Opinion: VMware and NVIDIA Step Up on Private AI for Enterprises
It's not a surprise that Generative AI featured heavily as a topic at VMware Explore US last week in Vegas. 2023 is the year that most large tech companies j...
Tag
95 posts
It's not a surprise that Generative AI featured heavily as a topic at VMware Explore US last week in Vegas. 2023 is the year that most large tech companies j...

NOTE: The following content was transcribed and modified from the Thoughts on X podcast…Click Play if you would like to listen. I think we should all put a p...

I must say... it was good to be back at the Mascone Center and San Francisco for VMware Explore 2022. Some people might question my excitement at getting bac...
I’m currently heading over to the newly renamed VMware Explore and it’s not been lost on me that this is the 10th anniversary of my very first VMworld back i...

Ok, here we are... it's been three years since VMworld 2019 and we are back next week in San Francisco at the Mascone Centre. But we are not attending VMworl...
It's been a while since i've done a vSphere specific Quick Fix post, but the great thing about tinkering and labbing is that you run into situations and corn...

One of the things I wanted to do this year was get back into technologies, applications, platforms or solutions that I have drifted away from over recent yea...

Overnight, we released v11a ( Build 11.0.1.1261 ) of our flagship product, Veeam Backup & Replication. This is the first major update to v11 which was releas...

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...
This week VMware is holding an online event to make and announcement around its vision for Application and Cloud Transformation . What does that exactly mean...

A Challenging Year for Community For a lot of us in the IT Industry, 2020 made it difficult to advocate technology like we had done in previous years. No dou...
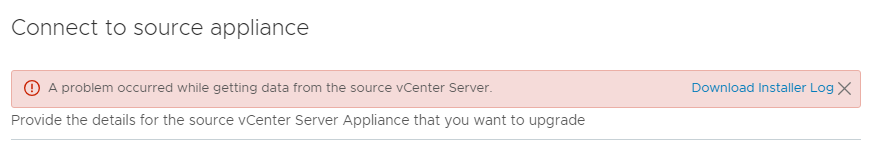
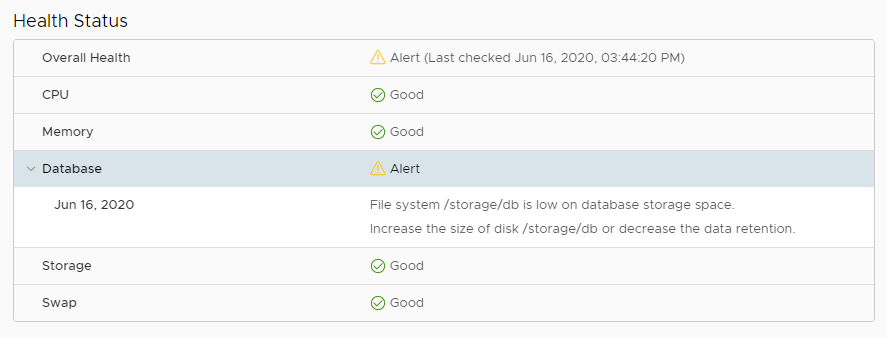
2020 Update : It seems as though this issue also pops up if doing a major version upgrade of the VCSA through the migration option. I was getting this error ...
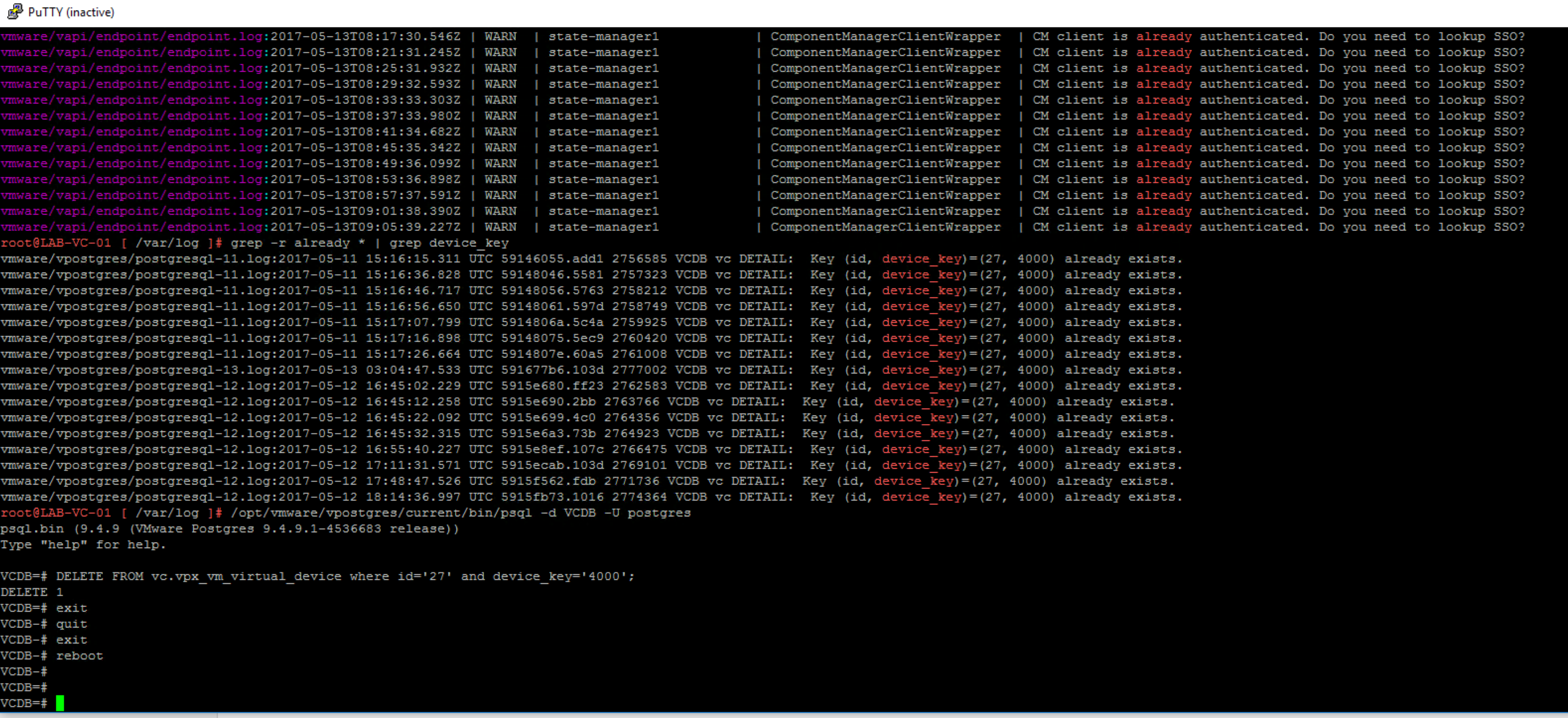
2020 Edit: Seems like this error has been updated in vSphere 7.x to be a little more friendly and less terminal. The old error I referenced below was somethi...
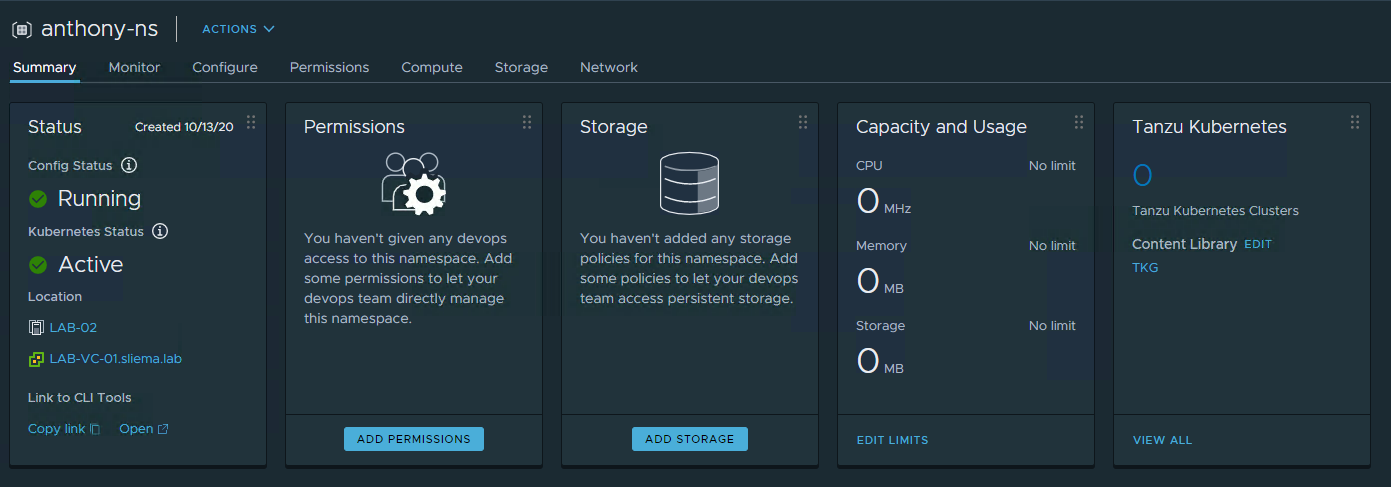
VMware released Update 1 of vSphere 7 last month and one of the big things to come out of that release was the ability to deploy Tanzu Basic which is vSphere...
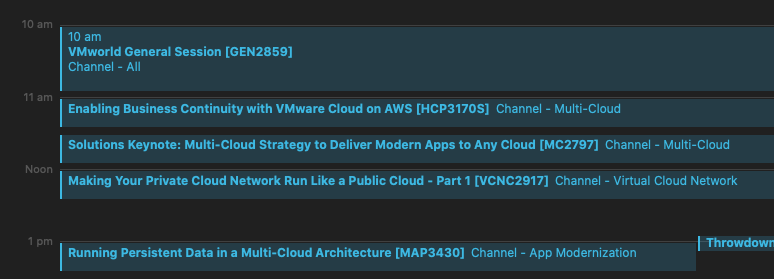
VMworld 2020 is happening today! And as I have banged on about over the past week, this is a very very different VMworld. No one will be lining up for overfl...

