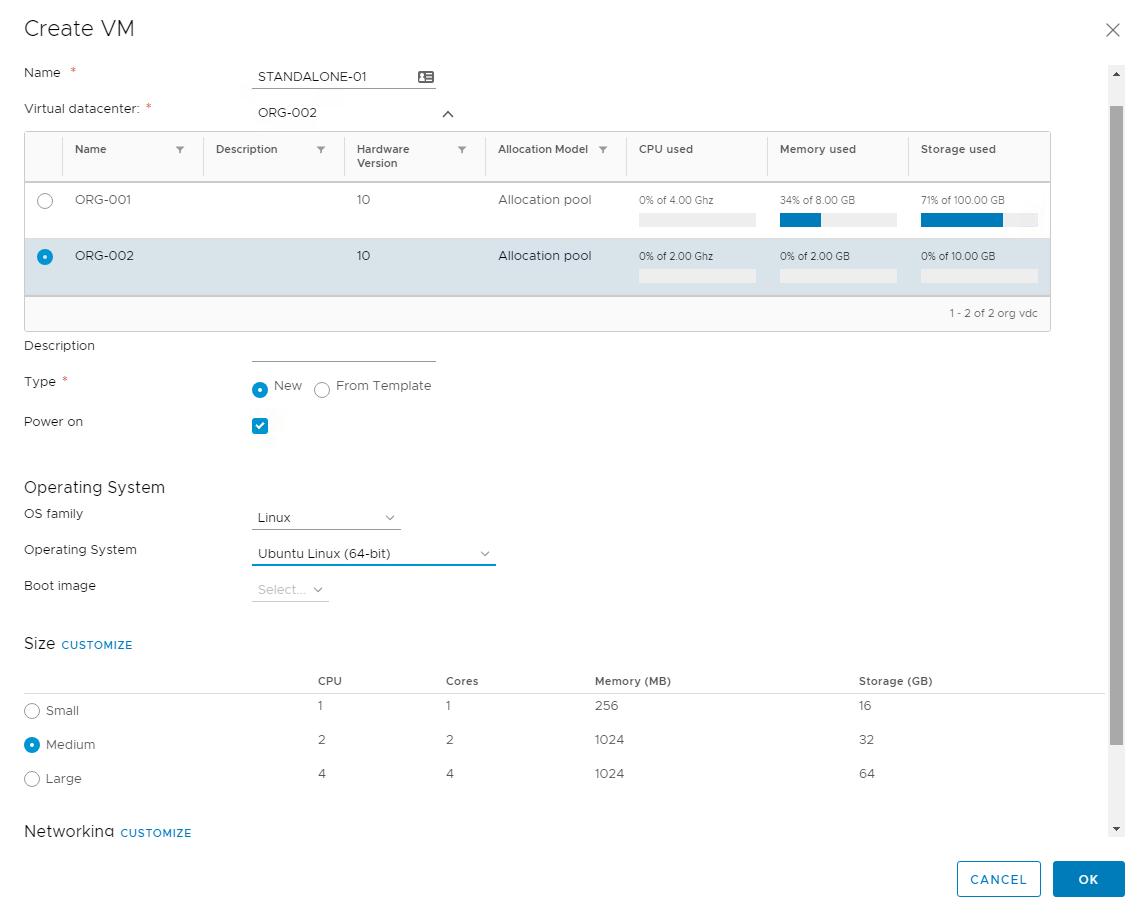
While we wait for the upcoming release of vCloud Director 9.7 next month (after the covers where torn off the next release in a blog post last week by the vC...
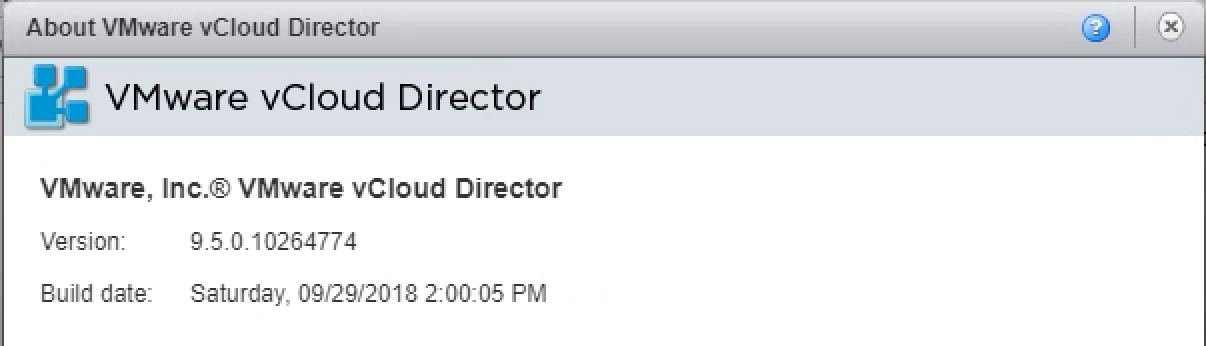
Last week VMware released vCloud Director 9.5 ( build 10266189 ) which builds on the 9.1 release that came out earlier this year . This continues to deliver ...
