
v11 For Service Providers - Replication for VMware Cloud Director
When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...
Tag
86 posts

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...

It is crazy to think that we could celebrate (those of us brave enough to admit it) the birthday of the piece of software. Throughout modern history, softwar...
Over the weekend, we released the v10a ( Build 10.0.1.4854 ) release of our flagship product, Veeam Backup & Replication. This is the first major update to v...

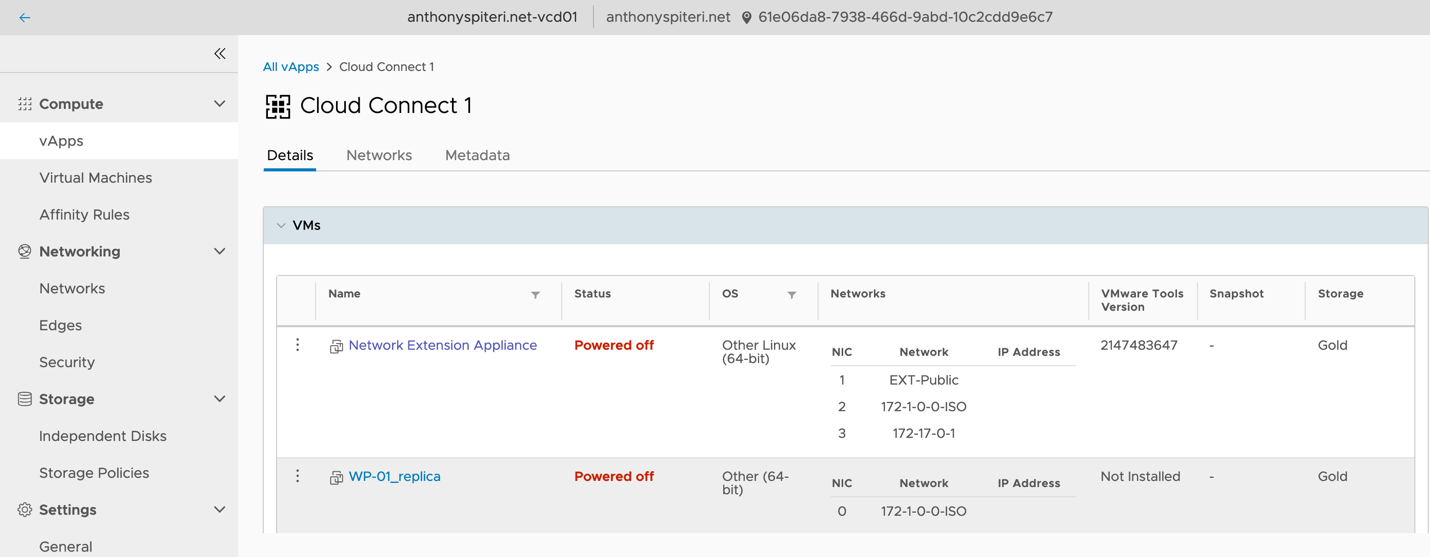
One of the early benefits of being part fo the vExpert Cloud Provider subprogram, was that we where given a chance to get a first look and use of Cloud Direc...

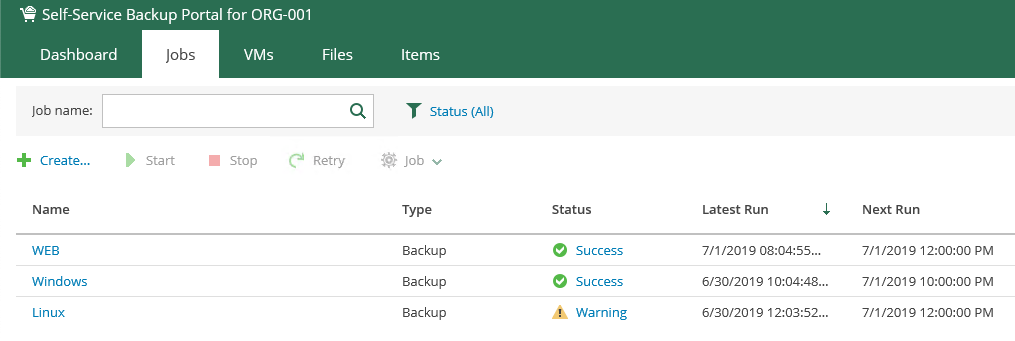
Veeam Backup & Replication v10 has been Generally Available since mid Feburary and last week I posted a What’s in it for Service Providers overview blog post...
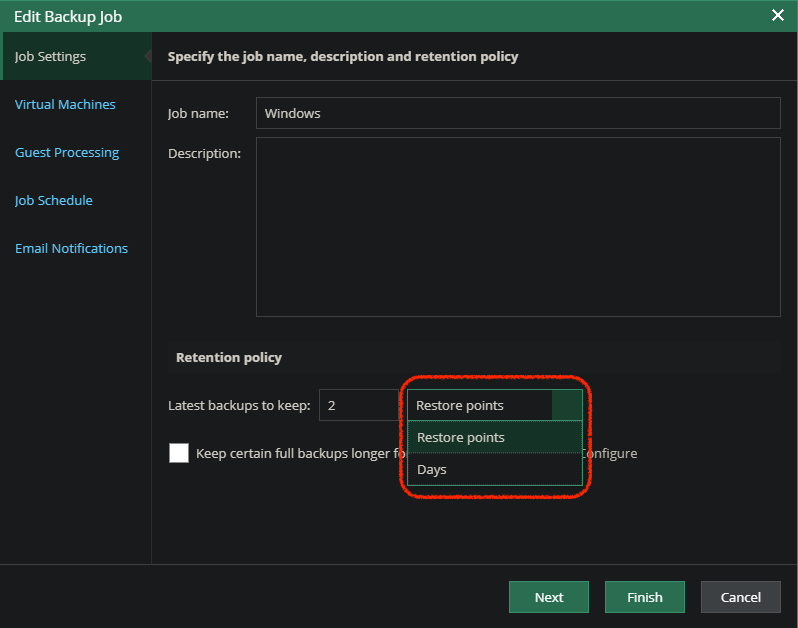
Version 10 of Veeam Backup & Replication right around the corner as we rapidly approach GA. The RTM has been out for our service provider partners for a coup...
![vCloud Director is no more... Long Live vCD! [VMware Cloud Director Service for VMC]](https://i1.wp.com/anthonyspiteri.net/wp-content/uploads/2016/10/VMWonAWSvCD2.png?fit=1038%2C416&ssl=1)
There was a very significant announcement at VMworld Barcelona overnight, with the unveiling of a new service targeted at Managed Service Providers. VMware C...
Since version 7 of Backup & Replication , Veeam has lead the way in regard to the protection of workloads running in vCloud Director. With version 7 Veeam fi...
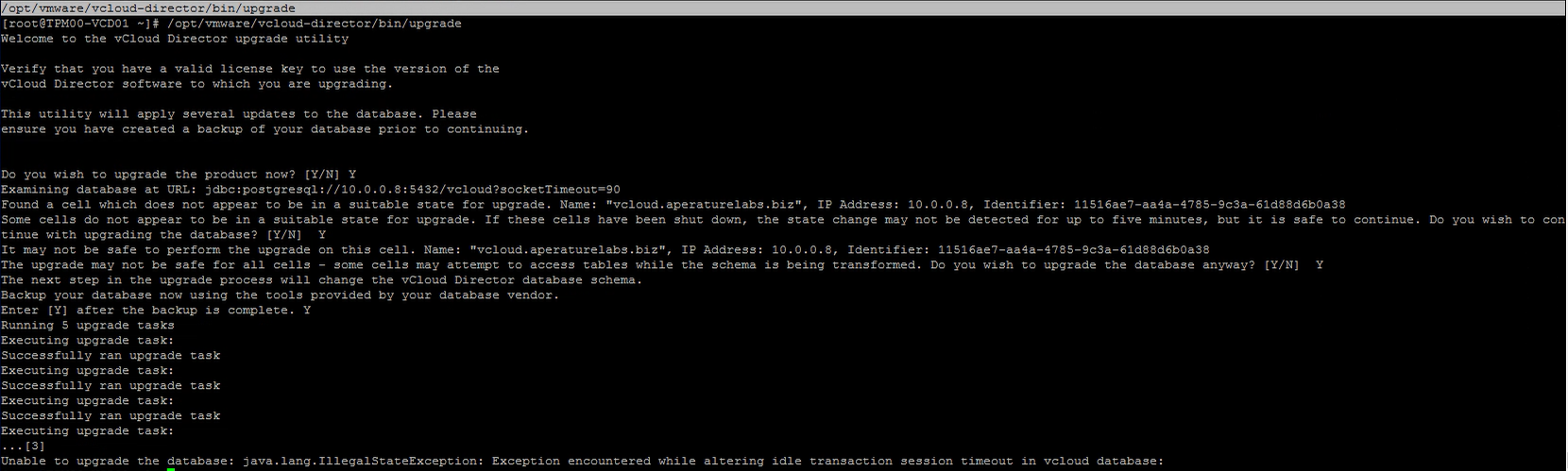
While looking to upgrade one of my vCloud Director instances I came across an error during the database upgrade process which is the second step of updating ...
When Veeam Backup & Replication 9.5 Update 4 went Generally Available in late January I posted a What’s in it for Service Providers blog. In that post I brie...
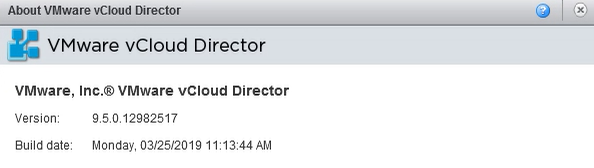
Late last week, on the same day as vCloud Director 9.7 was released to GA, an update was also released for vCloud Director 9.5.x which has been marked are cr...
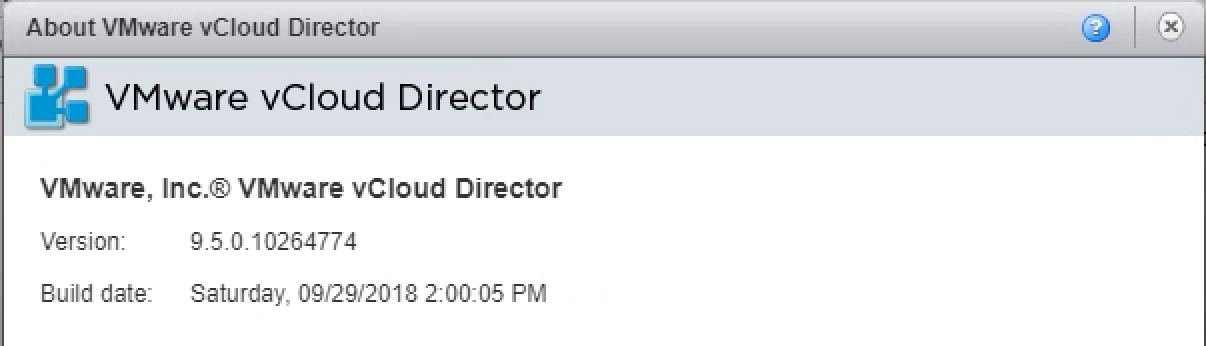
Last week VMware released vCloud Director 9.5 ( build 10266189 ) which builds on the 9.1 release that came out earlier this year . This continues to deliver ...
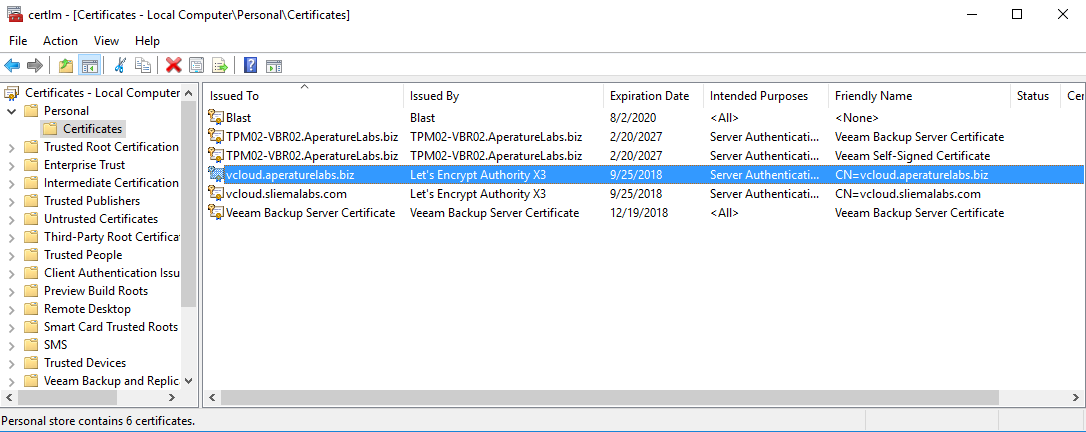
For the longest time the configuring of vCloud Director's SSL certificate keystore has been the thing that makes vCD admins shudder. There are lots of posts ...
As most of you should know buy now, vCloud Director 9.0 features a new HTML5 Tenant UI Portal which is not only very pretty, but also functional. As of the 9...

