
Verge.io - A New Wave of Hyper-Converged Virtualization
There is no doubt we are moving into a new era of infrastructure to host applications and workloads on. And as organisations start to move back to on-premise...
Tag
24 posts

There is no doubt we are moving into a new era of infrastructure to host applications and workloads on. And as organisations start to move back to on-premise...

I remember back a few years ago when VMware first launched their Flings how useful some of them where (and still are). Seemed like no matter what area of the...
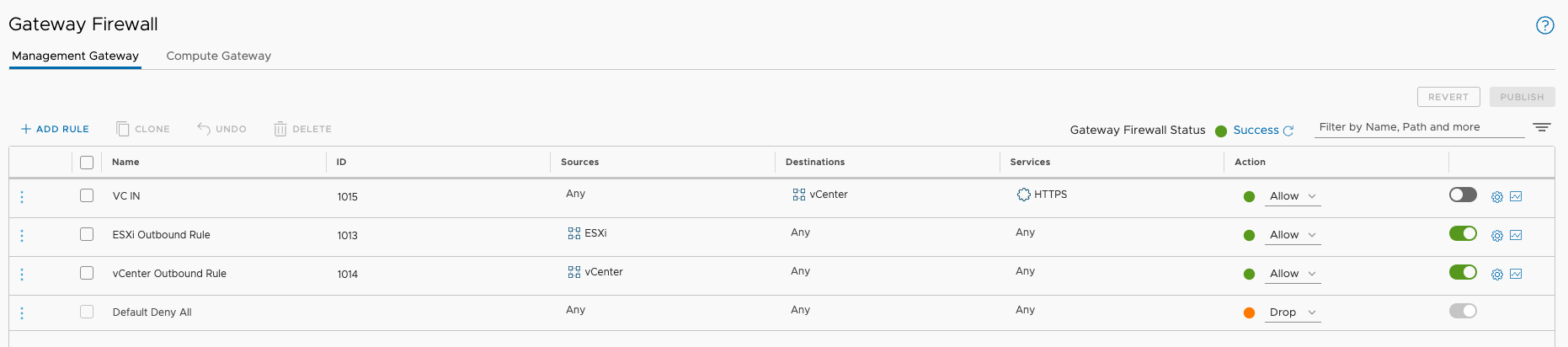
Over the past week or so, i've been diving back into working on VMware Cloud on AWS ... for the most, the experience hasn't changed that much since I started...

One of the things I wanted to do this year was get back into technologies, applications, platforms or solutions that I have drifted away from over recent yea...
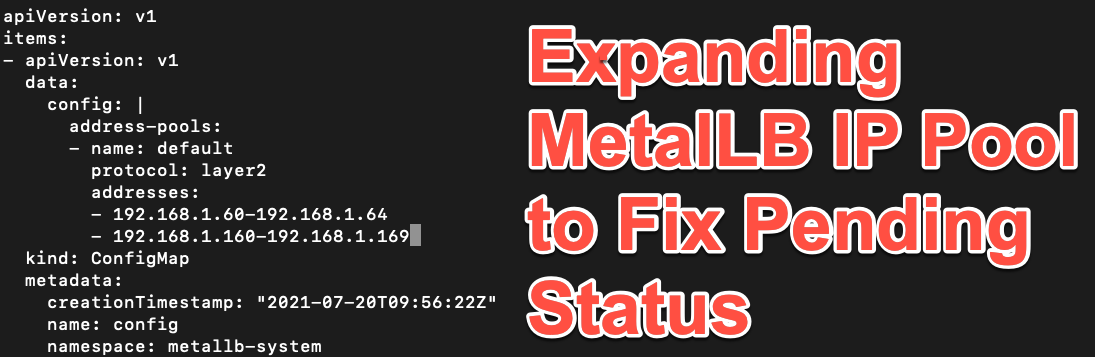
I've been using MetalLB for a while now in my Kubernetes Clusters and it's a great easy way to achieve high availability networking for service endpoints. Fo...