VMworld has been leveraged by a lot of people to help advance their careers with a lot of advancement seeded by personal interactions at the conference. Soci...

VMworld 2020 is now only a couple of days away, and this year we will all be experiencing the conference remotely. Without question this will be a different ...

VMworld 2020 is different this year... but in this COVID year, we are only five days away from kicking off Virtually. The content catalog for the Virtual eve...

It is crazy to think that we could celebrate (those of us brave enough to admit it) the birthday of the piece of software. Throughout modern history, softwar...
Over the weekend, we released the v10a ( Build 10.0.1.4854 ) release of our flagship product, Veeam Backup & Replication. This is the first major update to v...

I'm a fan of a good streak... but 2020 has forcefully ended a couple of existing streaks that I had in play. One of those was my annual trip over to Melbourn...
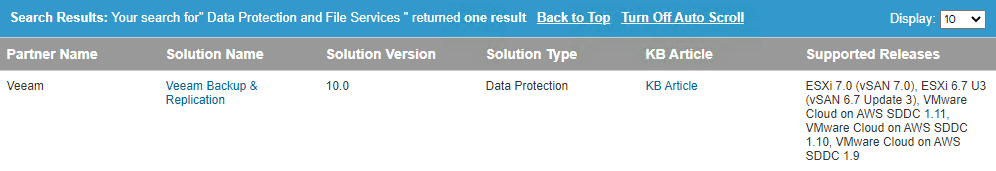
VMware still represents a strong focus for the foundation of our core platform supportability. VMware workloads are still easily the most protected workloads...
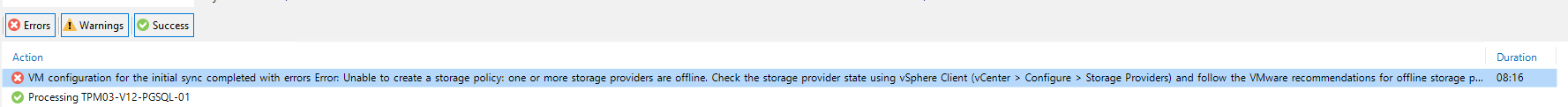
I had a situation earlier this week where the VMware SDK/API service was being reported as offline. I was triggered by some failed backup jobs which made me ...
This is a very quick post to let people know that from the first of June, till the 20th of June, applications are open for the half yearly intake into the VM...

When VMware Cloud on AWS was announced in 2017 , it was met with trepidation and caution from the industry. Regardless of how successful the platform has bee...

It shouldn't come as a surprise that I'm writing about an event that is being held online... especially in this very moment in time. 2020 is the year of the ...
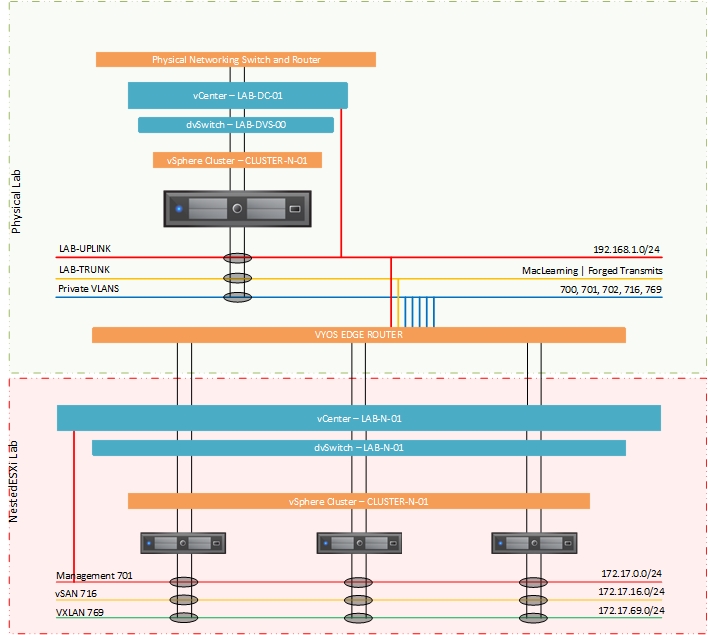
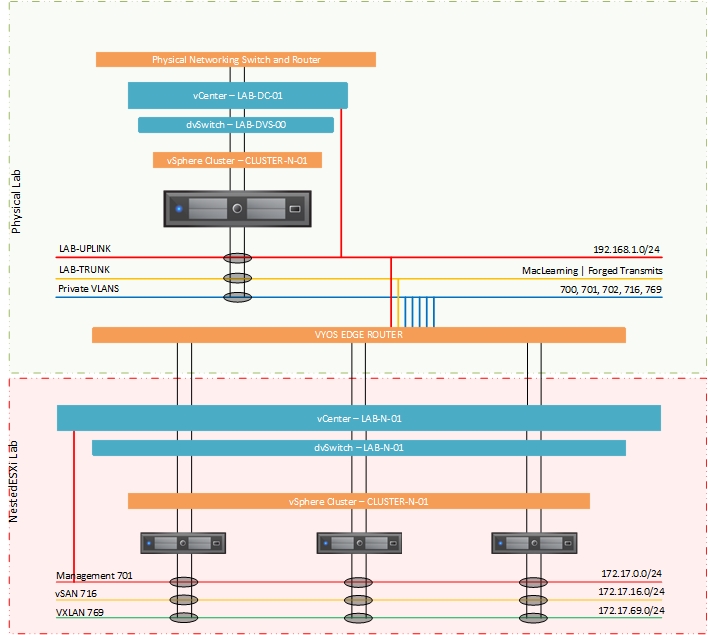
Back for part two of this look at how I went about configuring a single host for NestedESXi deployments. In the previous post I looks at the physical configu...
As usual, I like to jump right into software upgrades to test out new functionality (on none production systems of-course). With the GA of vSphere7 overnight...
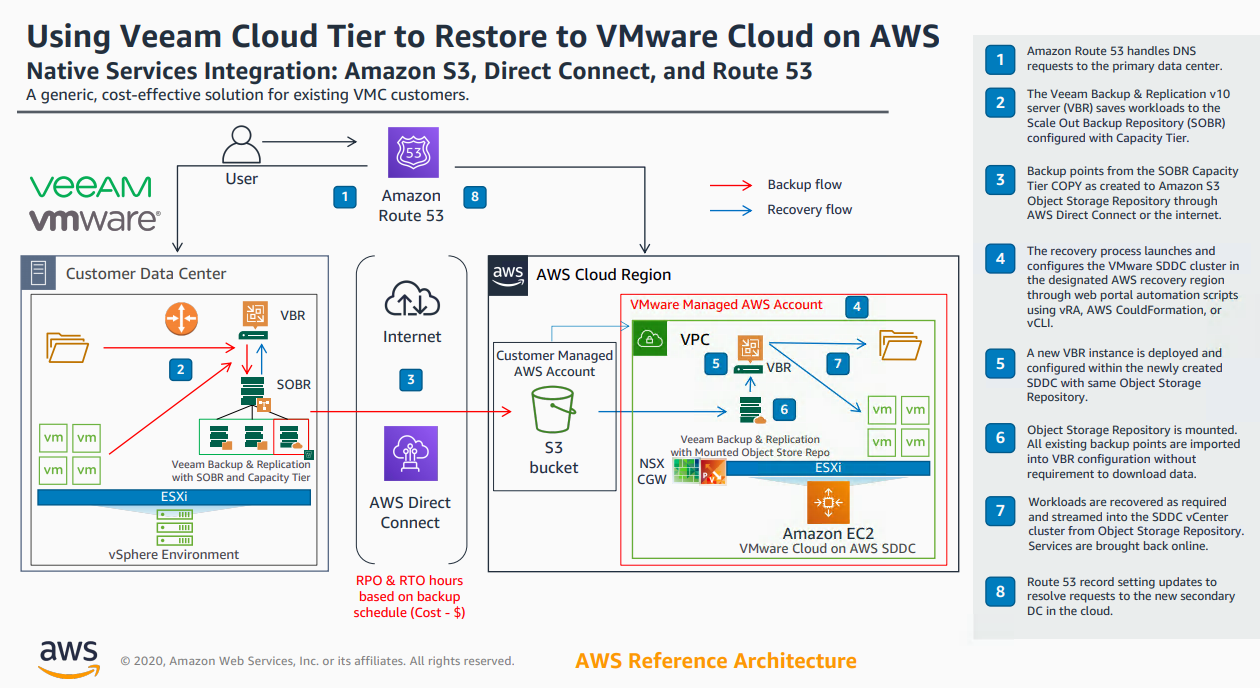
With the release of v10 of Backup & Replication came significant enhancements to the Cloud Tier. As I wrote about here , we introduced Copy Policy , Immutabi...
I've should have written this article a long long time ago! In fact, i've been promising certain people that I would write this up for a number of years. The...
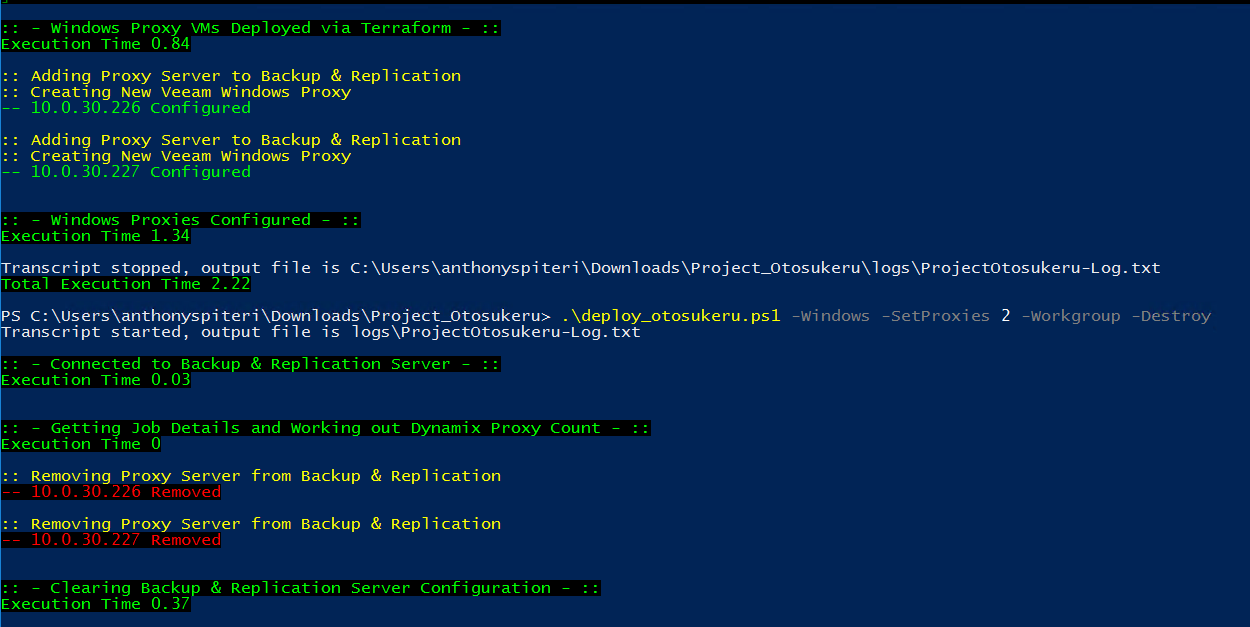
My recent obsession with automation and Infrastructure as Code in general has resulted in a lot of efficiencies in my day to day work life. Where I used to d...