Back in May when VMware released vCloud Director 9.1 they also depreciated support for a number of older API versions: End of Support for Older vCloud API Ve...
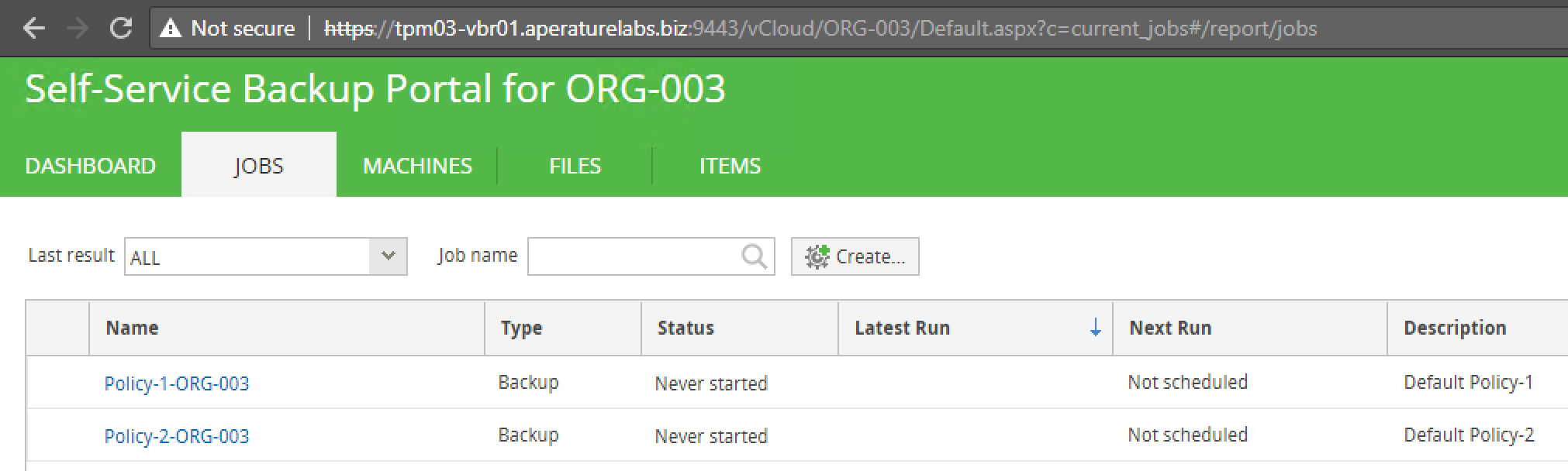
For a long time Veeam has lead the way in regard to the protection of workloads running in vCloud Director. Veeam first released deep integration into vCD ba...
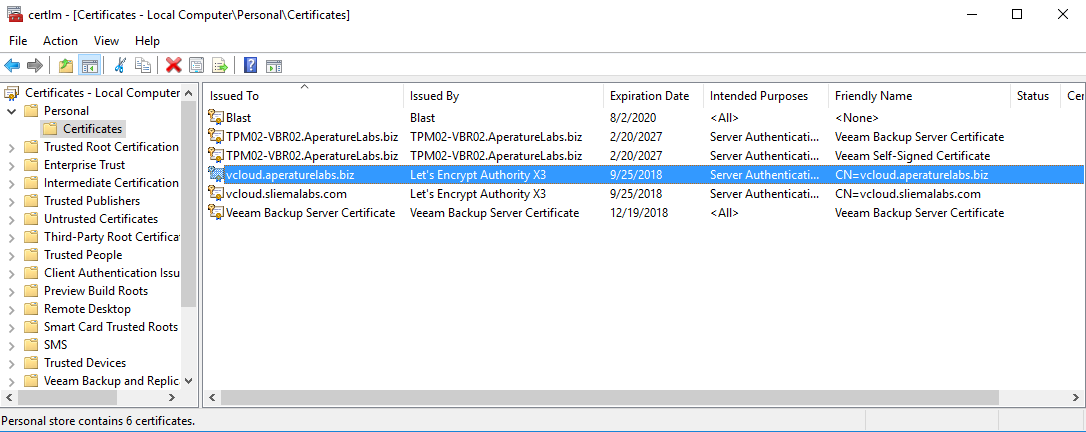
For the longest time the configuring of vCloud Director's SSL certificate keystore has been the thing that makes vCD admins shudder. There are lots of posts ...