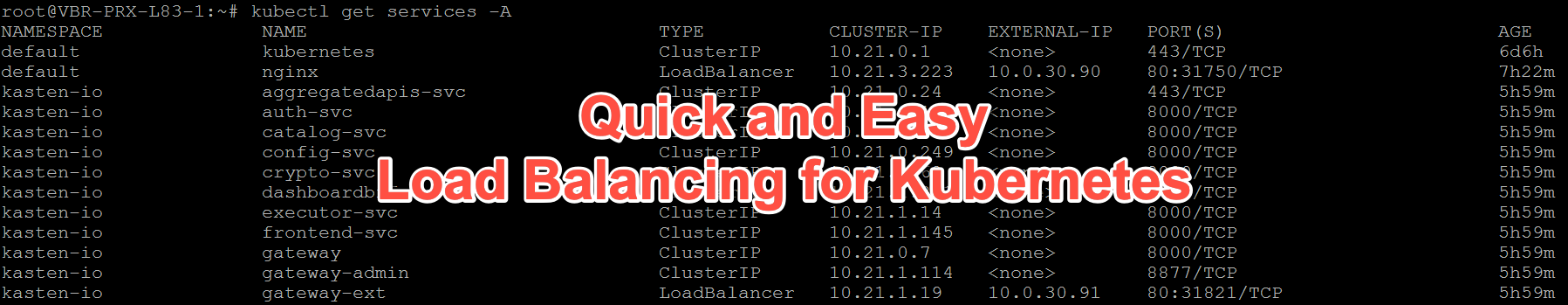
I've been tinkering with a number of different Kubernetes platforms again and the relative complication of external networking for deployed Kubernetes applic...
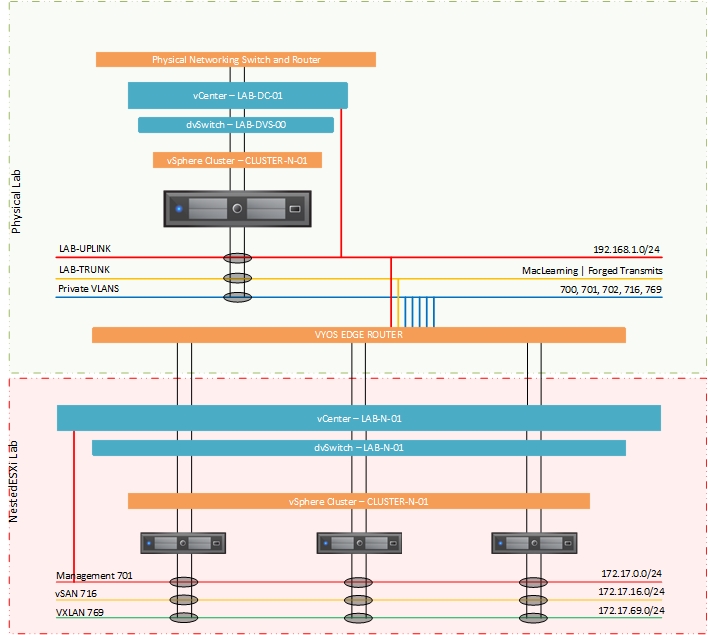
Back for part two of this look at how I went about configuring a single host for NestedESXi deployments. In the previous post I looks at the physical configu...
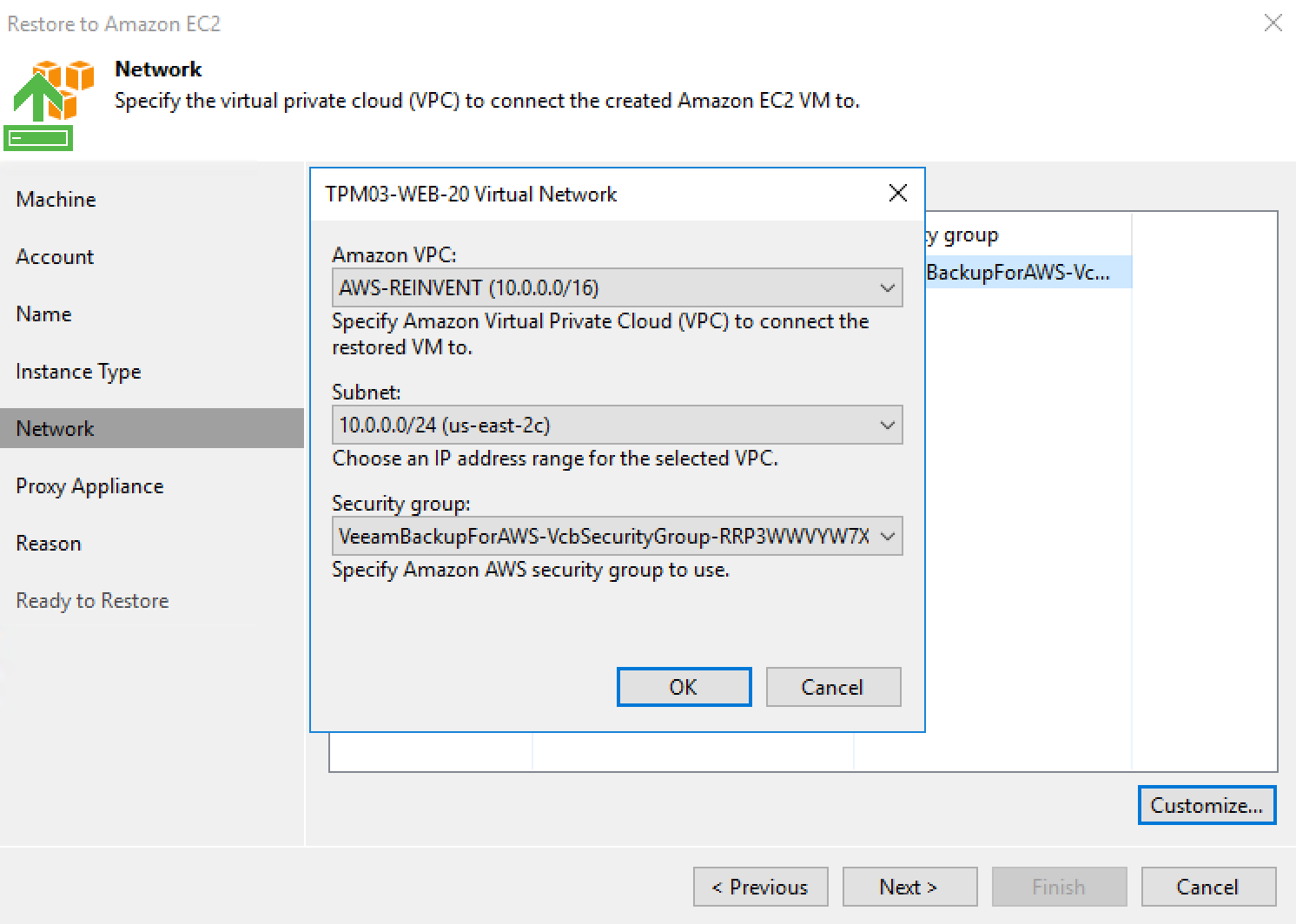