Today, VMware announced the vExpert class of 2020 and as per usual this generated lots of social media buzz as well as the now customary backlashes that have...
Over the last few years the amount of CBT related issues has decreased significantly from VMware. I remember back in my previous roles of having to deal with...
Over the last few years the amount of CBT related issues has decreased significantly from VMware. I remember back in my previous roles of having to deal with...
Apart from the K word, there was one other enduring message that I think a lot of people took home from VMworld 2019 . That is, that Dev and Ops should be co...
Kubernetes Kubernetes, Kubernetes... say Kubernetes one more time... I dare you! If it wasn't clear what the key take away from VMworld 2019 was last week in...

Everything to do with VMworld this year feels like it's arrived at lightning speed. I actually thought the event was two weeks away as the start of the week....
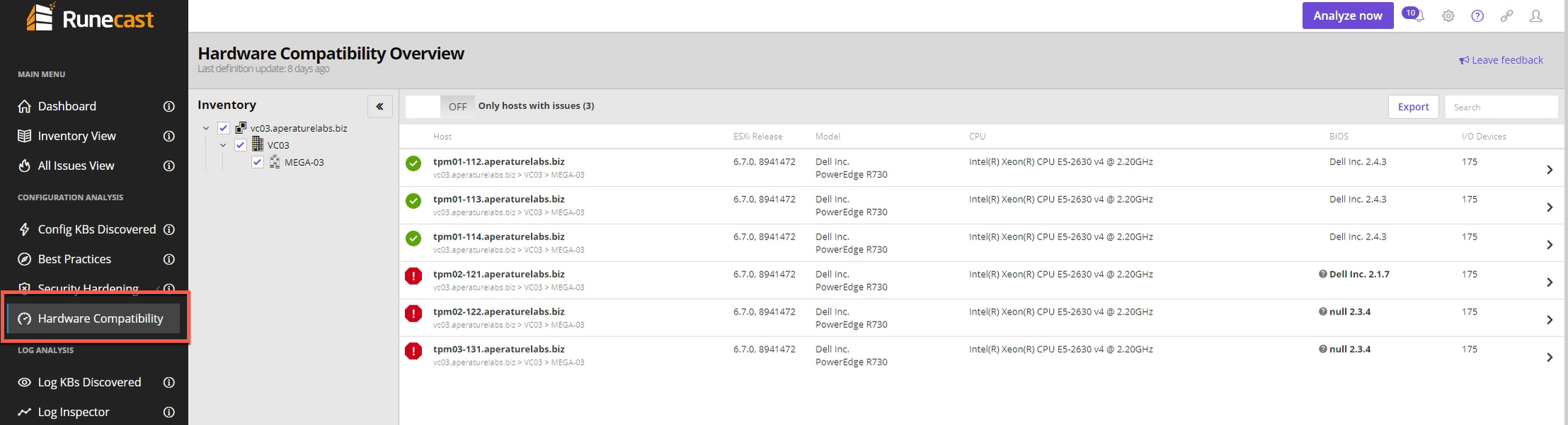
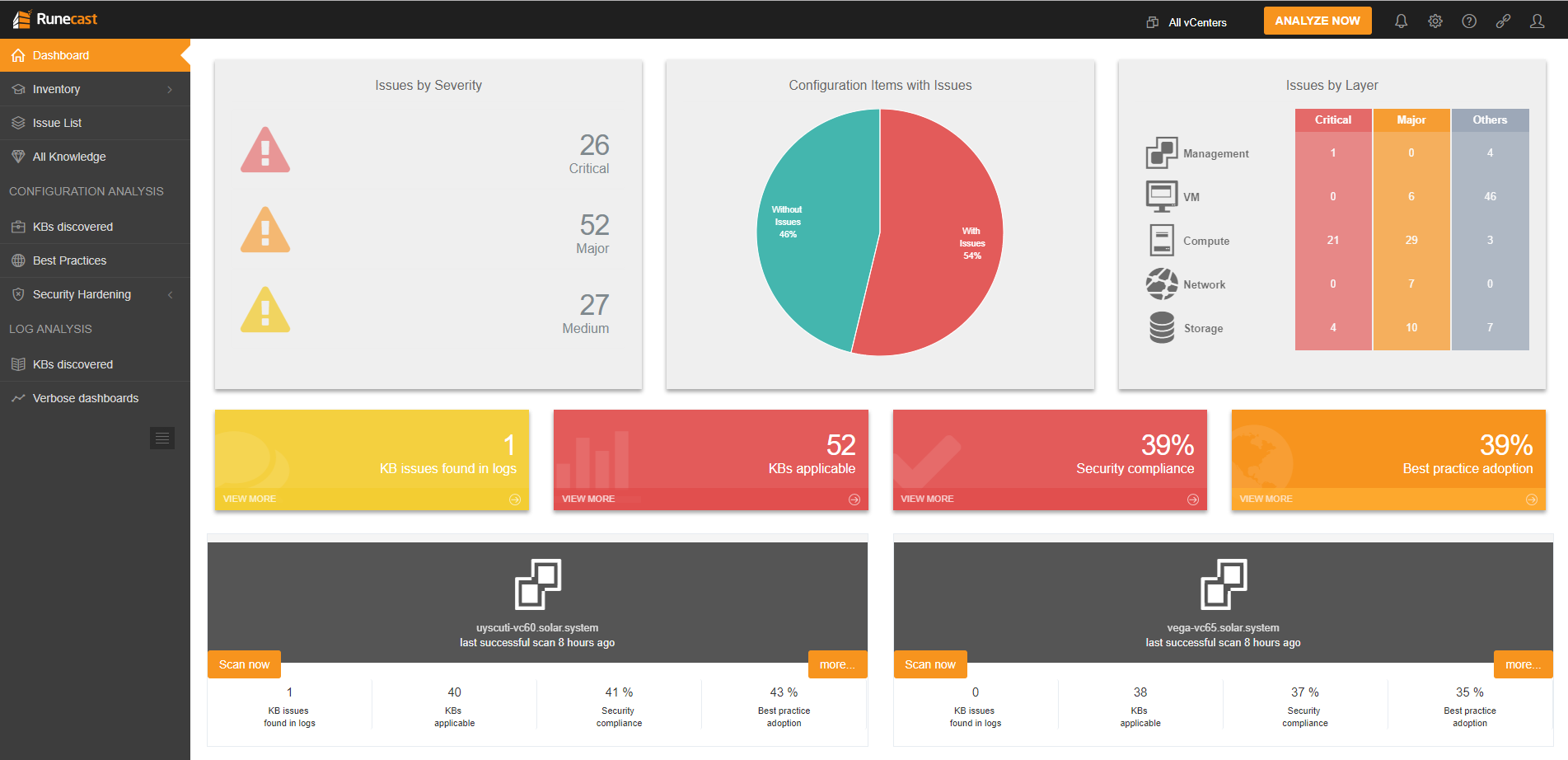
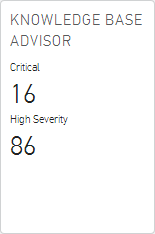
Two years ago at the 2017 Sydney and Melbourne UserCons, I spent time with a couple of the founders of Runecast, Stanimir Markov and Ched Smokovic and got to...