Last week Corey Romero announced the inaugural members of the vExpert Cloud sub-program . This is the third vExpert sub-program following the vSAN and NSX pr...
vCloud Director 9.0 was released late last month and brought with it a number of big new features and enhancements. If you are interested in a overview of wh...
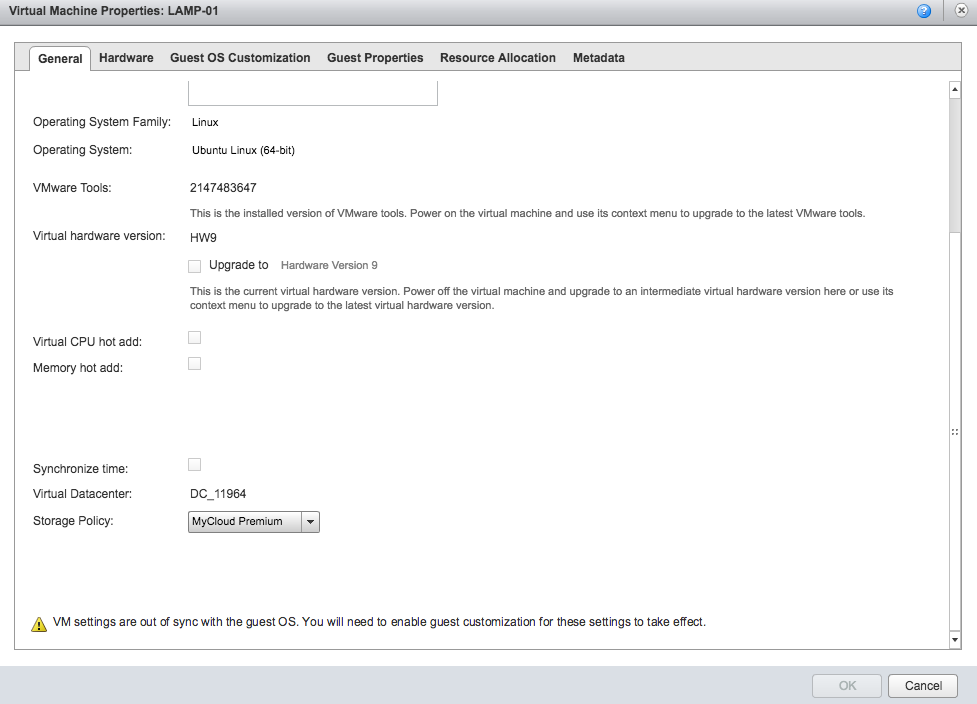
One of the cool features released in vCloud Director SP 5.6.x was the ability to expose VM metrics that service providers could expose to their clients via a...

Last year saw a resurgence in vCloud related sessions at VMworld and the trend has continued this year at the 2017 event. Looking through the sessions at Par...
Today at VeeamON 2017 we announced two very important enhancements to our DRaaS capabilities around Cloud Connect Replication and Tape Backup for our Veeam C...
It seems that with the announcement last week that VMware was offloading vCloud Air to OVH people where again asking what is happening with vCloud Director.....
vCloud Director SP 8.20 was released a few weeks ago and I wanted to highlight an issue I ran into while testing of the BETA. I hadn't come across this issue...