Version 10 of Veeam Backup & Replication isn't too far away and we are currently at the end of a second private BETA for our customers and partners. There ha...
I had a really strange situation pop up in one of my lab environments over the weekend. vSAN Health was reporting that one of the hosts had lost networking c...

When it comes to connecting remote sites, branch offices or extending on-premises networks to the cloud that level of complexity has traditionally always bee...

For those that have been monitoring my Twitter posts over the past month of so, i've been hinting at some upcoming news around WireGuard and the research i'v...
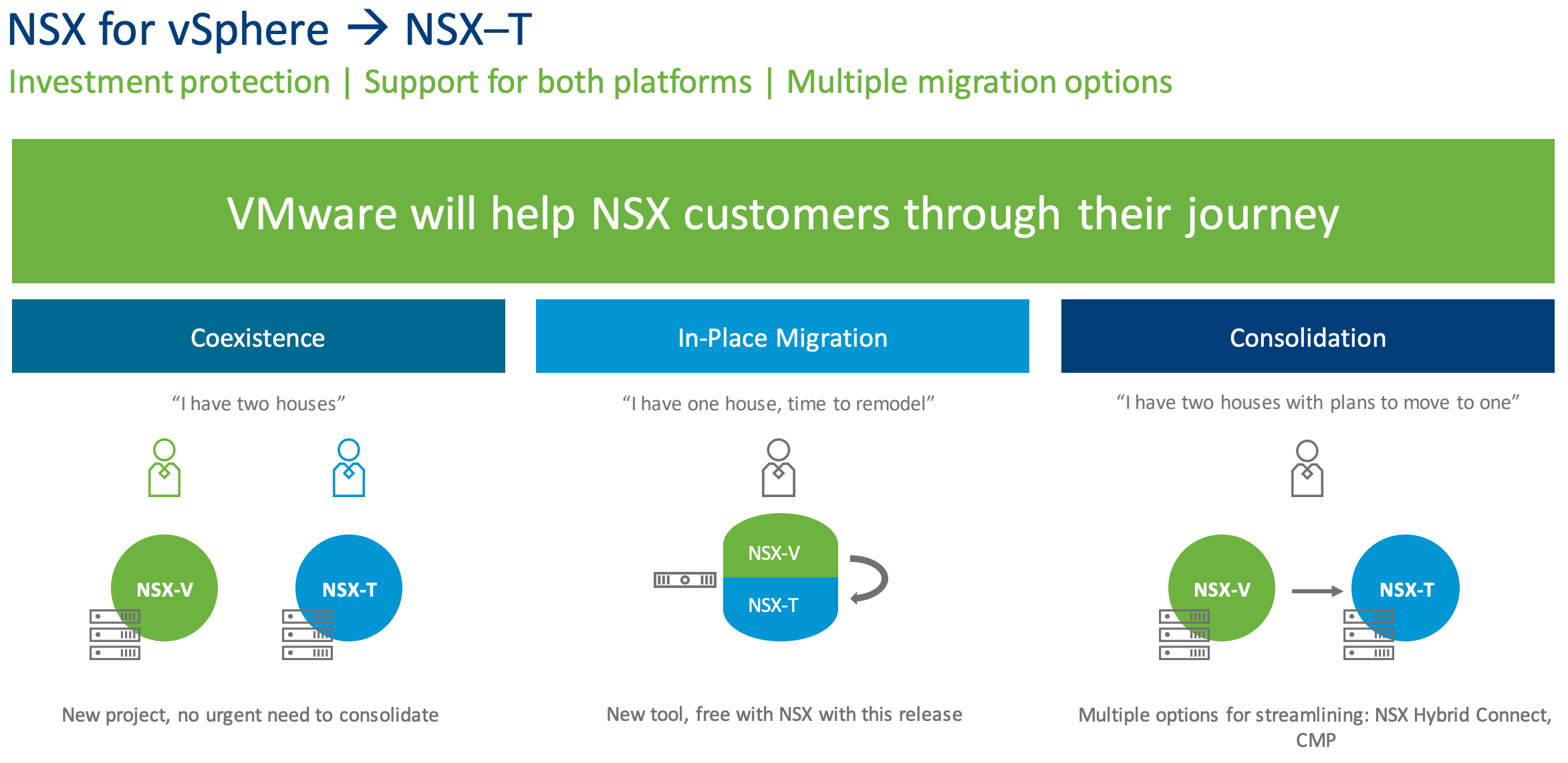
A little over two years ago in Feburary of 2017 VMware released NSX-T 2.0 and with it came a variety of updates that looked to continue to push NSX-T beyond ...
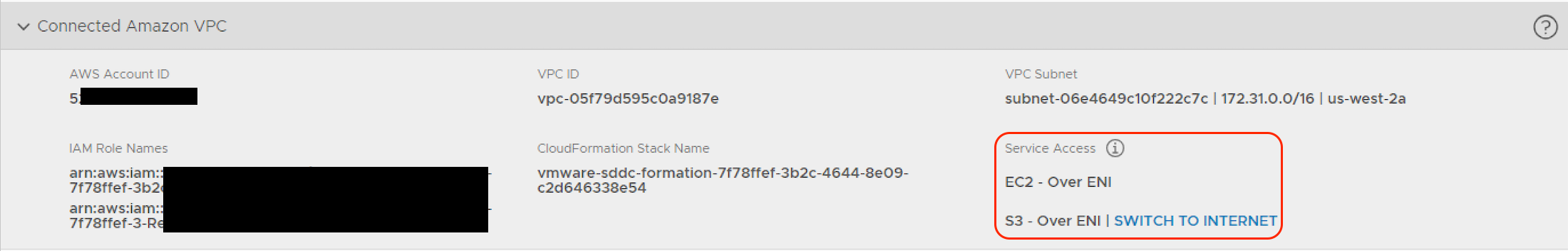
When looking at how to configure networking for interactions between a VMware Cloud on AWS SDDC and an Amazon VPC there is a little bit to grasp in terms of ...