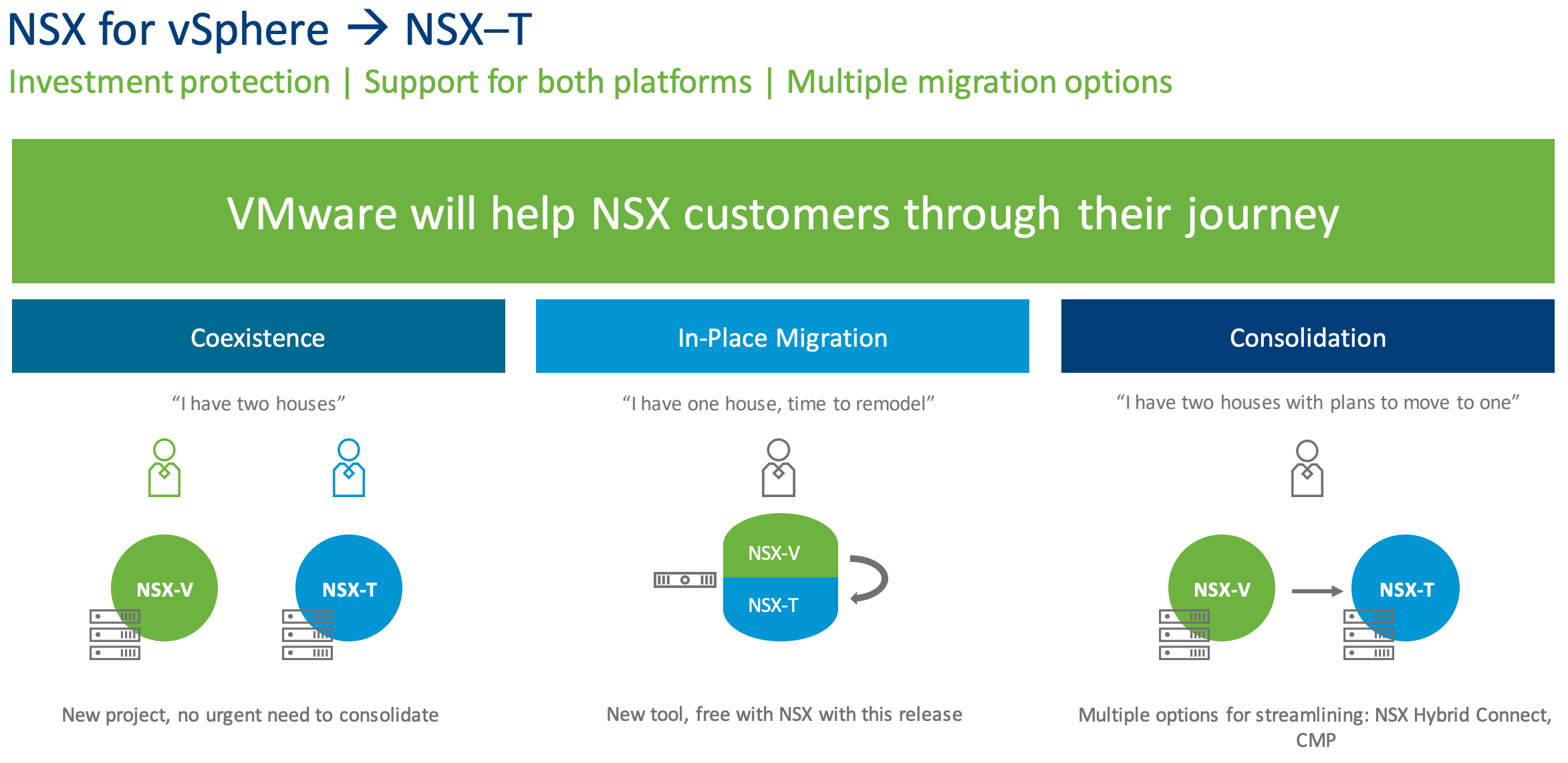
A little over two years ago in Feburary of 2017 VMware released NSX-T 2.0 and with it came a variety of updates that looked to continue to push NSX-T beyond ...
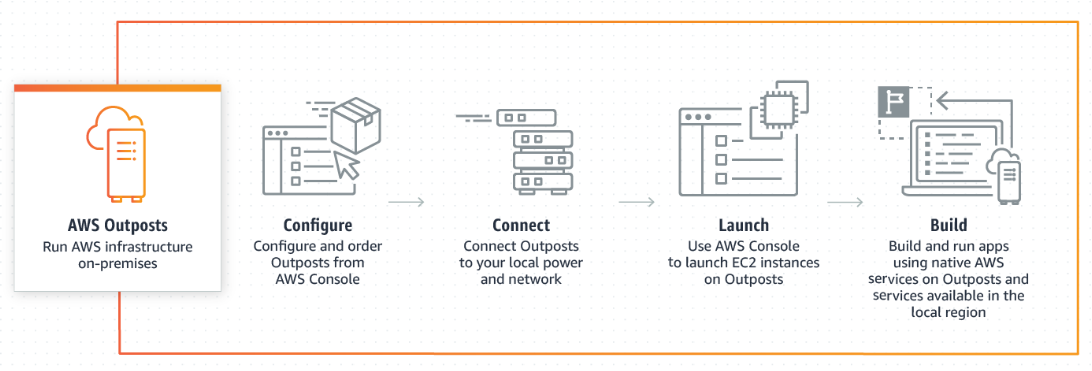
Now that AWS re:Invent 2018 has well and truly passed...the biggest industry shift to come out of the event from my point of view was the fact that AWS are g...
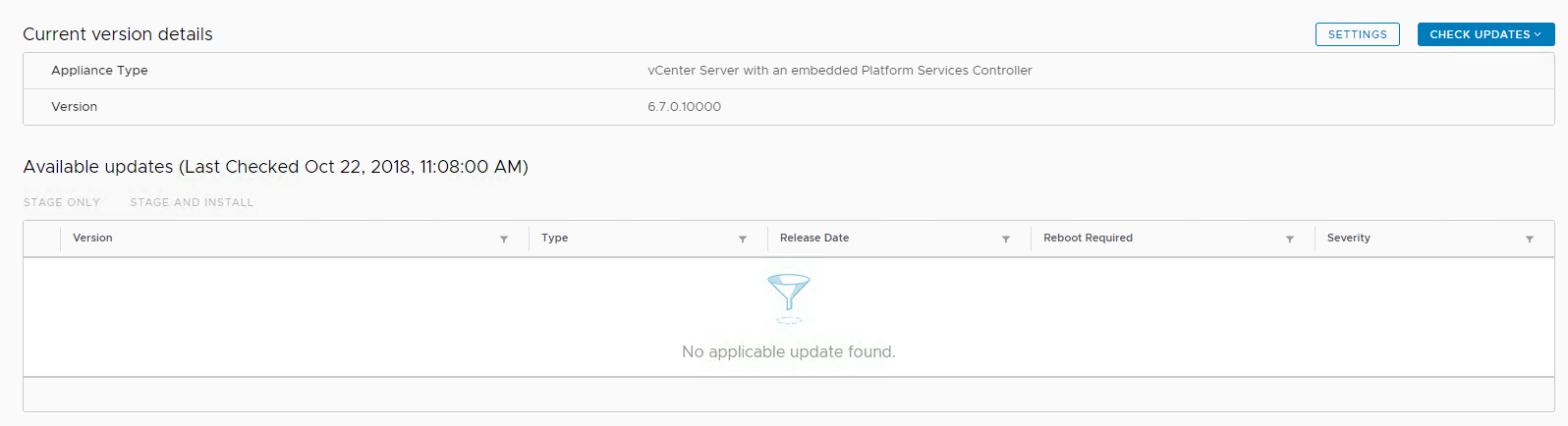
I had an issue with my VCSA today trying to upgrade to vCenter 6.7 Update 1 whereby the Management Interface Upgrade option was not detecting the update to u...
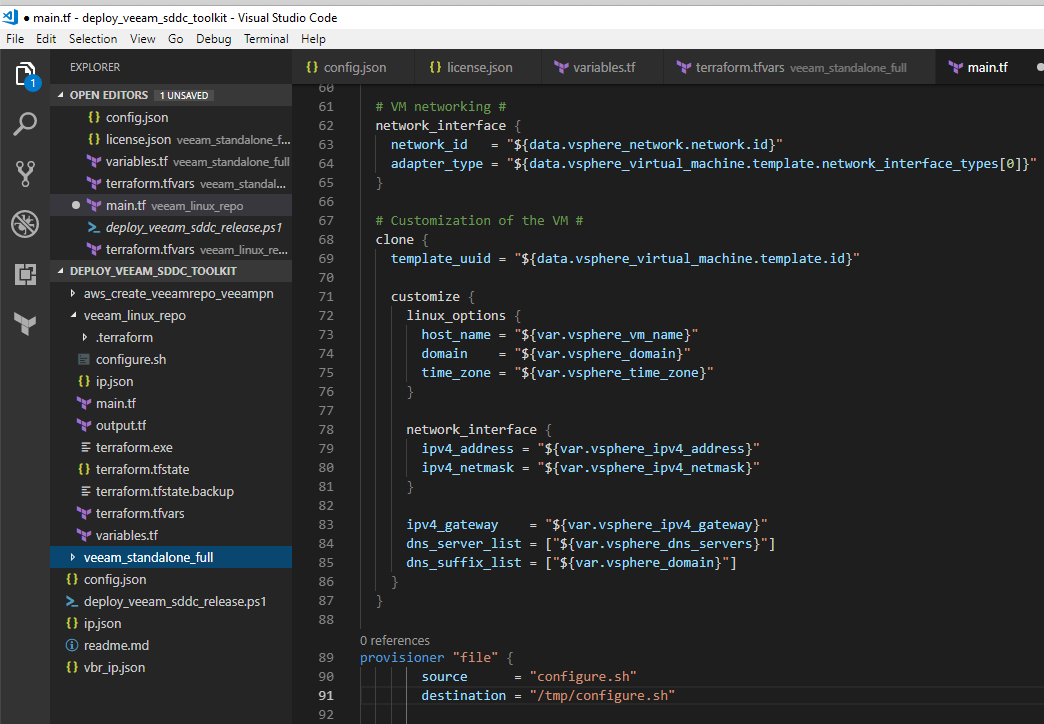
Last week I was looking to add the deployment of a local CentOS virtual machine to the Deploy Veeam SDDC Toolkit project so that it included the option to de...
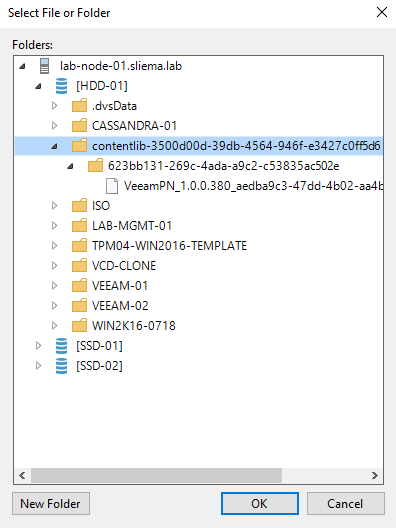
A question came up in the Veeam Forums this week about how you would backup the contents of a Content Library. As a refresher, content libraries are containe...
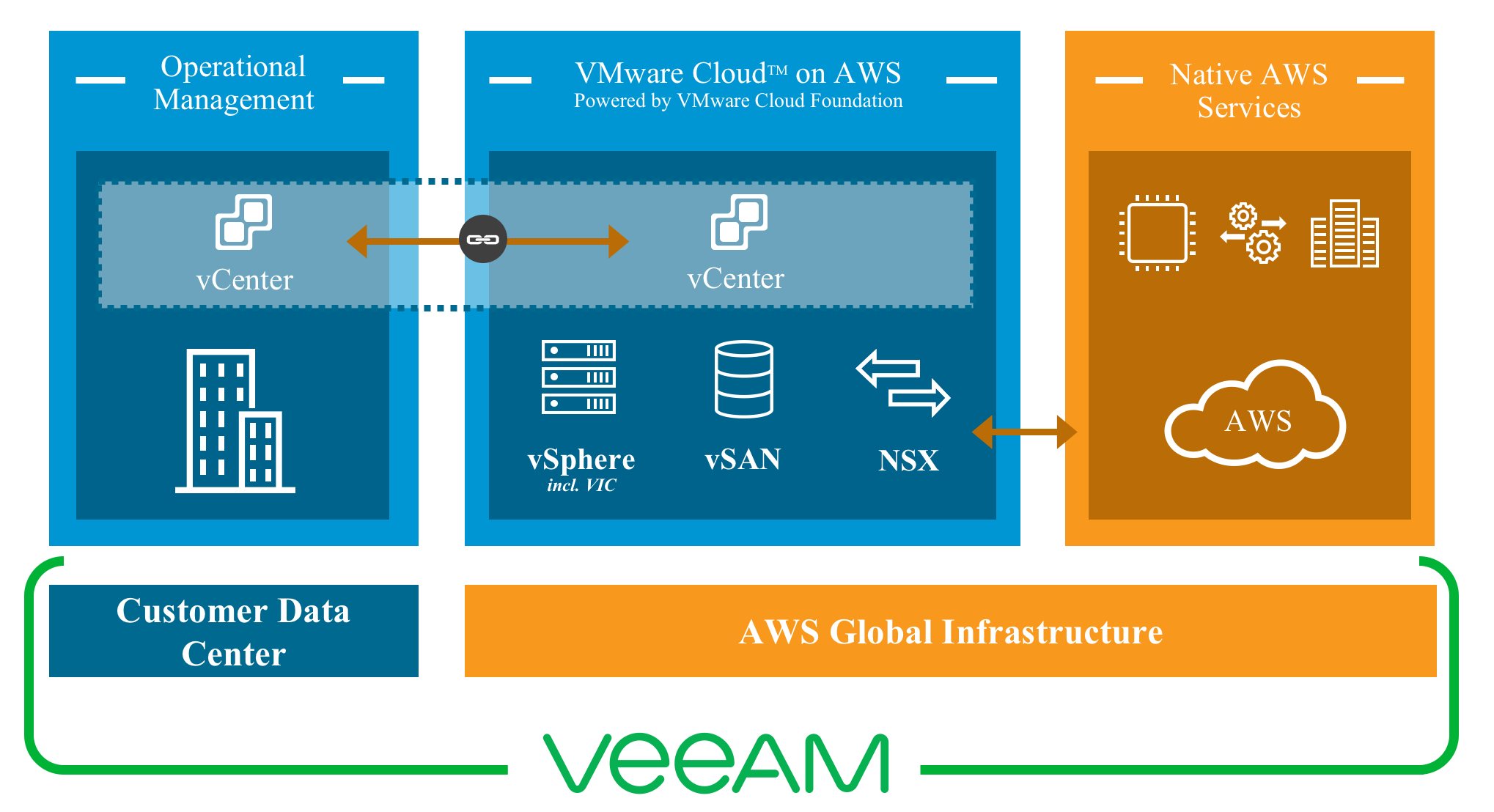
At VMworld 2018, myself and Michael Cade gave a session on automating and orchestrating Veeam on VMware Cloud on AWS . The premise of the session was to show...