Welcome to 2017! To kick off the year I thought I'd do a quick post on a little known product (at least in my circles) from Red Hat Inc called ManageIQ . I s...
Last week VMware released vCloud Director SP 8.10.1 Build 4655197 and while it was mainly a patch release there was one new feature added which was a couple ...

Since Backup and Replication 7 Veeam have continued to develop new features in enhancements to support their Cloud and Service Provider community. This start...
This week VMware released vCloud Director SP 8.10.1 Build 4655197 . This is the sister build for vCD SP 8.0.2 and like that release, while there a a number o...
It seems that all with all the announcements of late around VMware's (re)shifting Hybrid Cloud strategy with Cross Cloud Foundation and VMware's partnership ...

Last week VMware and Amazon Web Services officially announced their new joint venture whereby VMware technology will be available to run as a service on AWS ...
Last week VMware released vCloud Director SP 8.0.2 Build 4348775 . While there a a number of minor bug fixes in this release there is one important fix that ...

VMworld Europe is a little over a week away and while I won't be attending the even in Barcelona in looking through the session catalog for Partner Exchange ...
I'm still trying to process the VMworld 2016 Day 1 Keynote in my mind...trying to make sense of the mixed messages that myself and others took away from the ...

VMworld 2016 is just around the corner (10 days and counting) and the theme this year is be_Tomorrow …which looks to build on the Ready for Any and Brave IT ...
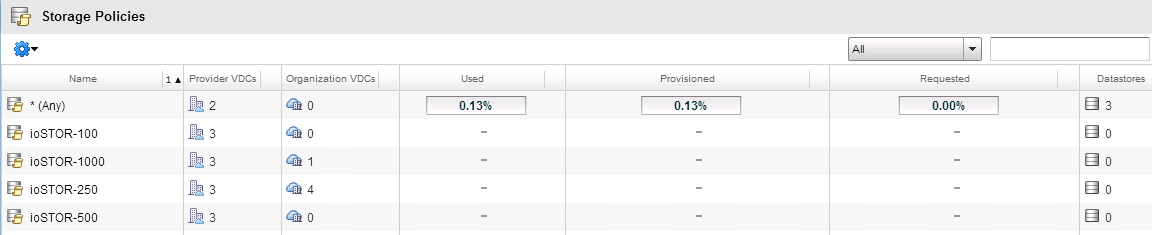
vCloud Director SP 8.10 has been out for a couple months now and the general buzz around this release has been extremely positive. The decision to expose the...

VMworld is a little over three weeks away and from the looking through the sessions at Partner Exchange and VMworld proper the refocus on the vCloud Air Netw...
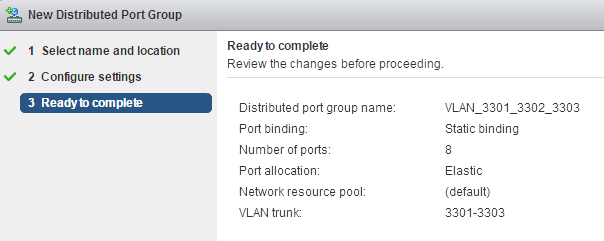
This week one of our Vitualisation Engineer's ( James Smith ) was trying to come up with a solution for a client that wanted the flexibility to bring in his ...
vCloud Director SP 8.10 has been out for about a month now and the general buzz around this release has been extremely positive. The decision to expose the p...
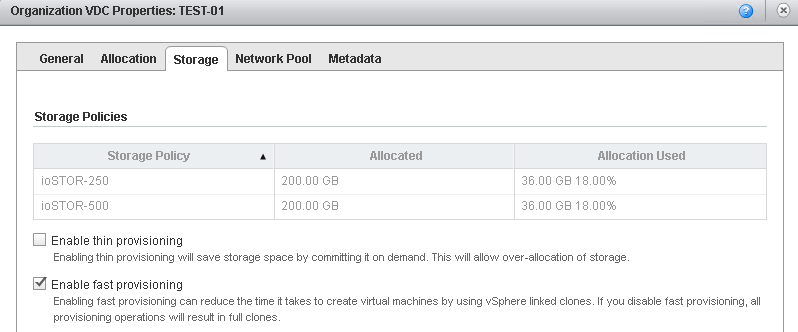
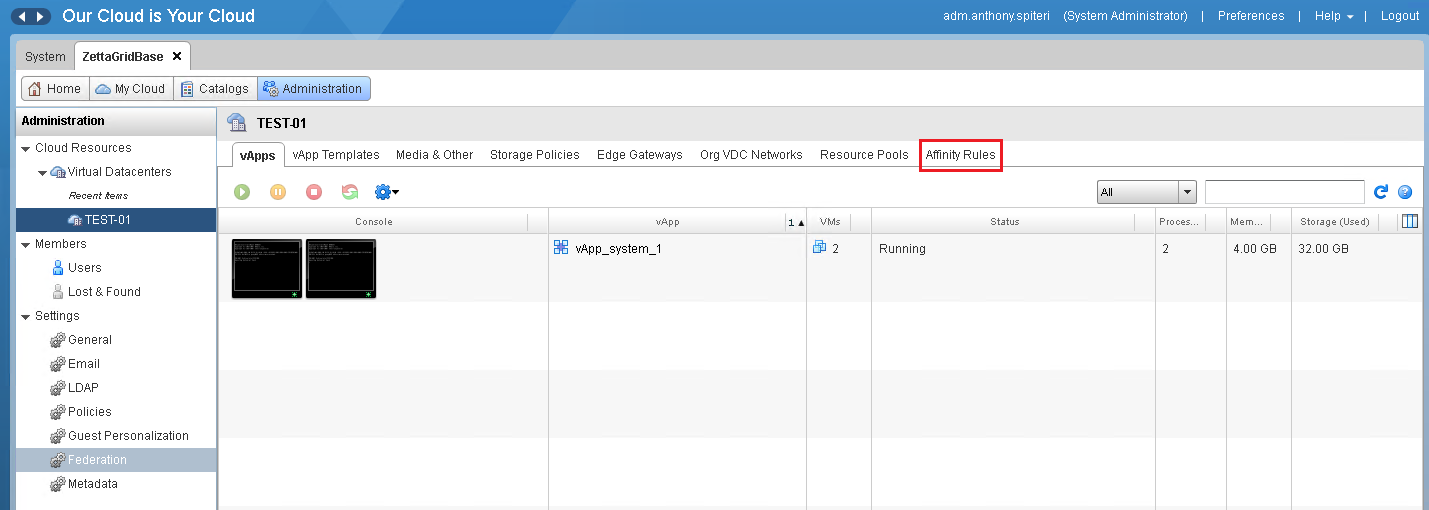
As mentioned last week VMware released vCloud Director SP 8.10 and with it a list of significant new features and improvements. In this series I'll go throug...
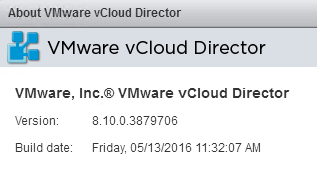
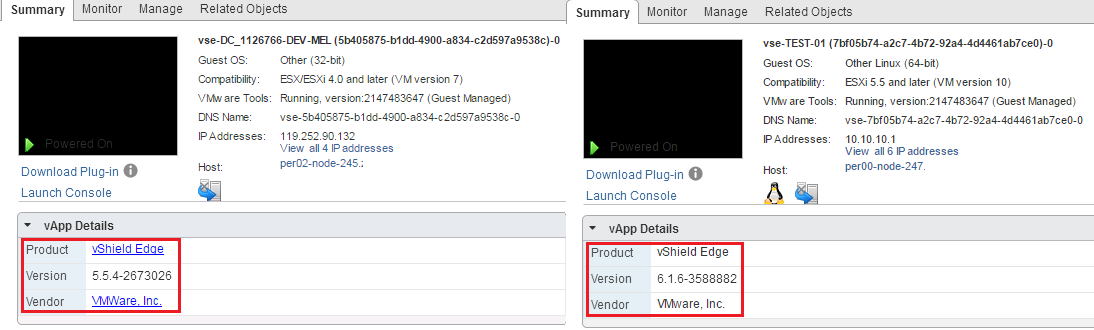
Earlier this morning VMware released vCloud Director SP 8.10 Build 3879706 . This is a significant release for vCloud Director as its the first release that ...