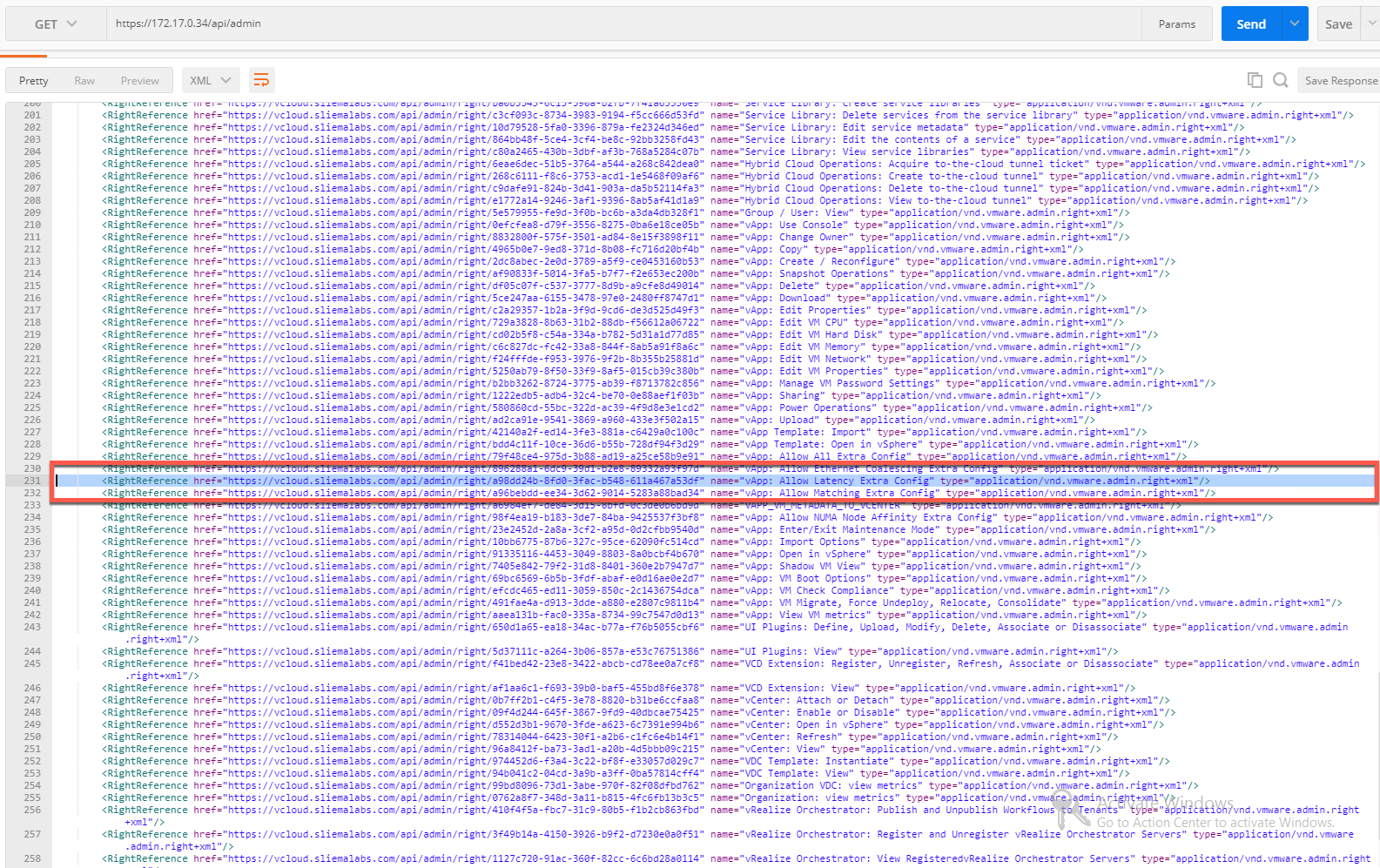
There was a point release of vCloud Director 9.1 ( 9.1.0.1 Build 8825802 ) released last week, bringing with it an updated Java Runtime plus new API function...
Overnight VMware released vCloud Director 9.1 ( build 7905680 ) which builds on the 9.0 release that came out last September. This continues to deliver on VM...