VMworld 2018 has come and gone and after a couple of days recovery from the week that was, i’ve had time to reflect on what was a great week and an another g...

VMworld 2018 has come and gone and after a couple of days recovery from the week that was, i've had time to reflect on what was a great week and an another g...
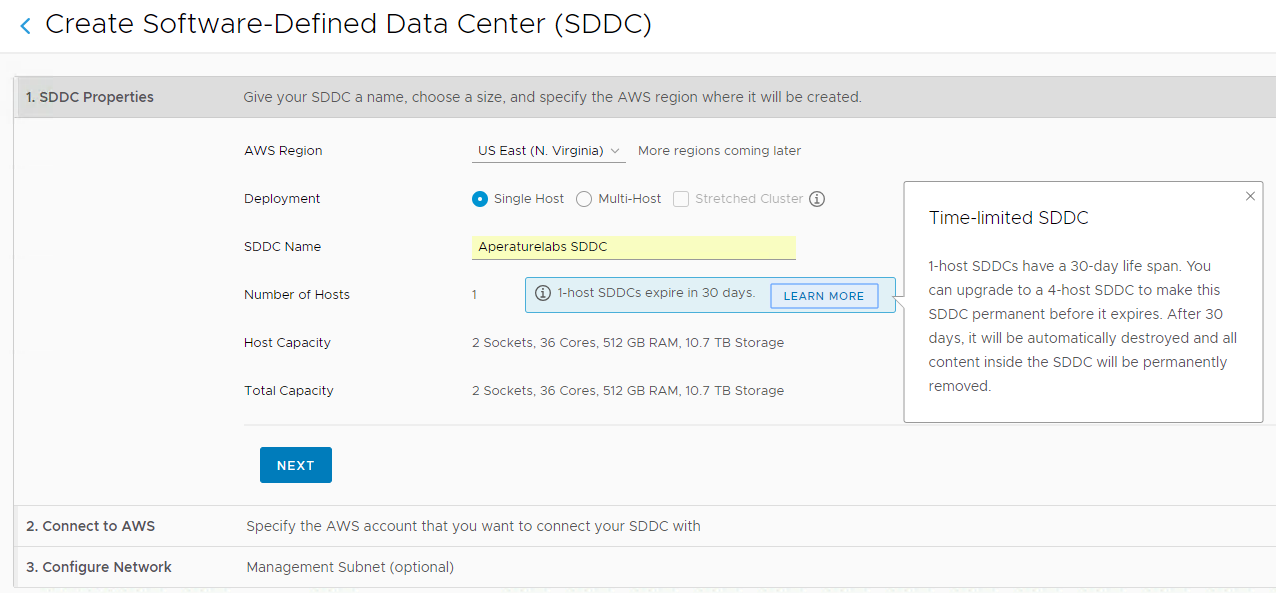
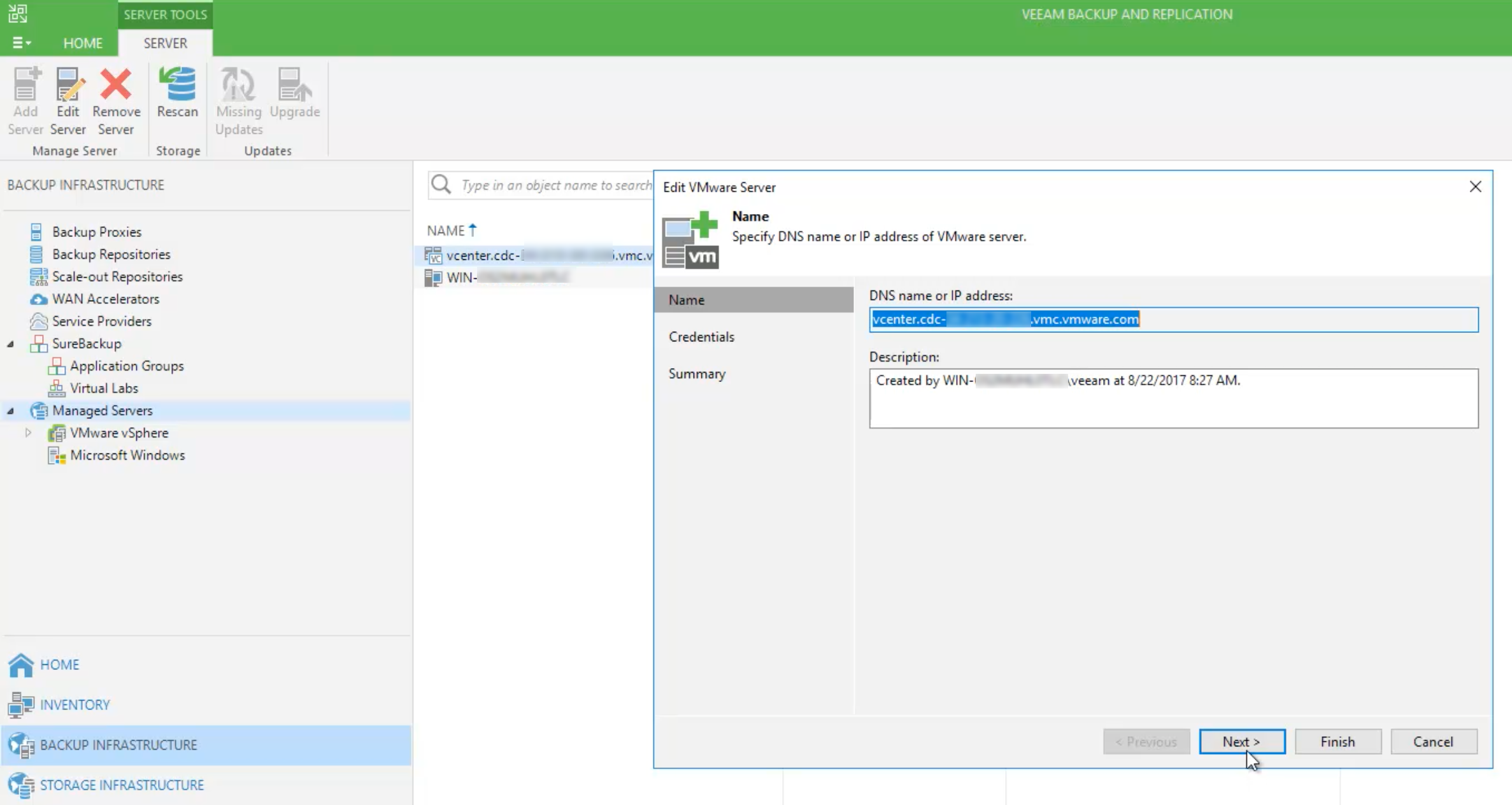
While preparing for my VMworld session with Michael Cade on automating and orchestrating the deployment of Veeam into VMware Cloud on AWS, we have been testi...
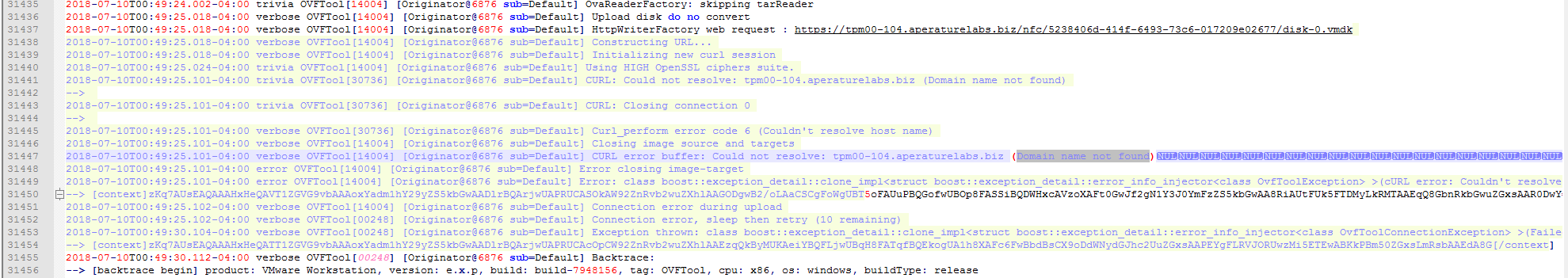
It's never an issue with DNS! Even when DNS looks right...it's still DNS! I came across an issue today trying to upgrade a 6.5 VCSA to 6.7. The new VCSA appl...
VMware has announced the general availability of vSAN 6.7 . As vSAN continues to grow, VMware are very buoyant about how it's performing in the market. With ...