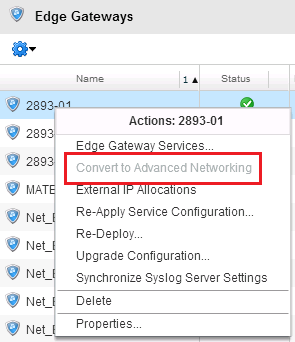
For a while now we have known that vCloud Networking and Security's days where numbered ...with the release of NSX as a replacement+ product it had been comm...
Somewhat hidden among the major releases that came our from VMware HQ yesterday was a point release for vCloud Director SP 8.x. This takes the vCD SP Build t...

This is a special post...apart from being this blog's 200th it's a great week for all those who have dedicated time and effort into VMware's vCloud Director....
It's been a big week for vCloud Director! For those still running the 5.6.x SP Build there was a point release last week taking vCD SP to 5.6.5 Build 3307437...

Last week I wrote a piece on the talk around vCloud Air’s demise or more to the point...the often suggested demise of VMware's Public Cloud Platform. The bas...

I’ve been wanting to write some commentary around the vCloud Air and Virtustream merger since rumours of it took place just before VMworld in Auguest and I’v...
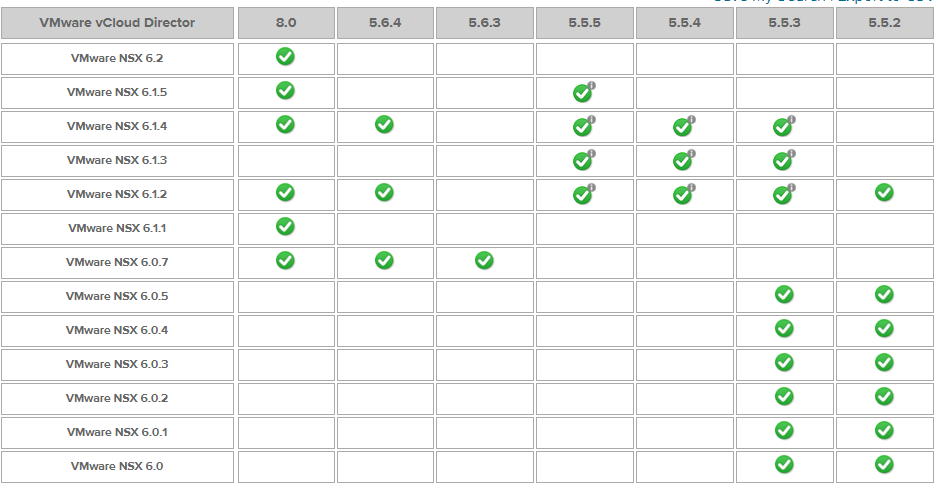
In what is welcome news for vCloud Air Service Providers that have integrated or are looking to integrate NSX-v into their offerings, NSX-v 6.2 is now offici...
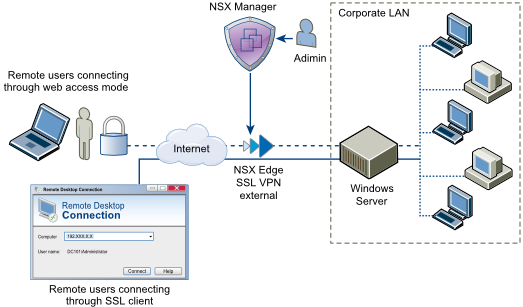
Overview : The SSL VPN-Plus feature has been around since the VSE 5.x days and as I've found out was possibly the best underused feature of the VSE. Contribu...