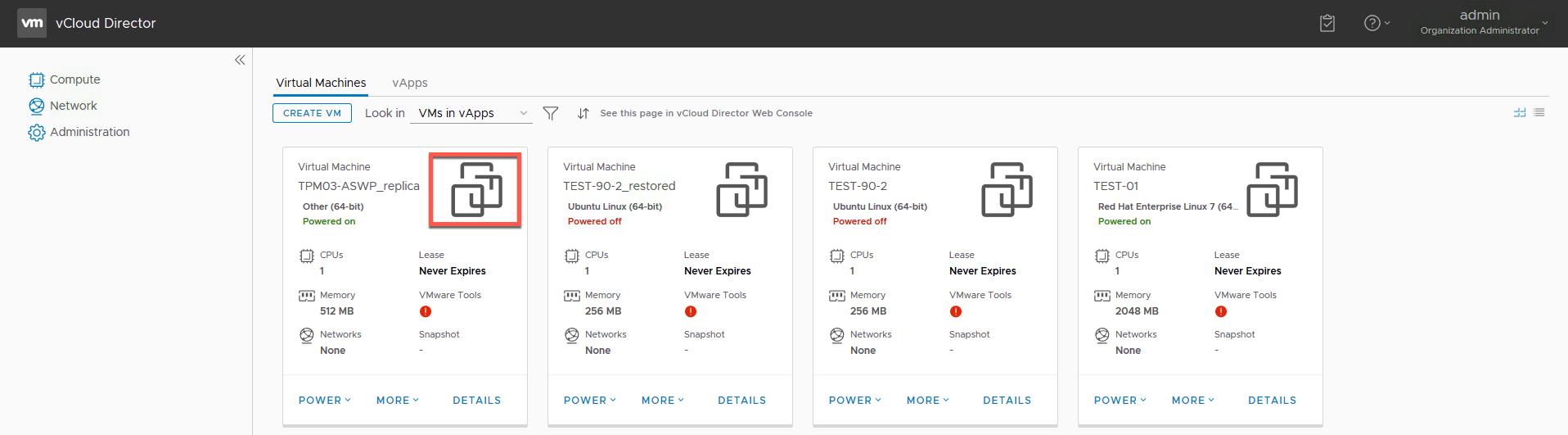
As most of you should know buy now, vCloud Director 9.0 features a new HTML5 Tenant UI Portal which is not only very pretty, but also functional. As of the 9...
Last week VMware put out a new point release for vCloud Director 9.0 ( Build 7553273 ) for Service Providers. While there is nothing new in this release ther...
Last week VMware snuck out two point releases for vCloud Director 8.10 and 8.20. For those still running those versions you now have 8.10.1.1 ( Build 6878548...
vCloud Director 9.0 was released late last month and brought with it a number of big new features and enhancements. If you are interested in a overview of wh...
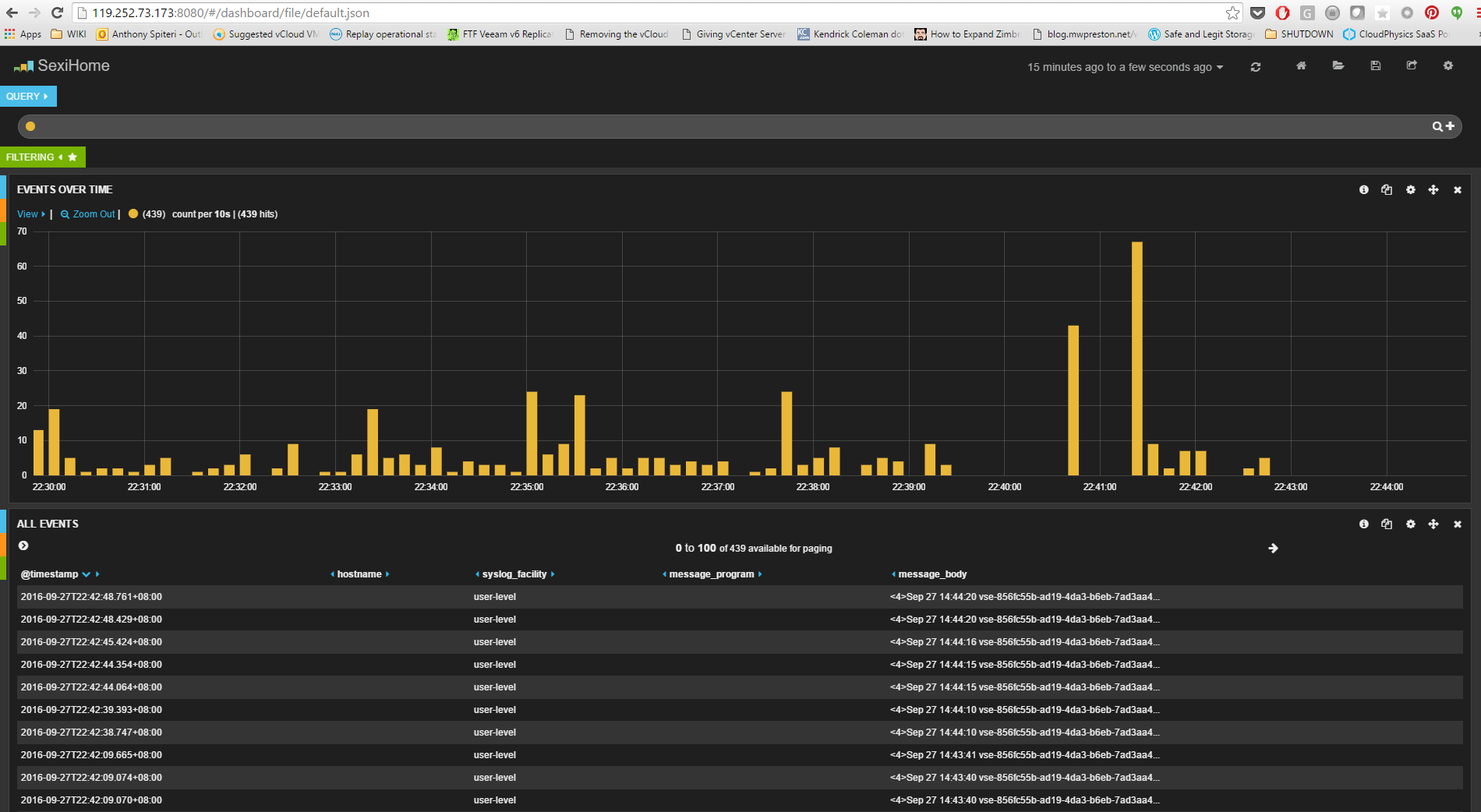
Last week I released a post on configuring Cassandra for vCloud Director 9.0 metrics . As a refresher, one of the cool features released in vCloud Director S...