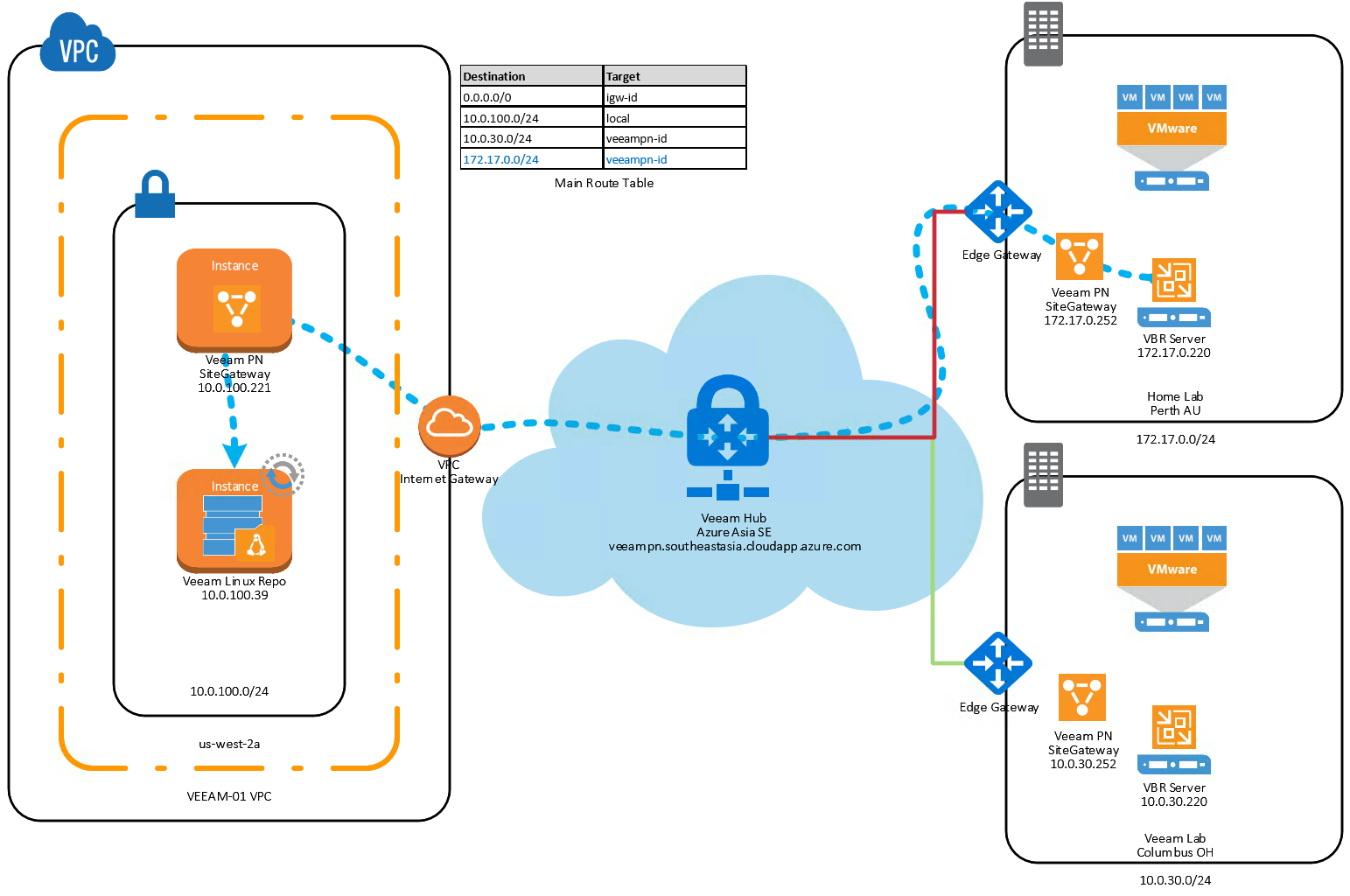
Veeam PN is a very cool product that has been GA for about four months now. Initially we combined the free product together with Veeam Direct Restore to Micr...

This week VMware released NSX-v 6.4.0 ( Build 7564187 ) and with it comes a new UI Plug-in for vSphere Client (HTML5) which includes some new dashboards incl...