This is something to look out for if you are upgrading from vCloud Director 5.5.x to 5.6.x SP and if you have altered the syslog settings of your cells....Th...
Since June the vCloud Director SP Beta has been running with a lot of renewed interest in the IaaS Platform. The beta was well participated in and there was ...
Its been a couple of weeks since I wrote this post on the need for improvement with the vCloud Director UI and the response I've had to the article through t...
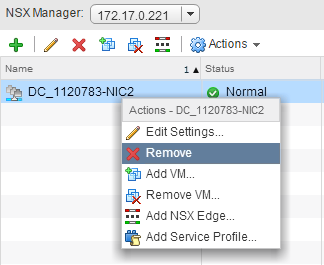
I came across an situation today where I was doing a clean up of Logical Switches in my NSX Lab where I was unable to remove a logical switch due to it appar...
The vCloud Director 8 SP Beta program has been going for a couple of months now and there has been decent activity in the Discussion Forums and also a good n...
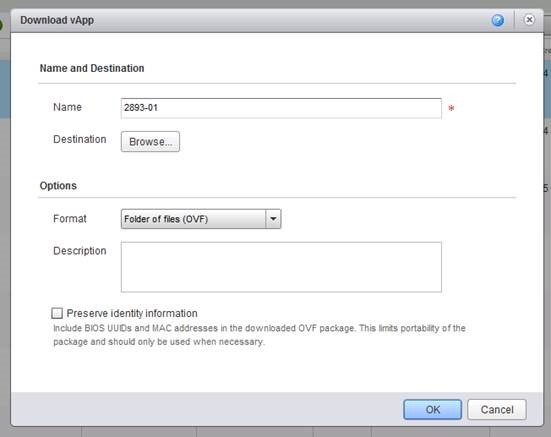
As those who have been using vCloud Director for a while...the ISO/OFV upload/download functionality can be frustrating to use at the best of times even thou...
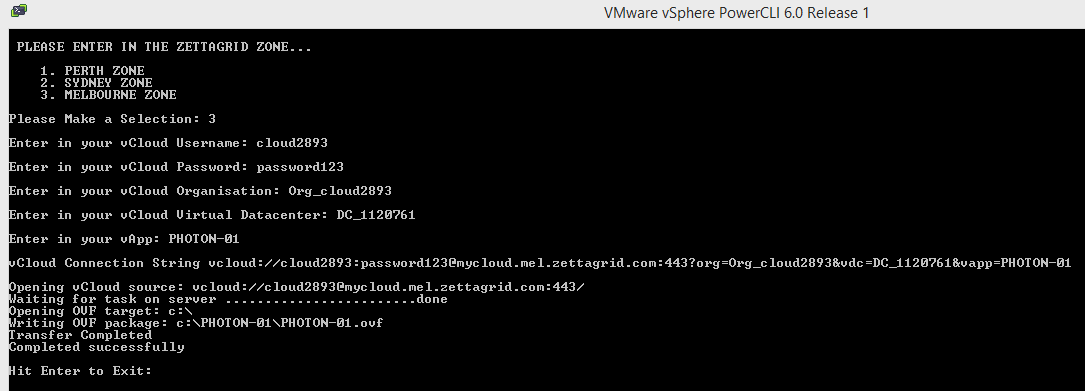
Last week I had a requirement to look at how to allow customers to export VM's and vApps from our vCloud Director Zones without using the UI. I've known abou...
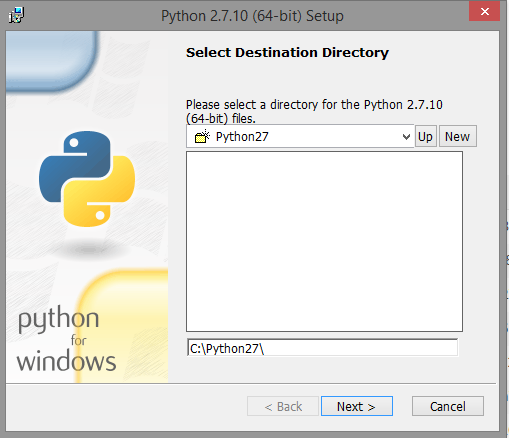
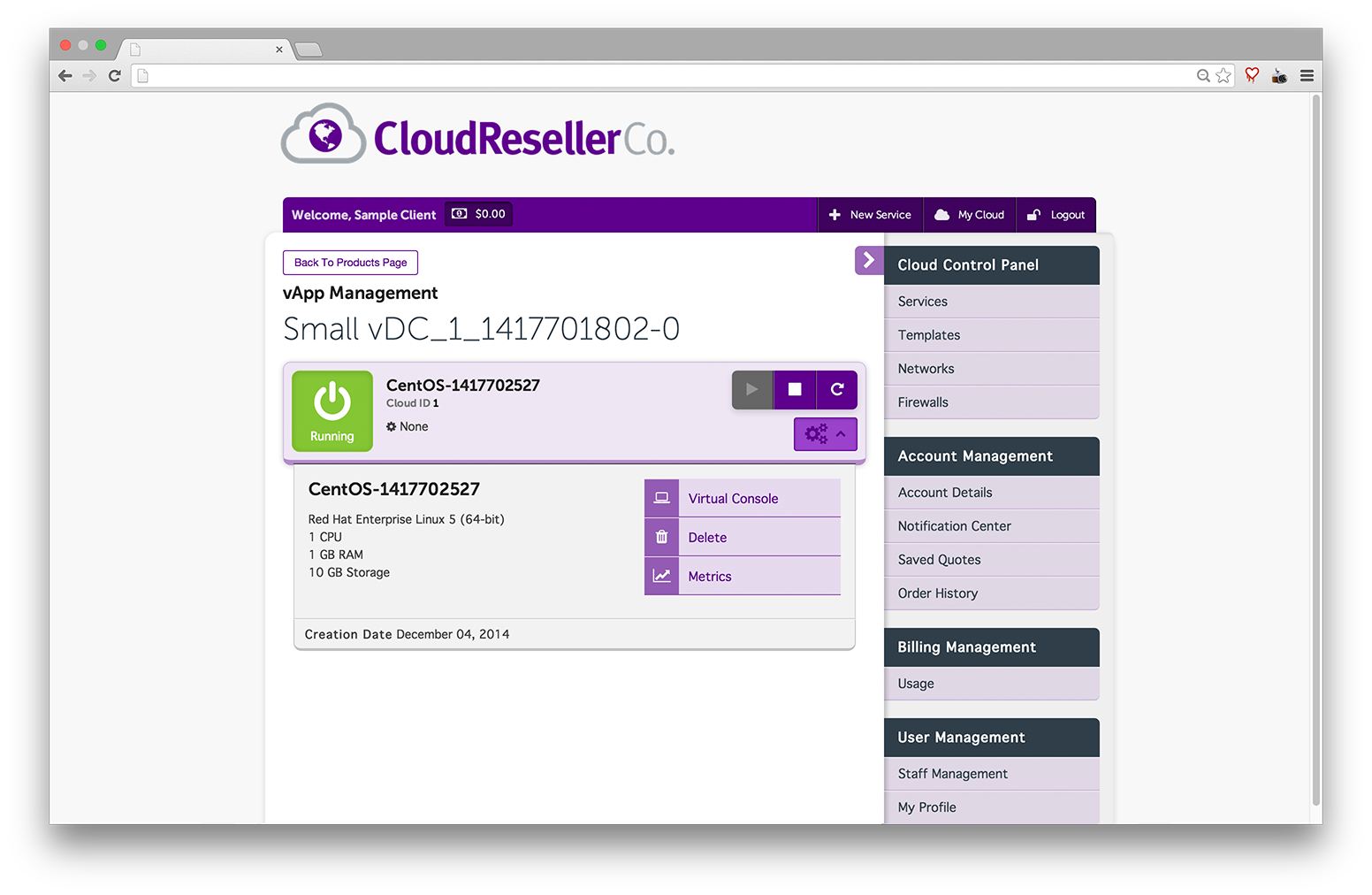
There is a lot of talk going around how IT Pros can more efficiently operate and consume Cloud Based Services...AWS has lead the way in offering a rich set o...
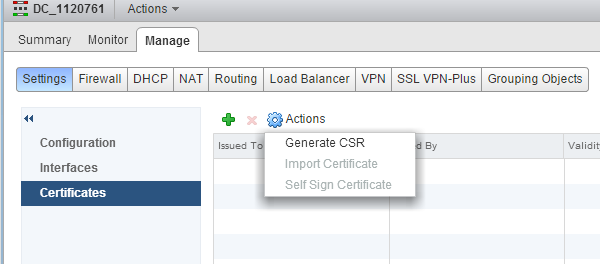
Overview : With the VSE and NSX Edges there are a number of features that can take advantage of Certificate services both as authentication mechanisms and fo...
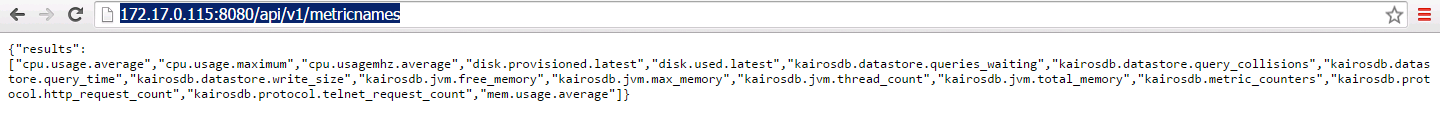
vCloud Director SP 5.6.x has the ability to export VM statistics to an external database source which can then be queried via a set of new API calls. I've go...
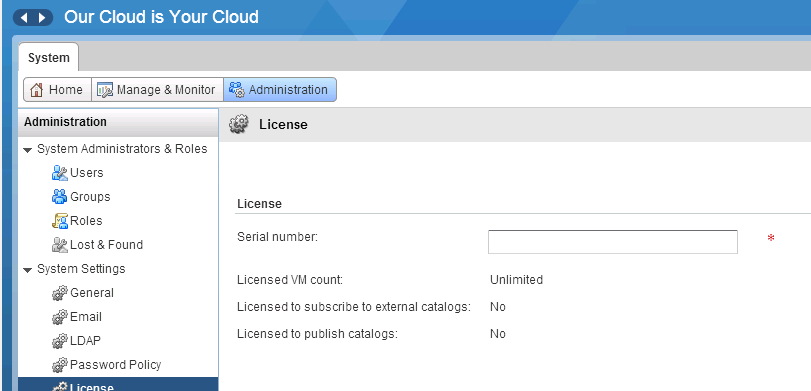
Thought I'd put up a very quick post on the process of upgrading from vCloud Director 5.5.x to vCloud Director SP 5.6.x. Any previous license key that you ha...
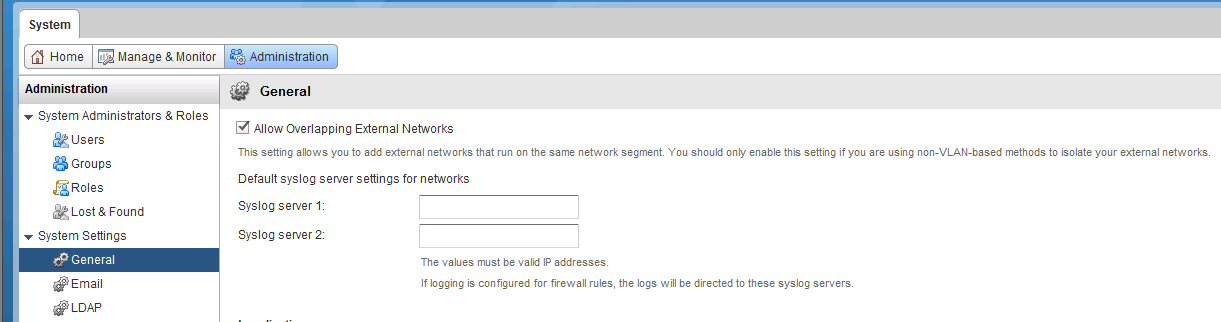
Part 4: vCloud Director Overlapping Networks : vCloud Director has the ability to allow Overlapping Network segments configurable from the Administration Tab...