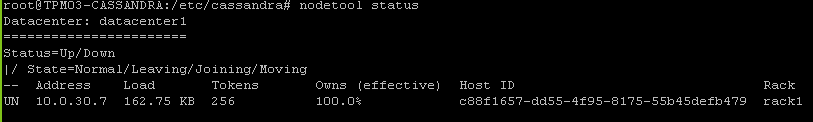
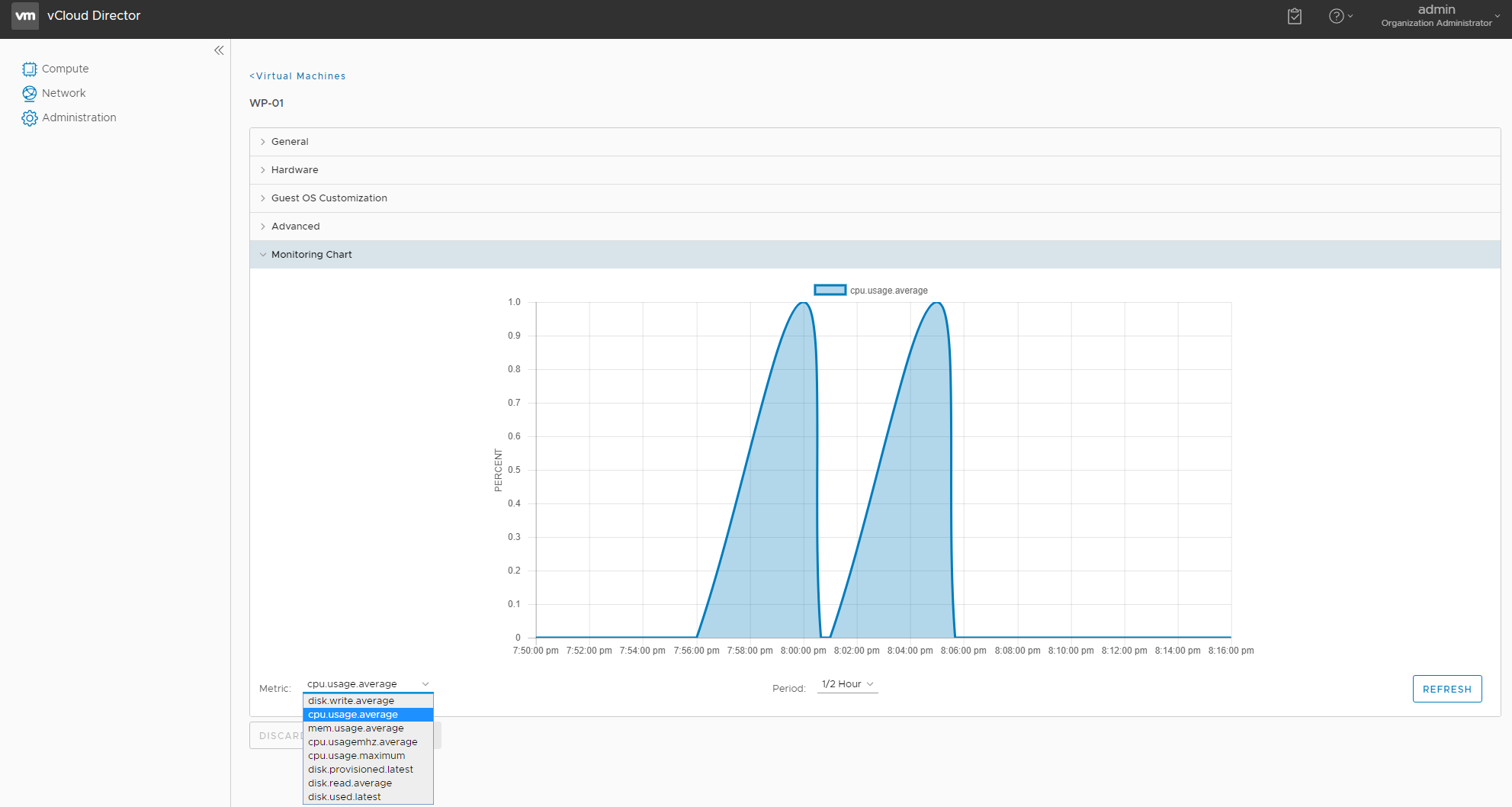
One of the cool features released in vCloud Director SP 5.6.x was the ability to expose VM metrics that service providers could expose to their clients via a...