After a longer than expected deliberation period the vExpert class of 2018 was announced late last Friday (US Time). I’ve been a vExpert since 2012 with 2018...
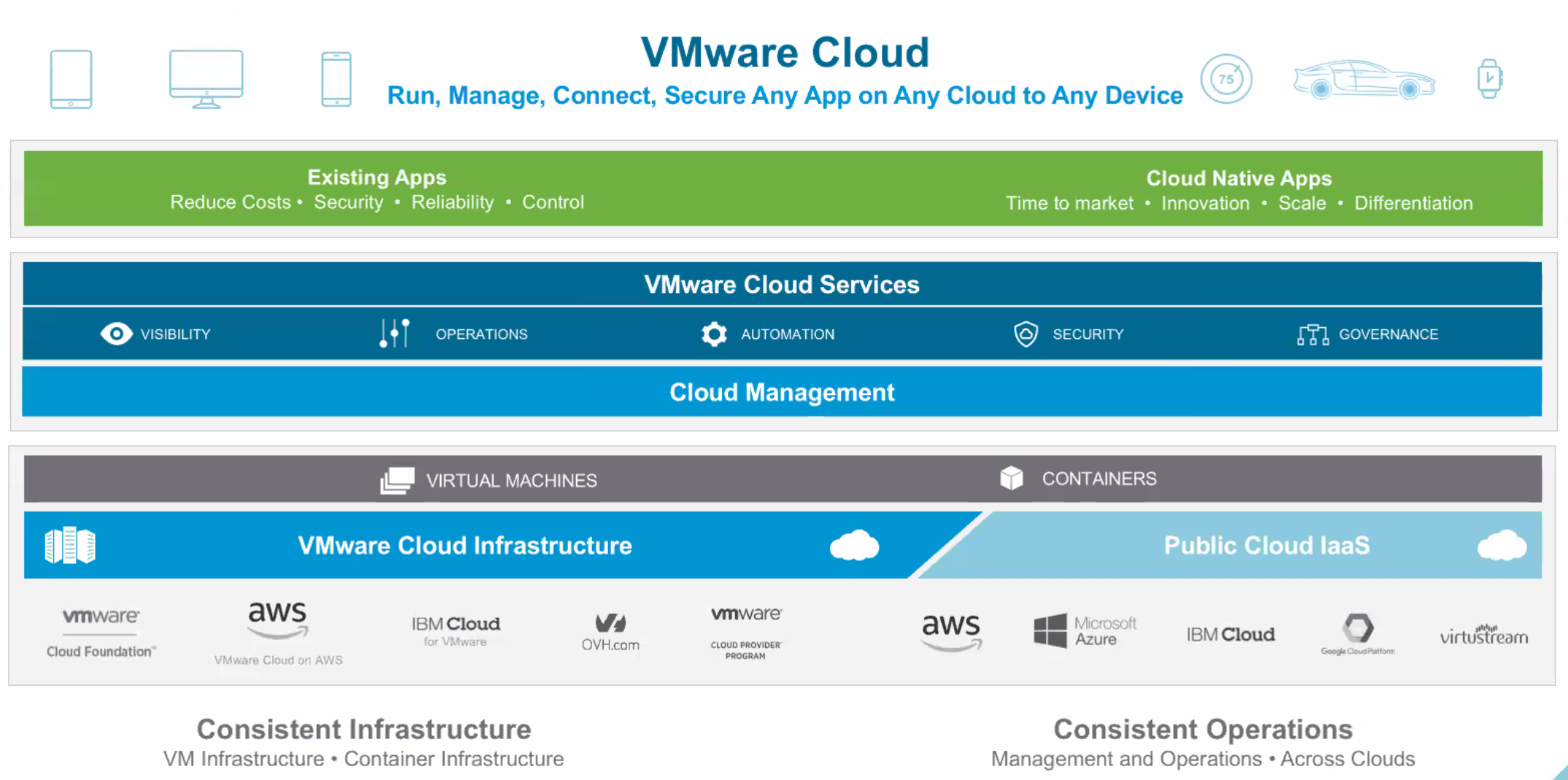
VMware has held it's first ever VMware Cloud Briefing today. This is an online, global event with an agenda featuring a keynote from Pat Gelsinger, new annou...
Runecast has released version 1.7 of their Analyzer today and it has added support for VMware vSAN. By using a number of resources within VMware’s knowledge ...
It’s been exactly a year since VMware announced their partnership with AWS and it’s no surprise that at this year’s VMworld the solution is front and center ...

A few months ago I was lucky enough to spend time with a couple of the founders of Runecast, Stanimir Markov and Ched Smokovic and got to know a little more ...

Everything to do with VMworld this year feels like it's earlier than in previous years. The call for papers opened in Feburary with session voting happening ...
Just after I joined Zettagrid in June of 2013 I decided to load up vSphere 5.1 Clustering Deepdive by Duncan Epping and Frank Denneman on my iPad to read on ...

I awoke this morning to the news that an announcement was made at DELL|EMC World that VMUG had been rolled into a the recently formed Dell Technologies User ...
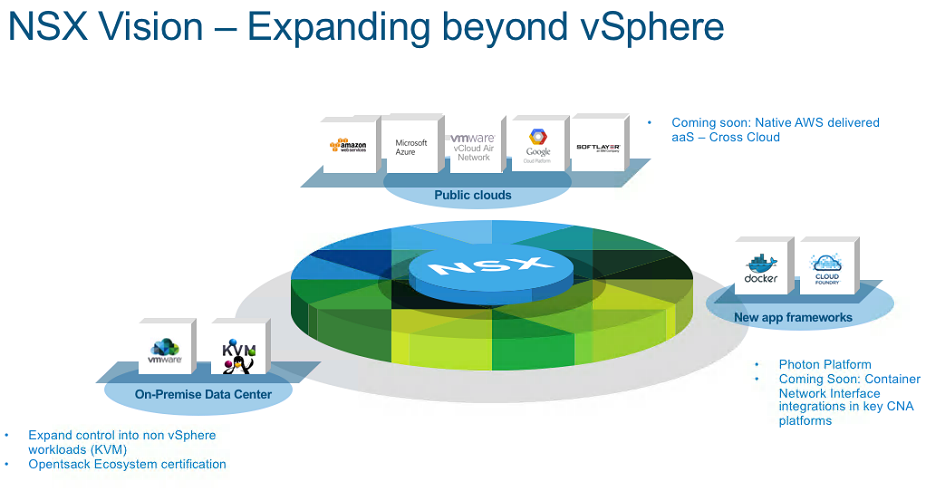
A couple of months ago in my NSX-v 6.3 and NSX-T 1.1 release post I focused around NSX-v features as that has become the mainstream version that most people ...

Last week I was in Sydney for the 2016 edition of vForumAU ...I've been coming to vForumAU since 2011 and this years event was probably up there with the bes...

About four years ago I was invited to join a program called the VMware vChampions...this program is run and operated by the VMware ANZ Channel and Marketing ...

Last week VMware and Amazon Web Services officially announced their new joint venture whereby VMware technology will be available to run as a service on AWS ...