vCloud Air Network Service Providers take note...rumours of vCloud's death where greatly exaggerated. Enterprise users...I still feel you are missing out on ...
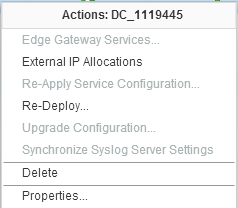
If you are familiar with vCloud Director Edge Gateway Services you might have come across situations where Edges become unmanageable and you see the followin...
Earlier in the week I did up a post on the vCloud Air On Demand Signup Process . As I've blogged about in the past, VMware reaffirmed their commitment to the...
We have been working with VMware GSS on an issue for a number of weeks whereby we were seeing some vShield Edge devices go into an unmanageable state from wi...
There is a lot of talk going around how IT Pros can more efficiently operate and consume Cloud Based Services...AWS has lead the way in offering a rich set o...
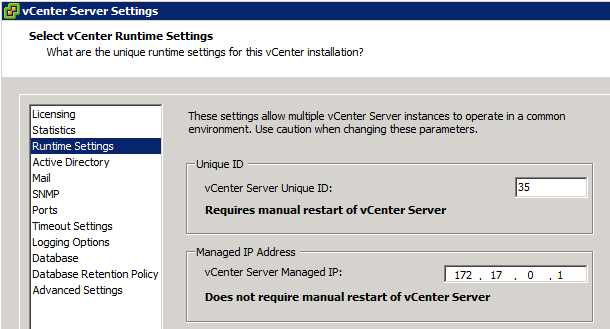
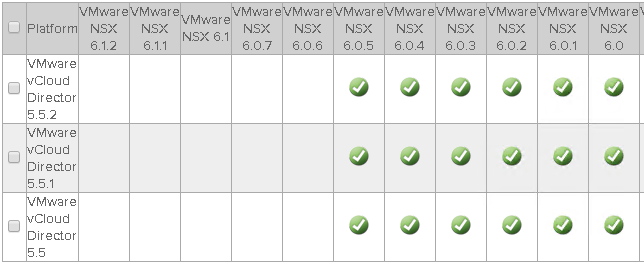
During my initial work with NSX-v I was running various 6.0.x Builds together with vCD 5.5.2 and vCenter/ESXi 5.5 without issue. When NSX 6.1 was released I ...
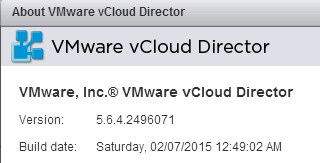
In October 2014 VMware released vCD SP 5.6.3 which was the first version of vCloud Director that was forked for Service Providers. As I mentioned in this pos...
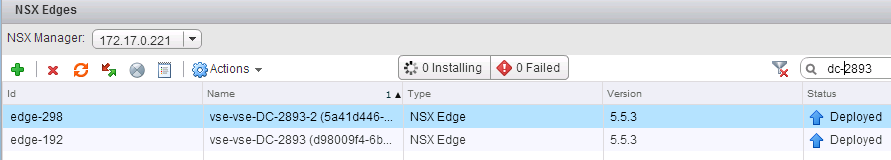
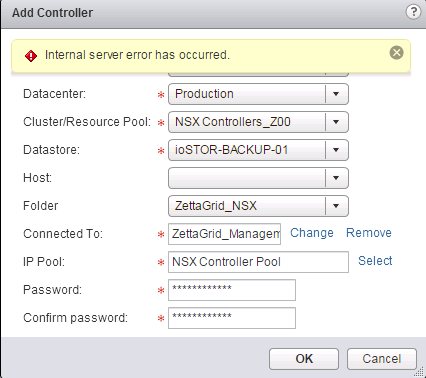
This blog series extends my NSX Bytes Blog Posts to include a more detailed look at how to deploy NSX 6.1.x into an existing vCloud Director Environment. Ini...
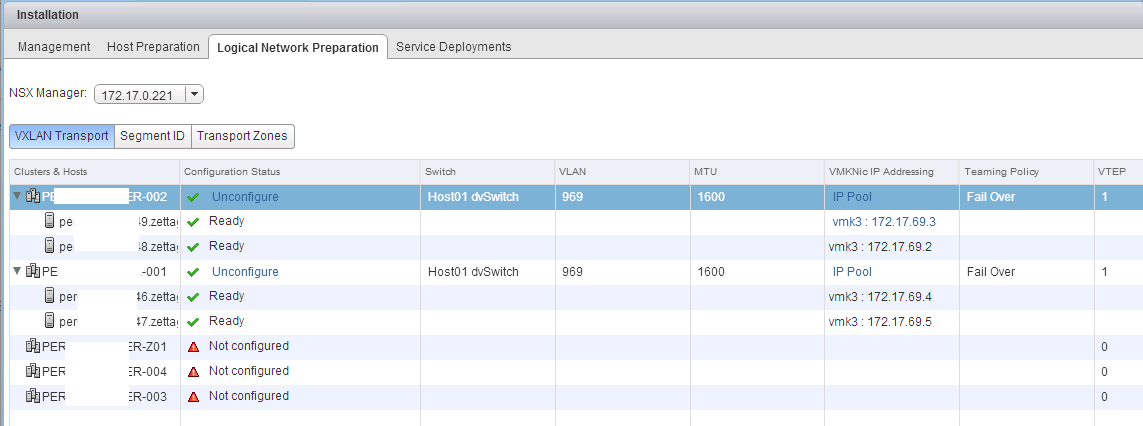
This blog series extends my NSX Bytes Blog Posts to include a more detailed look at how to deploy NSX 6.1.x into an existing vCloud Director Environment. Ini...
vCloud Director SP 5.6.3 was initially released in October 2014 was the first of the SP Editions that had been forked from the Enterprise 5.x builds that cam...
This blog series extends my NSX Bytes Blog Posts to include a more detailed look at how to deploy NSX 6.1.x into an existing vCloud Director Environment. Ini...
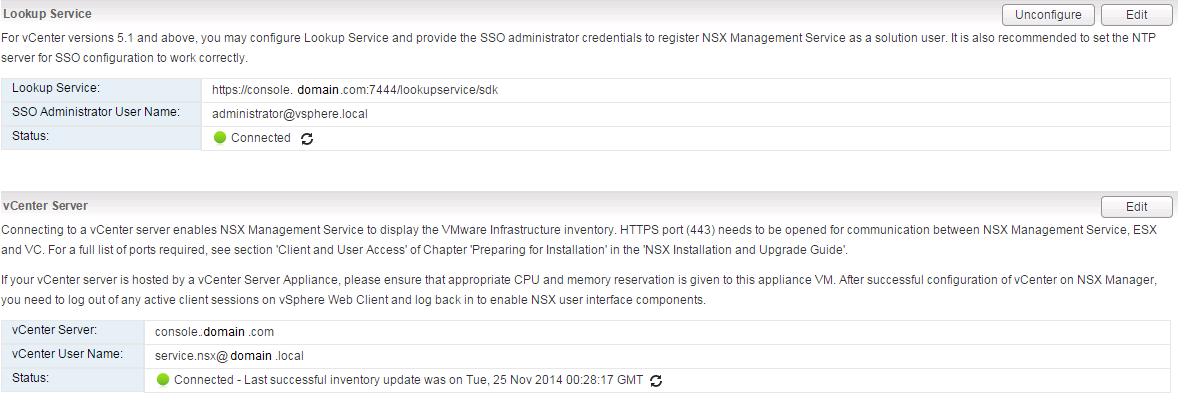
This blog series extends my NSX Bytes Blog Posts to include a more detailed look at how to deploy NSX 6.1.x into an existing vCloud Director Environment. Ini...
Part 1: Intro and VSM to NSX Manager Upgrade Part 2: NSX Manager Configuration and vCD VSE Deployment Validation Part 3: Controller Deployment, Host Preparat...