vCloud Director 9.0, released last week has a bunch of new enhancements and a lot of those are focused around it's integration with NSX. Tom Fojta has a what...
Today is a good day! VMware have released to GA vCloud Director 9.0 ( build 6681978 ) and with it come the most significant feature and enhancements of any p...
Today at VeeamON 2017 we announced two very important enhancements to our DRaaS capabilities around Cloud Connect Replication and Tape Backup for our Veeam C...
It seems that with the announcement last week that VMware was offloading vCloud Air to OVH people where again asking what is happening with vCloud Director.....
Many, including myself thought that the day would never come where we would be talking about a new UI for vCloud Director...but a a month on from the 8.20 re...
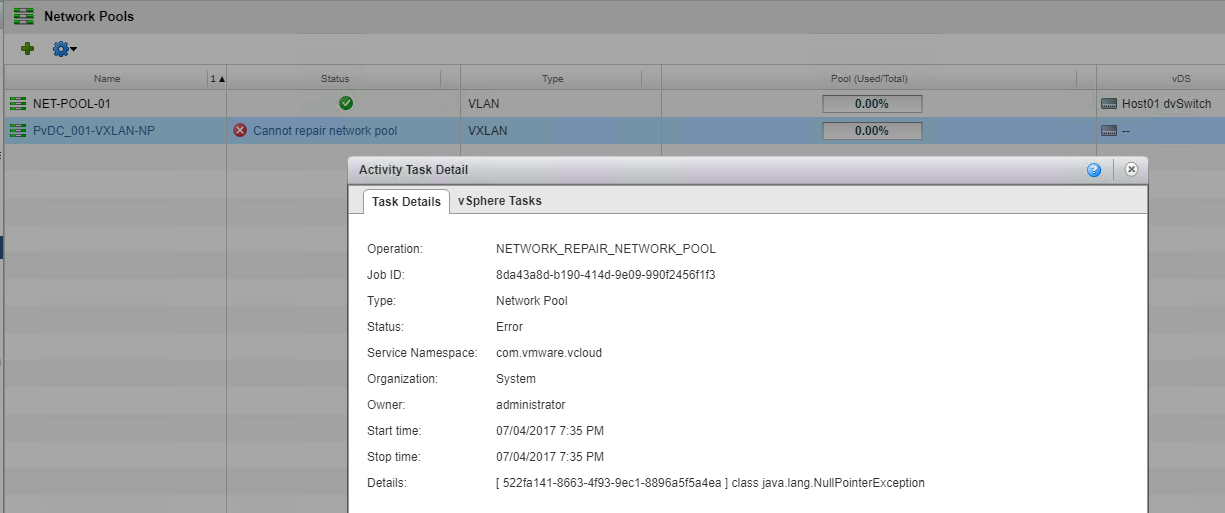
vCloud Director SP 8.20 was released a few weeks ago and I wanted to highlight an issue I ran into while testing of the BETA. I hadn't come across this issue...
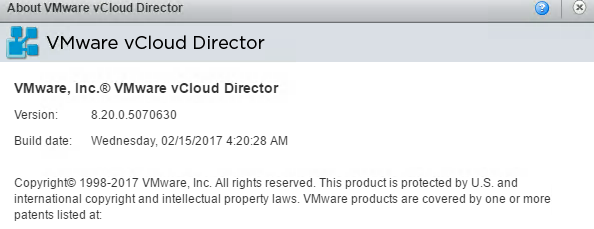
This week, VMware released vCloud Director SP version 8.20 ( build 5070630 ) which marks the 8th Major Release for vCloud Director since 1.0 was released in ...

Welcome to 2017! To kick off the year I thought I'd do a quick post on a little known product (at least in my circles) from Red Hat Inc called ManageIQ . I s...