Last week VMware and Amazon Web Services officially announced their new joint venture whereby VMware technology will be available to run as a service on AWS ...
[ UPDATE ] - VMware have released an official KB for the CBT issue. Sadly if you recognize the title of this post it's because this isn't the first time I've...

This is a quick post to alert Veeam users to an issue that was raised in the Veeam Community Forums yesterday...firstly if you are a Veeam customer and are n...
VMware is at an interesting place at this point in time...there is still no doubting that ESXi and vCenter are the market leaders in terms of Hypervisor Plat...
Why Veeam's software-driven, hardware agnostic approach makes sense for backups https://www.youtube.com/watch?v=hDBlTdzE6Us&t=8s Late last year I attended a ...
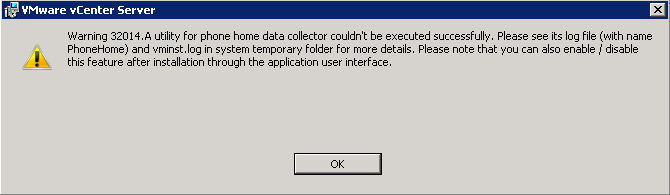
This week I've been upgrading vCenter in a couple of our labs and came across this issue during and after the upgrade of vCenter from 5.5 Update 2 to 5.5 Upd...
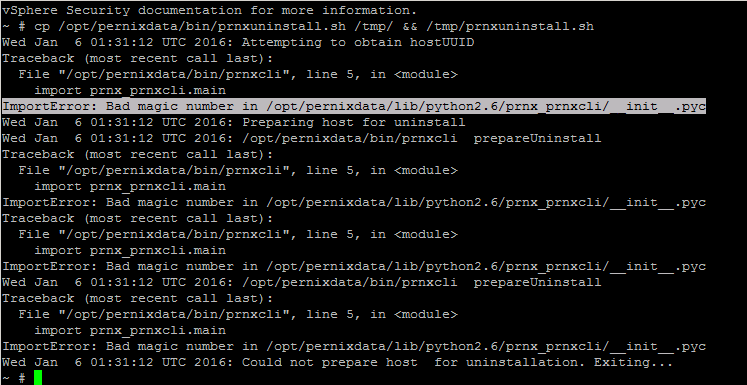
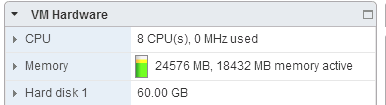
Came across an issue this morning trying to remove old 2.0 PernixData FVP Host Extensions from an ESXi 5.5 Update 3a Host. When running the uninstall script ...

Those that know me know that I am a very proud Australian of Maltese decent ...so when I was emailed a while back to see if I would review the beta for Altar...

Last week at VMworld we had the annual vExpert Reception…this year the party was held at the very swanky Julia Morgan Ballroom in the Merchants Exchange buil...
NSX for vSphere version 6.2 was made Generally Available earlier today and there has been some significant updates and improvements to the Network Virtualiza...
Rubrik is a company a lot of IT Professionals have been keeping an eye since release of their v1.0 Appliance back in May. Their industry DNA is extremely imp...
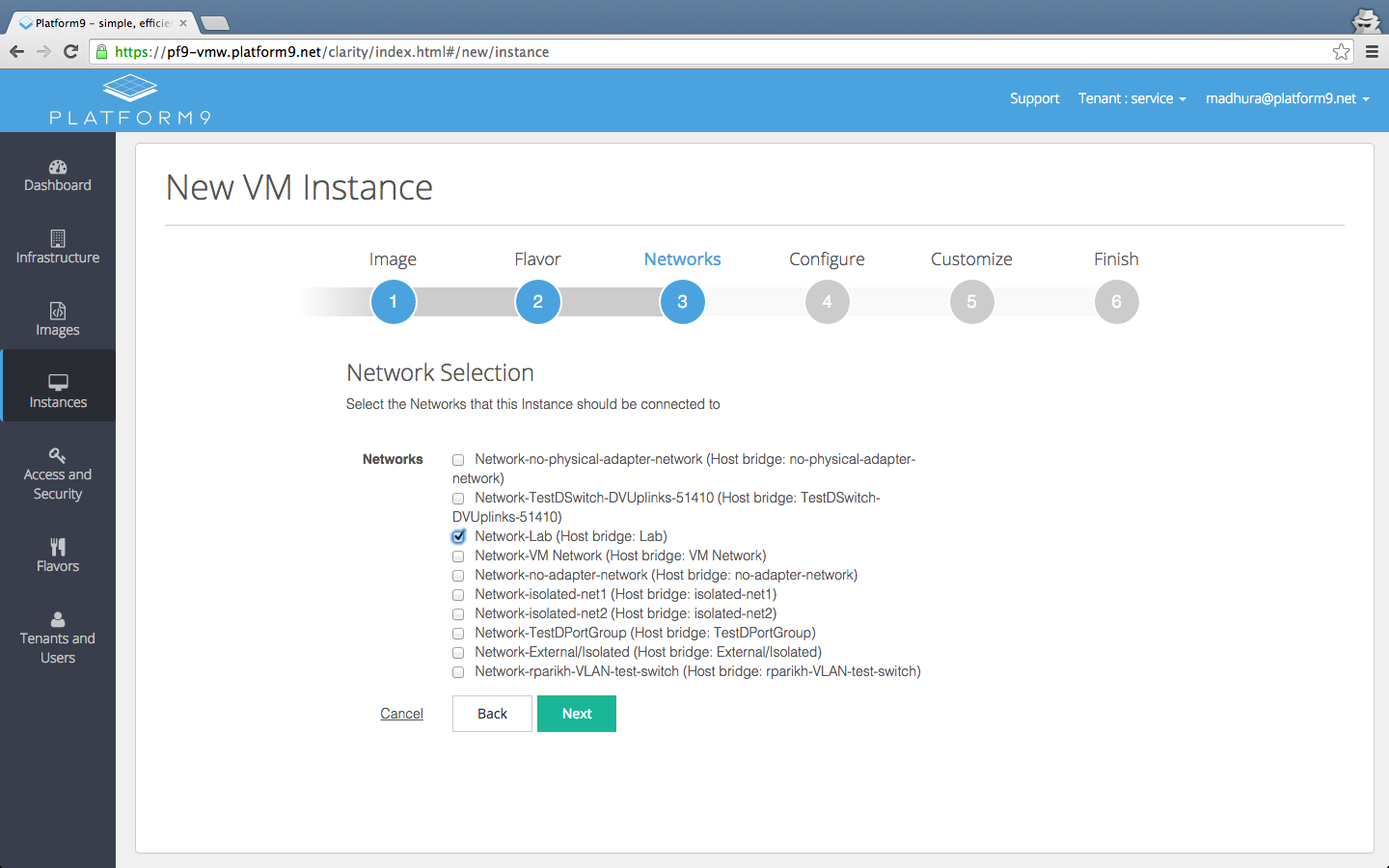
Today, Platform9 have announced the General Availability of their Managed OpenStack for VMware vSphere environments which adds to Platform9's ability to mana...

For those that are not aware, VMware has had their Lab Flings going for a number of years now and on the back of the latest release ( ESXi Embedded Host Clie...
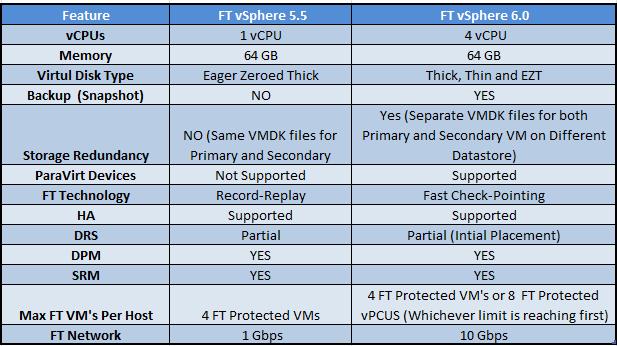
Today vSphere 6.0 was officially announced and will be GA in about 6-8 weeks...I've had limited time myself to tinker with the BETA in great depth, however I...
Late last year I was load testing against a new storage platform using both physical and nested ESXi hosts...at the time I noticed decreased network throughp...

Probably the biggest announcement from last week’s VMworld was the unveiling of the Project Marvin/Mystic as EVO:RAIL. Most of the focus on VMware releasing ...