"With regards to the upgrade path for SPs looking to deploy vCD SP there will be a build released approx. Q1 15 that will allow upgrades from 5.5.2" On the 8...
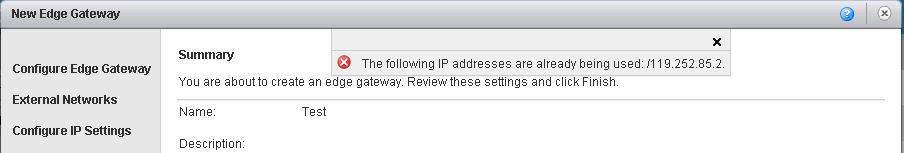
A few months ago I wrote a quick post on a bug that existed in vCloud Director 5.1 in regards to IP Sub Allocation Pools and IP's being marked as in use when...
A couple of years ago I remember first hearing about Project Zepher which was rumored to be VMware's first attempt at a public cloud offering...though it was...
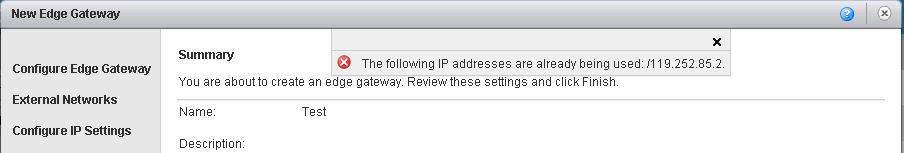
A few months ago I wrote a quick post on a bug that existed in vCloud Director 5.1 in regards to IP Sub Allocation Pools and IP's being marked as in use when...
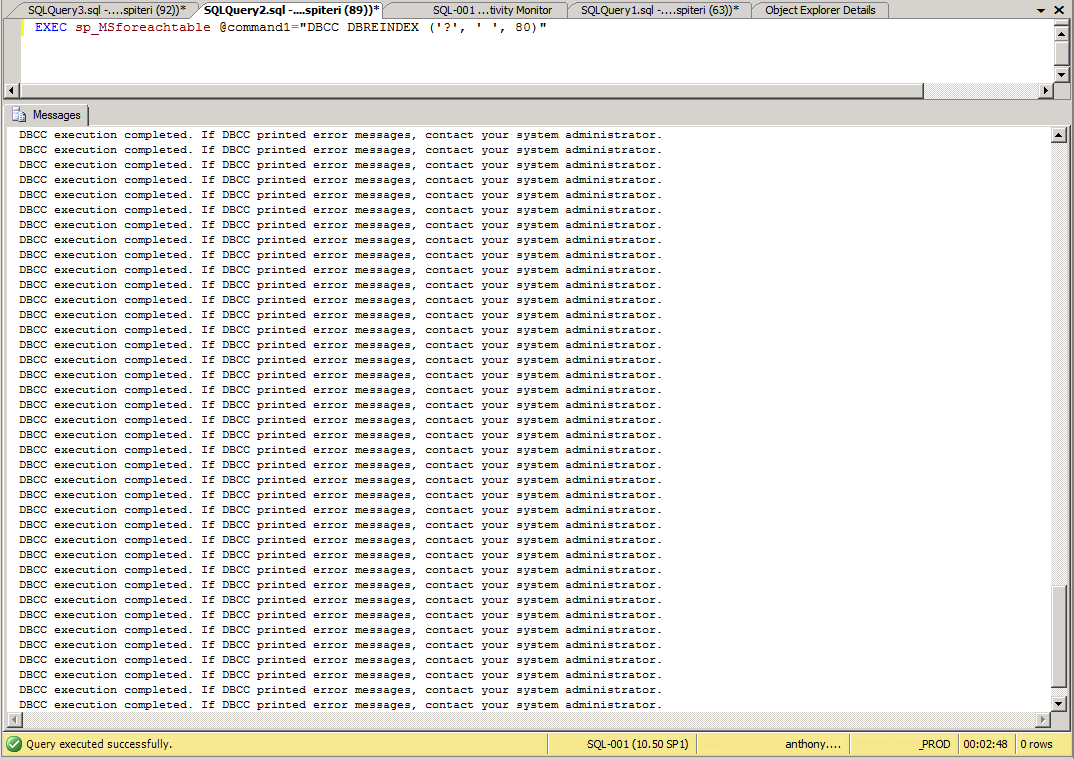
Generally speaking upgrading the vCloud Director binaries is a pretty straight forward task. It's a two step process where the Cell's are upgraded first foll...
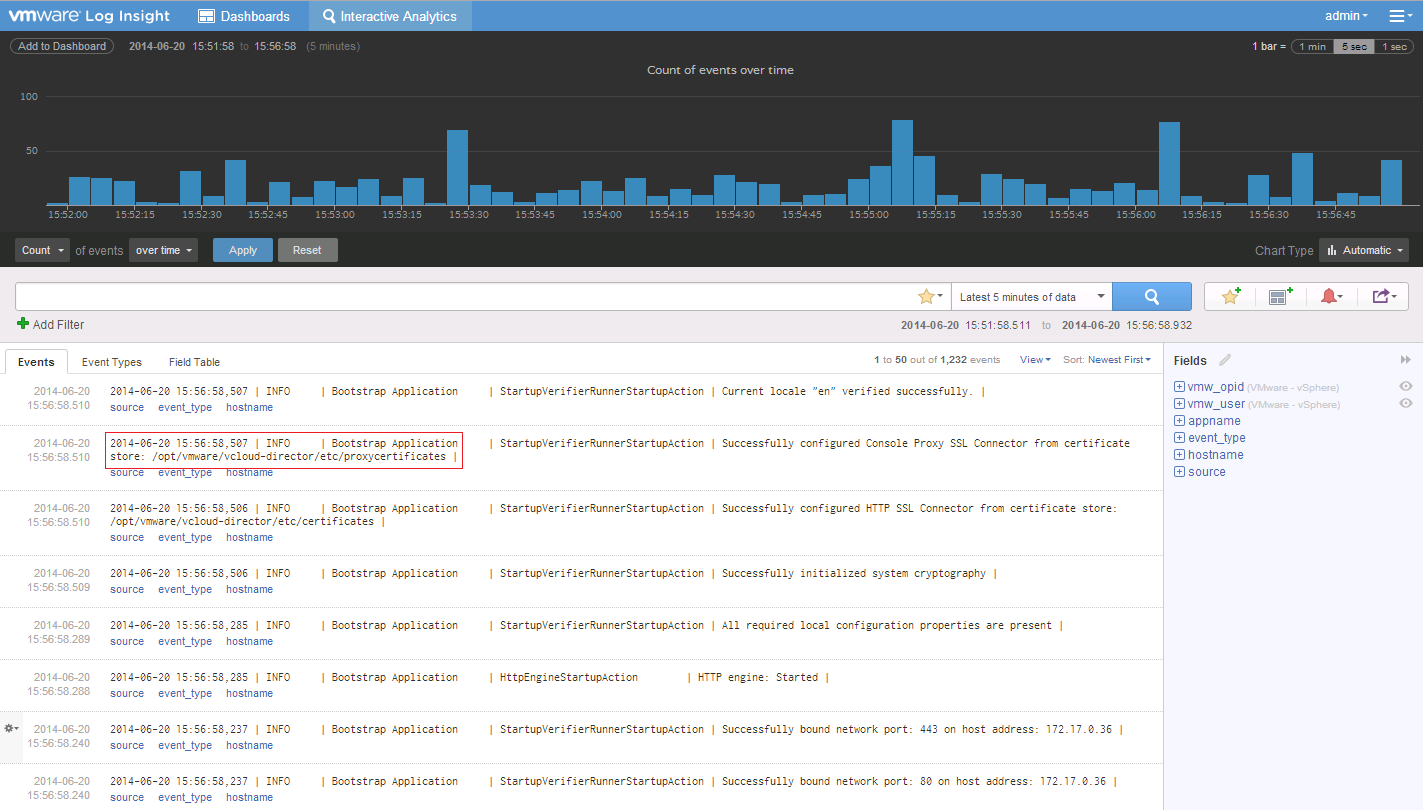
Recently v2.0 of VMware Log Insight became GA, and I've been playing around with it since it's release. Having been on the BETA of the 1.5 Version the 2.0 Ve...
Sometimes I think there is change just for the sake of change...or to keep us on our toes :) Either way I just came across an interesting upgrade gotchya whe...
Just after the release of VSAN a couple weeks back, I wrote this post talking about the need for VSAN to appear on the VSPP pricelist. At the time there only...