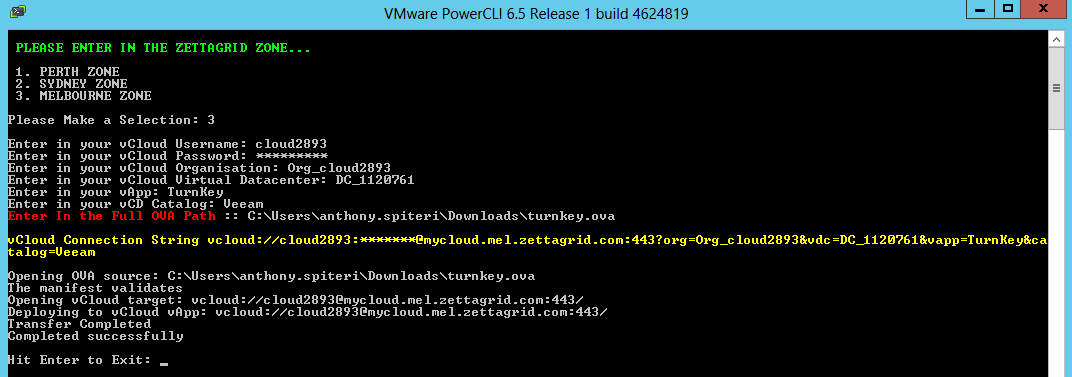
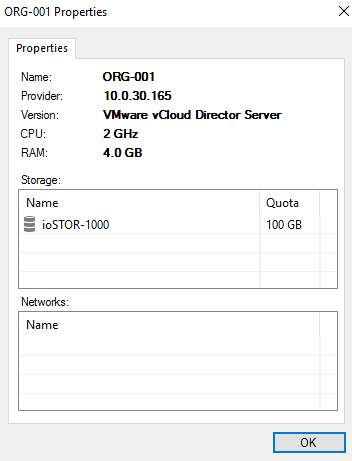
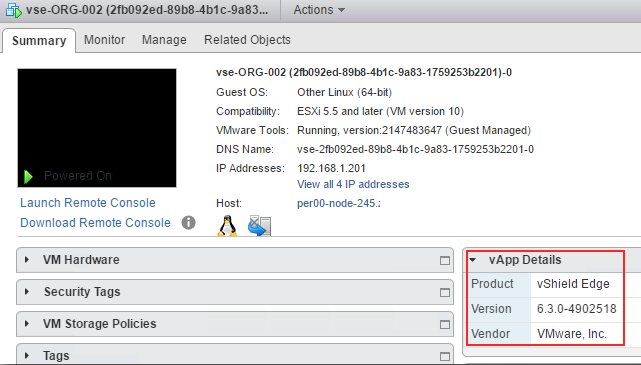
Earlier this year I put together a quick and nasty PowerShell Script that exports a vApp from vCloud Director using the OVFTool ...for those that don't know ...
Last week VMware released vCloud Director SP 8.10.1 Build 4655197 and while it was mainly a patch release there was one new feature added which was a couple ...
This week VMware released vCloud Director SP 8.10.1 Build 4655197 . This is the sister build for vCD SP 8.0.2 and like that release, while there a a number o...

Last week VMware and Amazon Web Services officially announced their new joint venture whereby VMware technology will be available to run as a service on AWS ...

Last week VMware and Amazon Web Services officially announced their new joint venture whereby VMware technology will be available to run as a service on AWS ...
Last week VMware released vCloud Director SP 8.0.2 Build 4348775 . While there a a number of minor bug fixes in this release there is one important fix that ...
There is a lot of talk going around how IT Pros can more efficiently operate and consume Cloud Based Services…AWS has lead the way in offering a rich set of ...

Over the weekend I was tasked with the recovery of a #NestedESXi lab that had vCloud Director and NSX-v components as part of the lab platform. Rather than b...
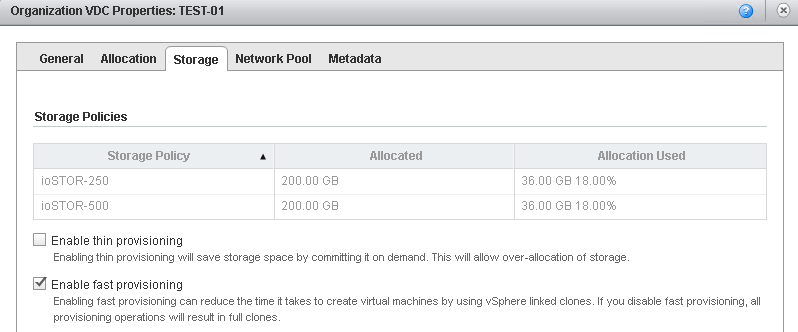
vCloud Director SP 8.10 has been out for a couple months now and the general buzz around this release has been extremely positive. The decision to expose the...