The power of a service like CloudPhysics continues to grow almost weekly as they add new features and Cards. Not only is it brilliant for analytics and metri...
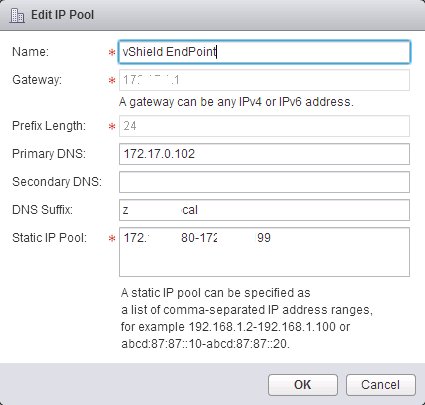
I recently had to deploy a solution into our Labs that required the installation of vShield Endpoint VMs to facilitate a 3rd Party service. No worries there....
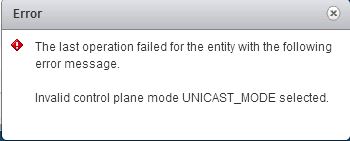
One of VMware NSX's best features is the ability to have the VXLAN Control Plane working in Unicast Mode...removing the requirement for Multicast traffic on ...
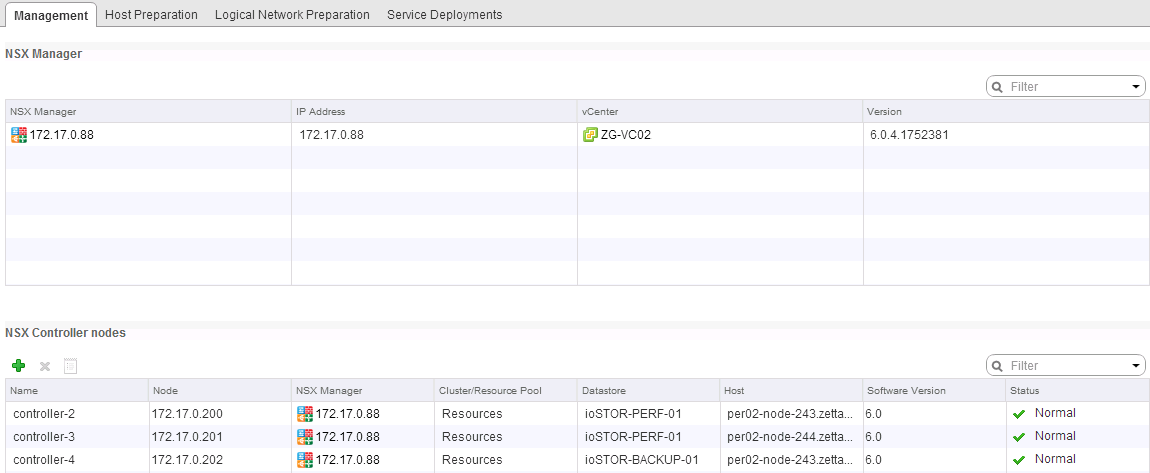
There are a lot of great posts already out there in regards to install and configuration of NSX. Rather than reinvent the wheel I've decided to do a series o...
About 7 weeks ago I wrote a post detailing my frustration at the way in which VMware's NSX was being trickled out into the market place and the hefty caveats...
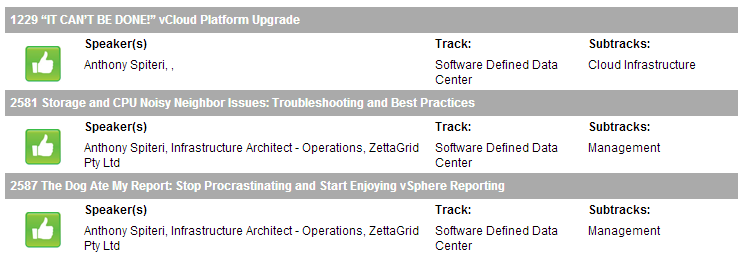
Voting is Open for VMWorld 2014 and I have submitted three sessions for your consideration. The first session is a VMUG User Conference Presentation I Co-Pre...
I'm a little frustrated! When VMware announced that their Network Virtualization acquisition Nicira (rebranded NSX) was officially GA at VMWorld 2013 most ha...
UPDATE : Looks like we will be seeing some VSPP Pricing for VSAN in Q2 vCenter and ESXi 5.5 Update 1 has reached GA, and we now have v1.0 of VSAN officially ...
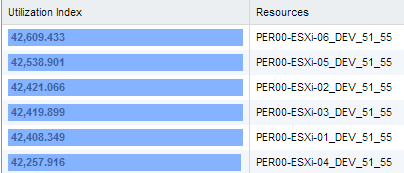
I've been lucky enough to have been early access to a new Card from the guys at CloudPhyics which, at it's core lets VMware admins quickly and precisely get ...
Over the last couple of weeks I've been fortunate to represent ZettaGrid, as a Platinum Sponsor of the VMware Series 2013 road shows in Melbourne and Sydney....
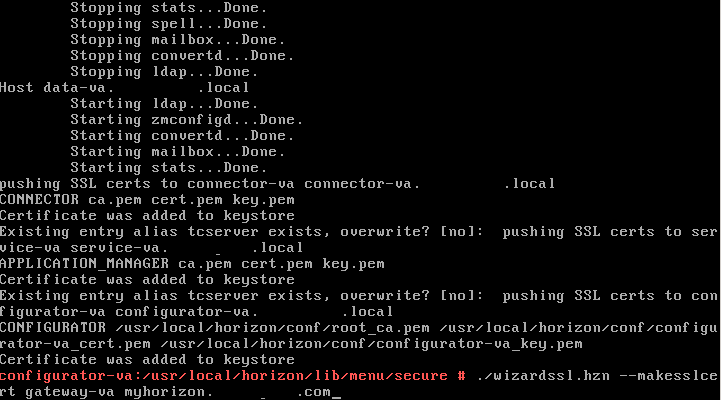
I came across this issue yesterday while trying to deploy a new instance on Horizon Workspace 1.0 in a POC environment. Having installed the vAPP a couple ti...
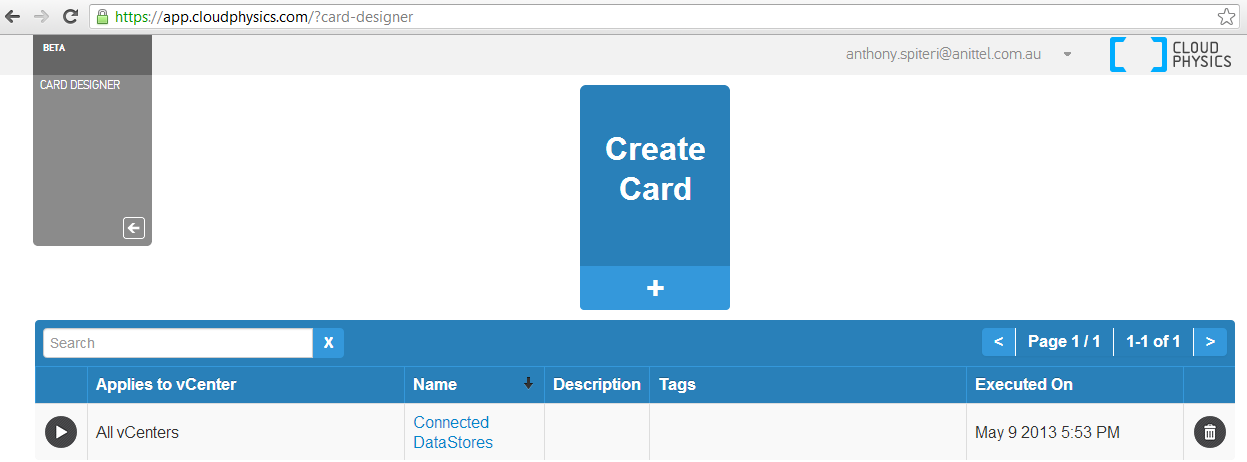
The boys at CloudPhysics are working hard behind the scenes at adding new features to their current stable of Analytic Cards based on data collected from t...
I was luckey to attend PEX at Australia Technology Park this week and thought I would share some of my take always. The venue was a little different to what ...
REMOVING DEAD PATHS IN ESX4.1 (version 5 guidance here ) Very quick post in relation to a slightly sticky situation I found myself in this afternoon. I was ...
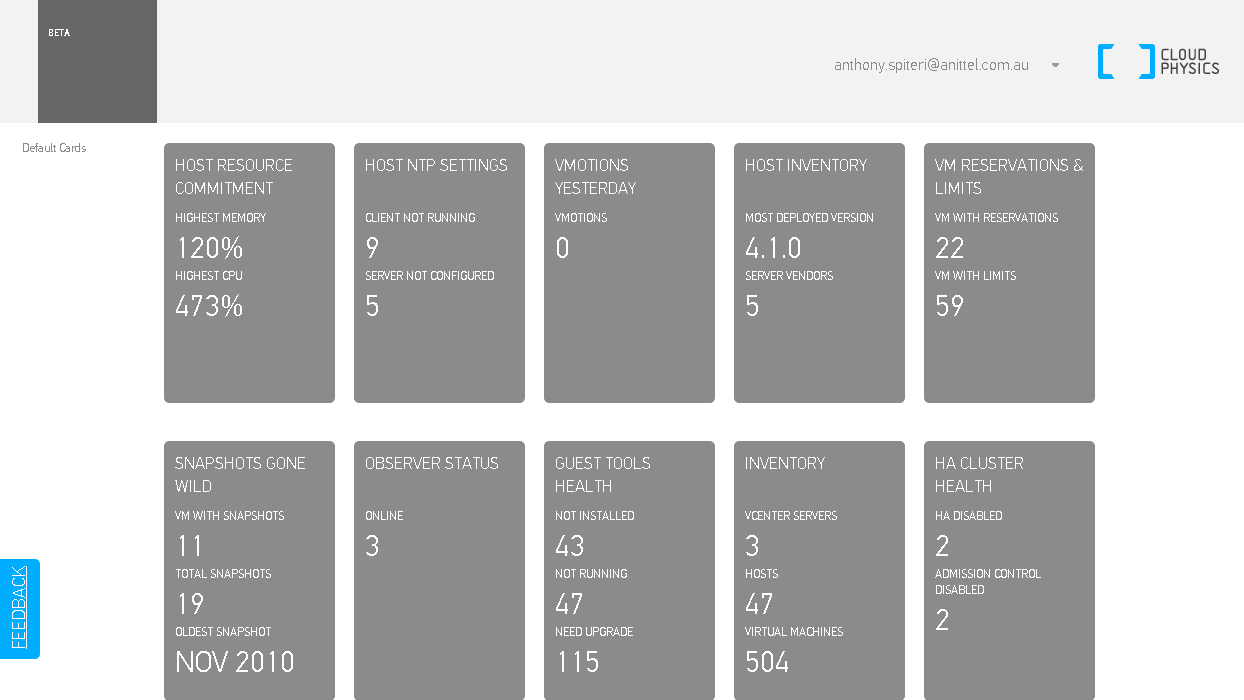
I first came across CloudPhysics just before VMWorld 2012. For a general overview, go here : I am a massive fan of analytics and trend metrics and I use a ...
A few years ago there was a theory put forward by a certain Apple CEO that we were entering the Post PC Era…while I have never subscribed to that theory (w...
There where some pretty big announcements and reveals at VMworld 2012, but unless I missed something (which was totally possible had any accouncement been ma...
If you had asked me 2 years ago that I'd be writing as a VMware vExpert I would have thought you were crazy. At that stage my only exposure to VMware was on ...