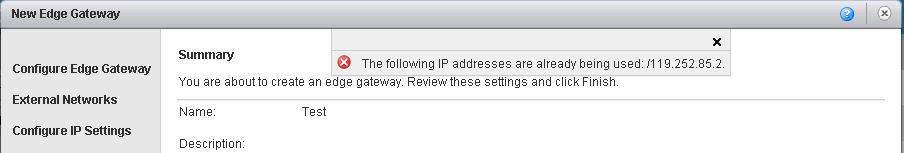
After our recent upgrade of vCloud Director from 1.5 to 5.1.2 we started to see some errors during our automated provisioning of VSEs that included the sub a...
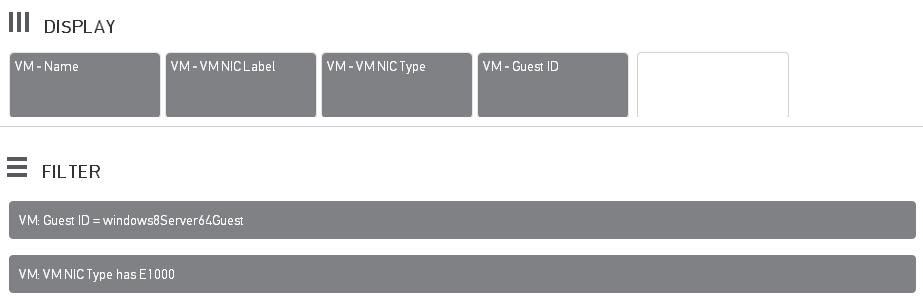
Over the past couple of months we have seen a number of support requests coming into our HelpDesk around network connection dropouts in Windows Server 2012 G...
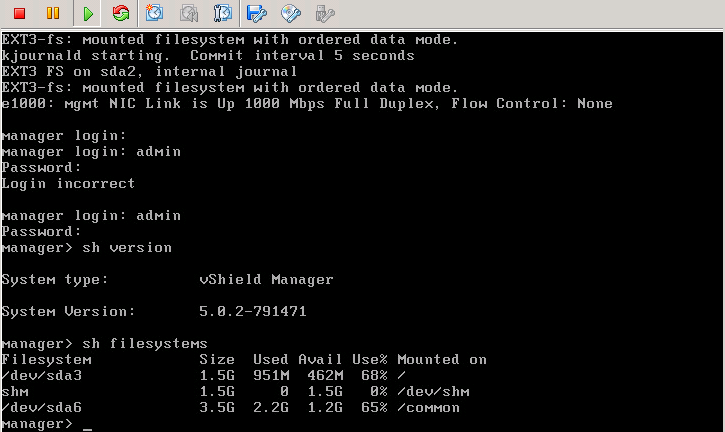
Having recently just completed the upgrading our vCloud Platform from 1.5 to 5.1 I thought it best to share my experiences around the upgrading of the vShiel...
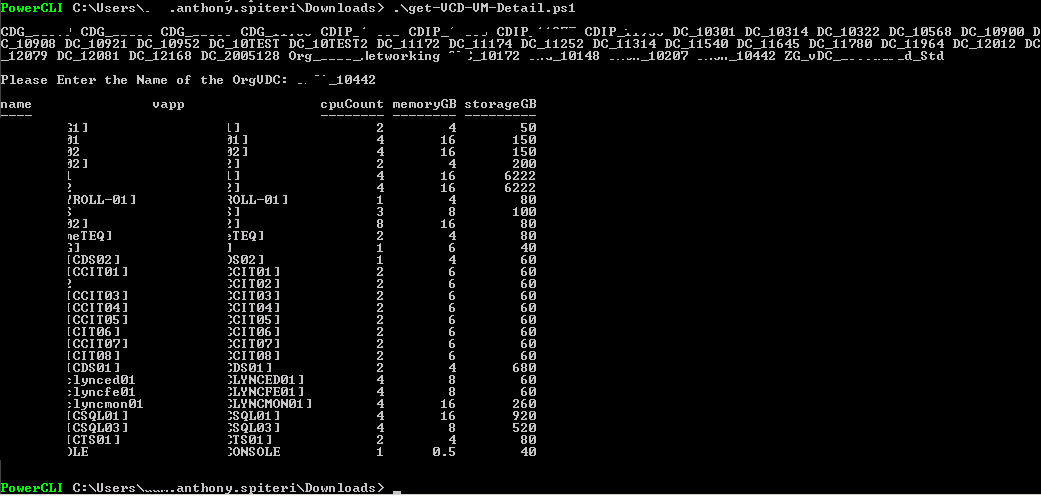
I had been looking for a way to get quick reports from our vCloud Zones using PowerCLI that reports on VM Allocated Usage. Basically I wanted to get a list o...
Over the last couple of weeks I've been fortunate to represent ZettaGrid, as a Platinum Sponsor of the VMware Series 2013 road shows in Melbourne and Sydney....
There where some pretty big announcements and reveals at VMworld 2012, but unless I missed something (which was totally possible had any accouncement been ma...
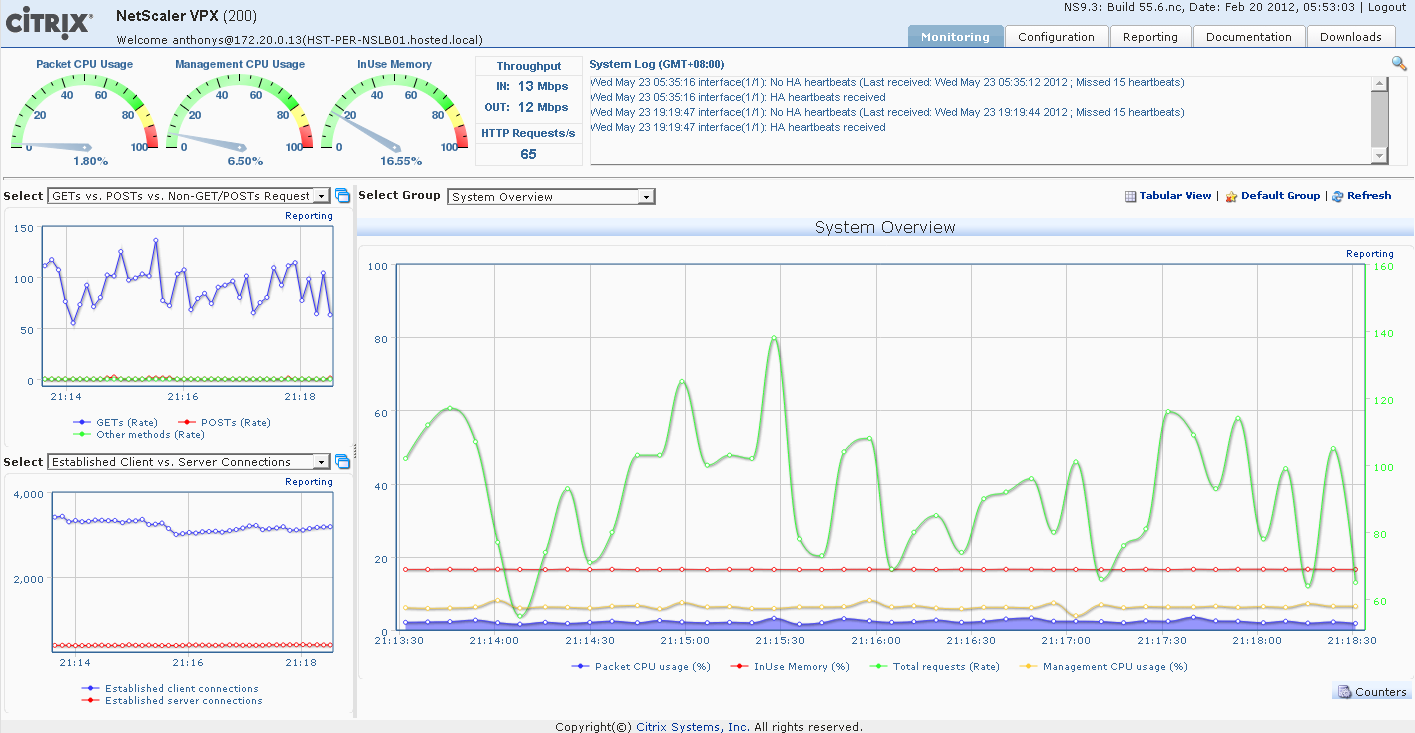
Ive come across a couple of how-to's on configuring vCloud Cells in a highly available Load Balanced environment. There is a good overview here by @hany_mich...
If you had asked me 2 years ago that I'd be writing as a VMware vExpert I would have thought you were crazy. At that stage my only exposure to VMware was on ...