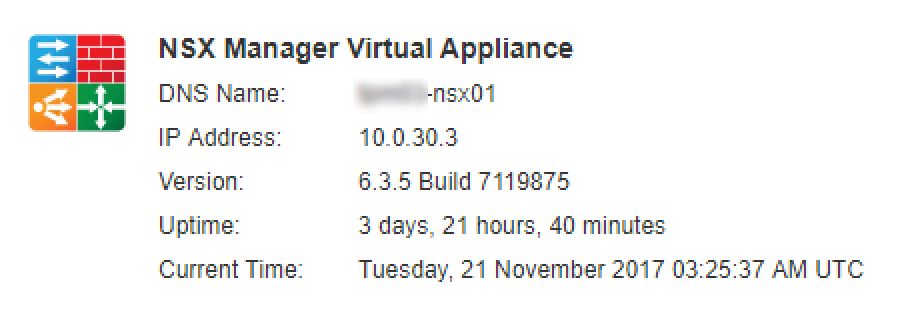
Last week VMware released NSX-v 6.3.5 ( Build 7119875 ) that contains a few new features and addresses a number of bug fixes from previous releases. Going th...
Earlier this year at VeeamON we announced Veeam PN as part of the Restore to Microsoft Azure product. While Veeam PN is still in RC, I've written a series of...

Last week VMware released NSX-v 6.3.3 ( Build 6276725 ) and with it comes a new operating system for the NSX Controllers. Once upgraded the new controllers w...
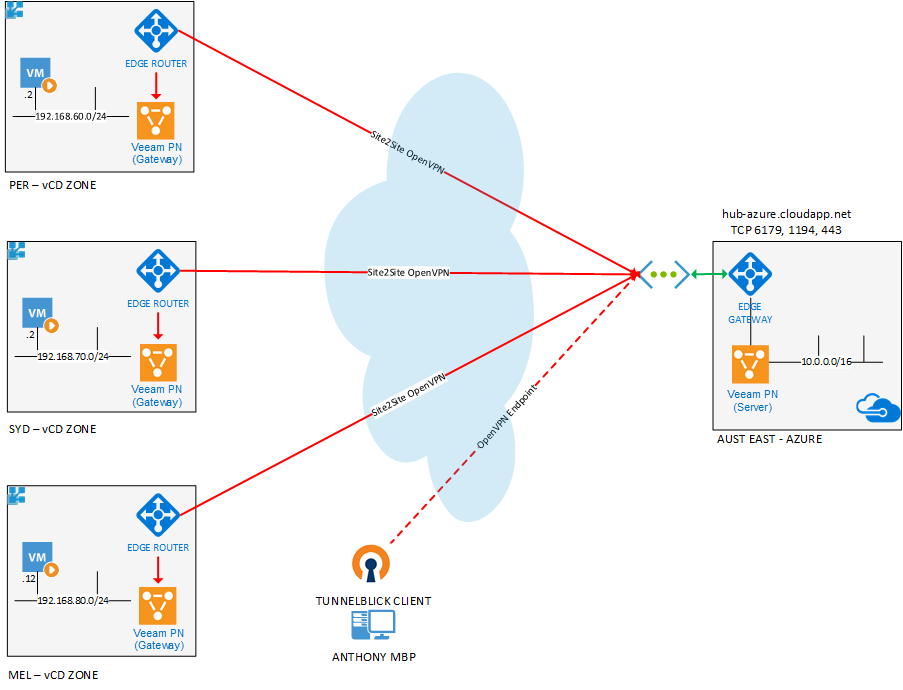
I've written a couple of posts on how Veeam Powered Network can make accessing your homelab easy with it's straight forward approach to creating and connecti...