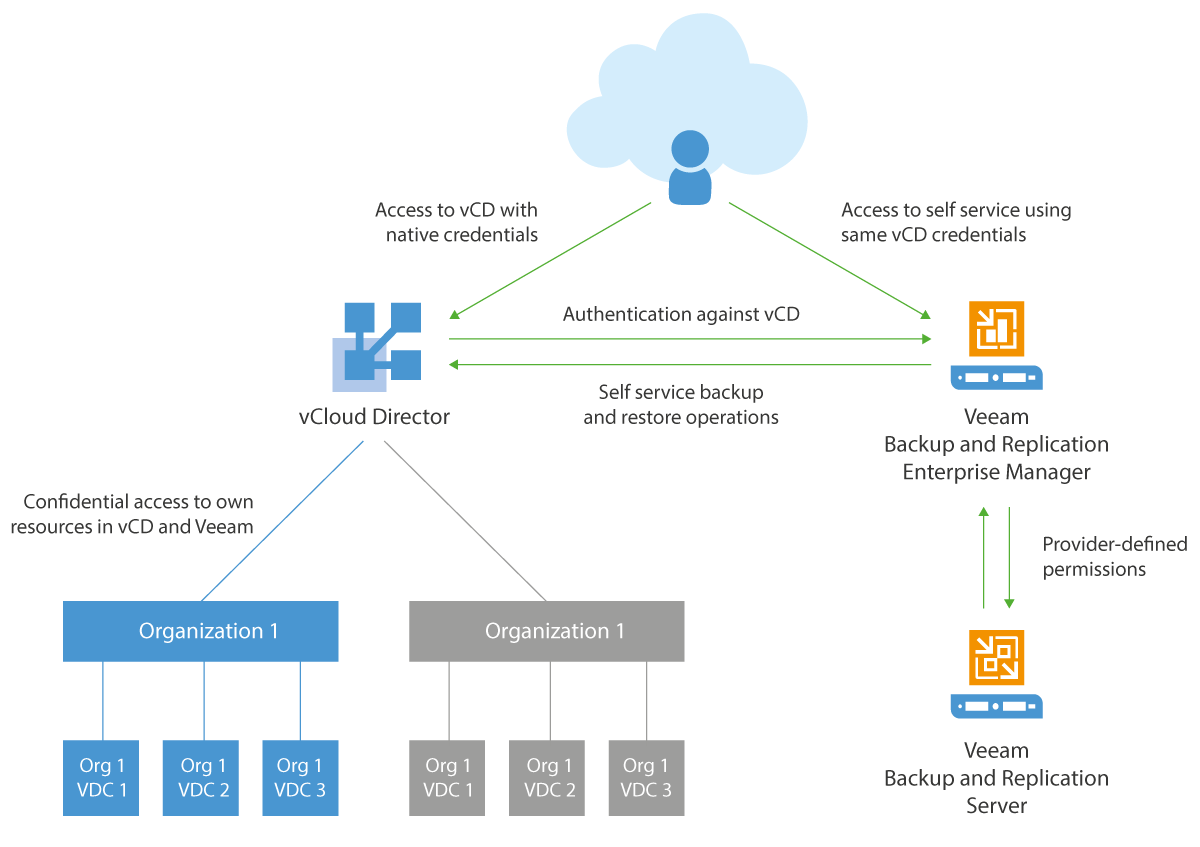
Veeam have only announced two features of their upcoming v9.5 release of Backup & Replication but it's exciting to announce that they have chosen to release ...
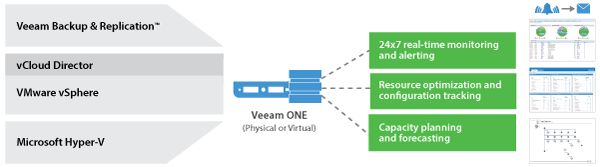
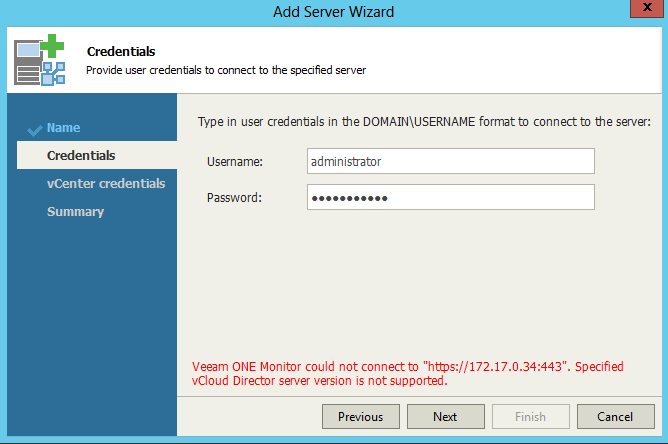
Veeam don't just do awesome Backup & Replication software ...they also have, what I think is a highly underrated operations and management and capacity plann...
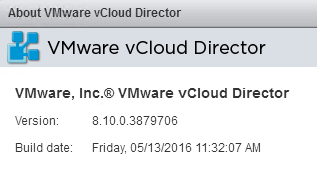
Earlier this morning VMware released vCloud Director SP 8.10 Build 3879706 . This is a significant release for vCloud Director as its the first release that ...
Last week VMware released advisory VMSA-2016-0004 for a critical security issue found in the Client Integration Plugin which is found in versions of vCenter,...