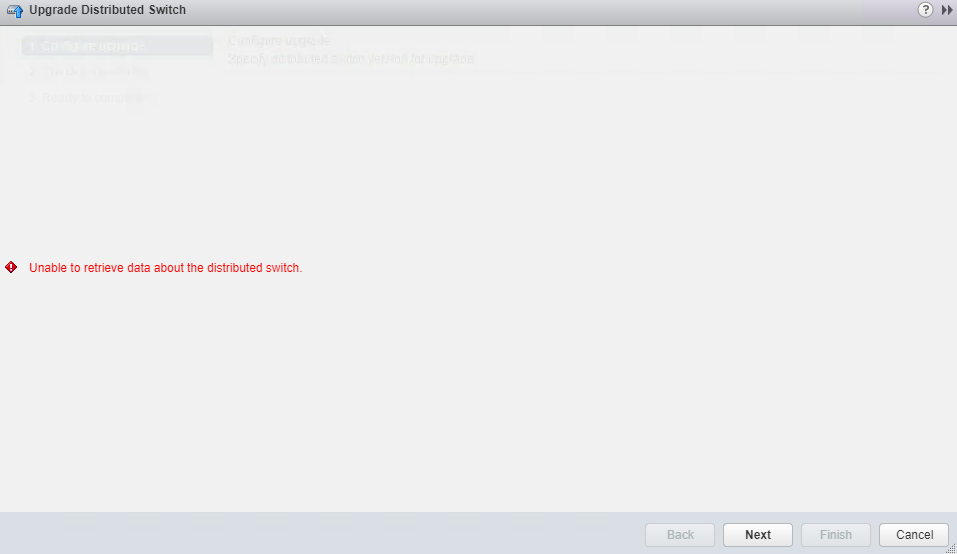
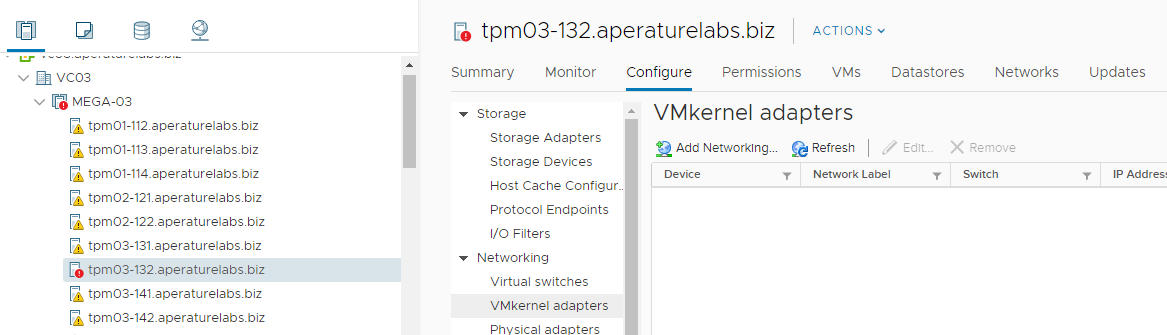
This week I upgraded (and migrated) my SliemaLabs NestedESXi vCenter from a Windows 6.0 server to a 6.5 VCSA ...everything went well, but ran into an issue w...

A few weeks ago I wrote an article on how Veeam Powered Network can make accessing your homelab easy with it's straight forward approach to creating and conn...
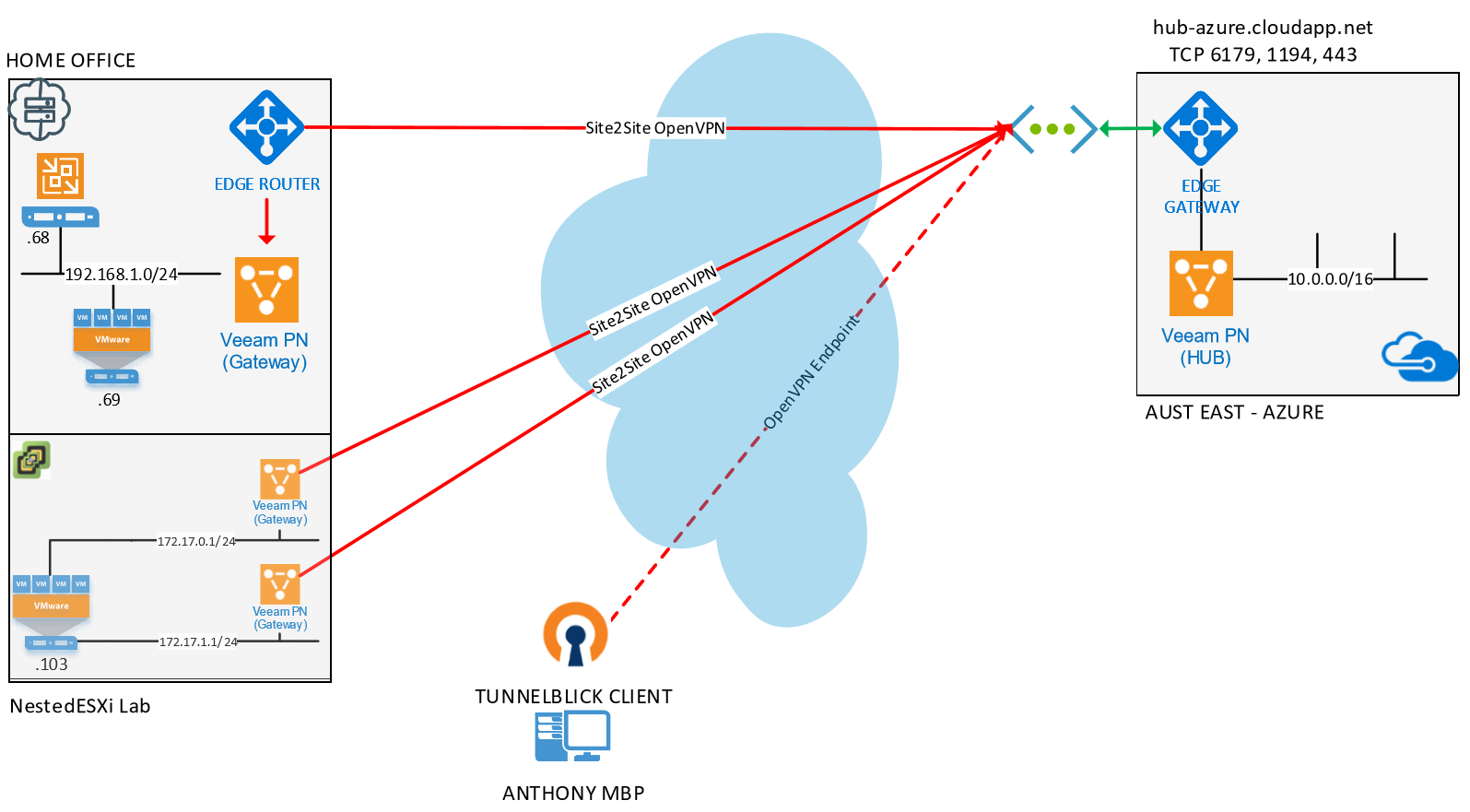
A couple of weeks ago at VeeamON we announced the RC of Veeam PN which is a lightweight SDN appliance that has been released for free . While the main messag...
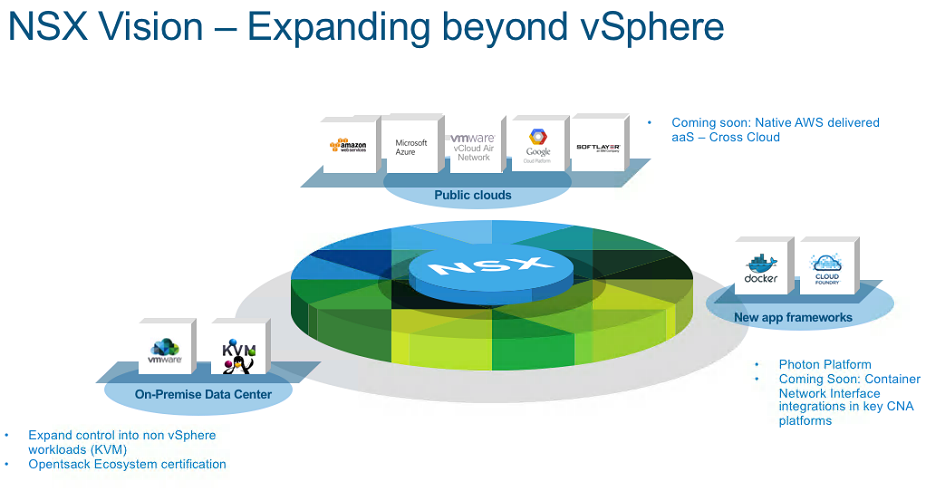
A couple of months ago in my NSX-v 6.3 and NSX-T 1.1 release post I focused around NSX-v features as that has become the mainstream version that most people ...
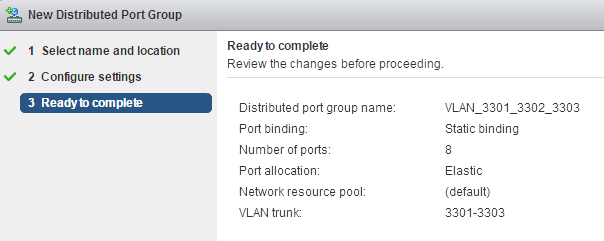
This week one of our Vitualisation Engineer's ( James Smith ) was trying to come up with a solution for a client that wanted the flexibility to bring in his ...