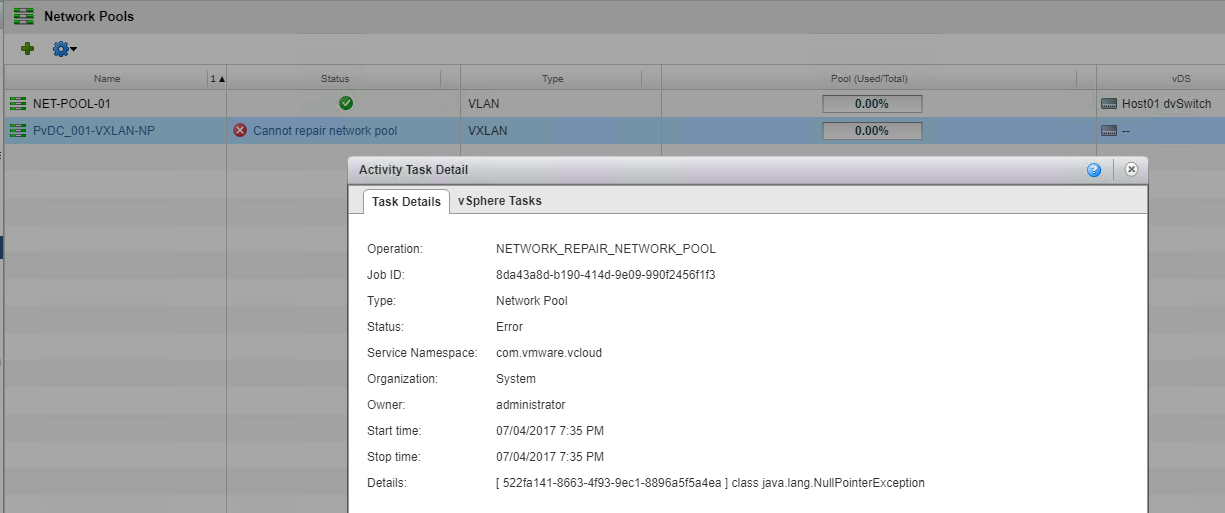
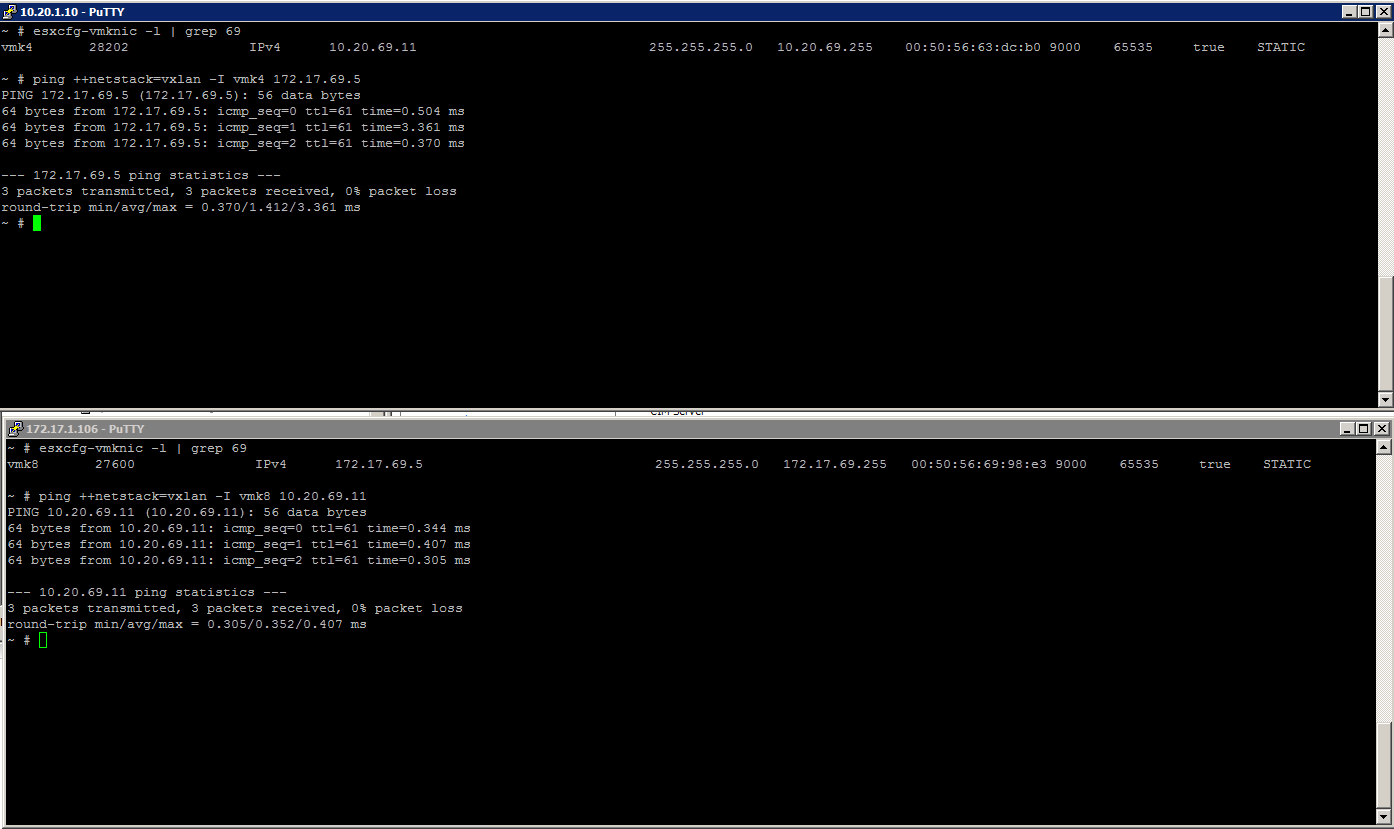
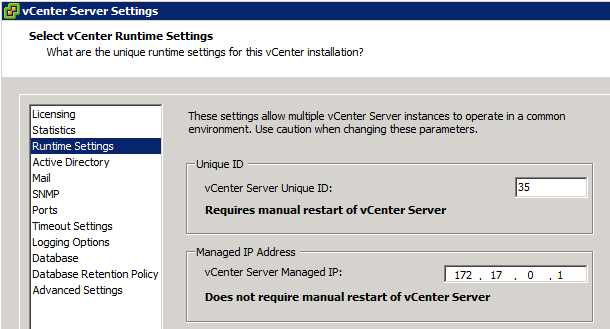
vCloud Director 9.0: Manual Quick fix for VXLAN Network Pool Error
vCloud Director 9.0, released last week has a bunch of new enhancements and a lot of those are focused around it's integration with NSX. Tom Fojta has a what...
Tag
4 posts
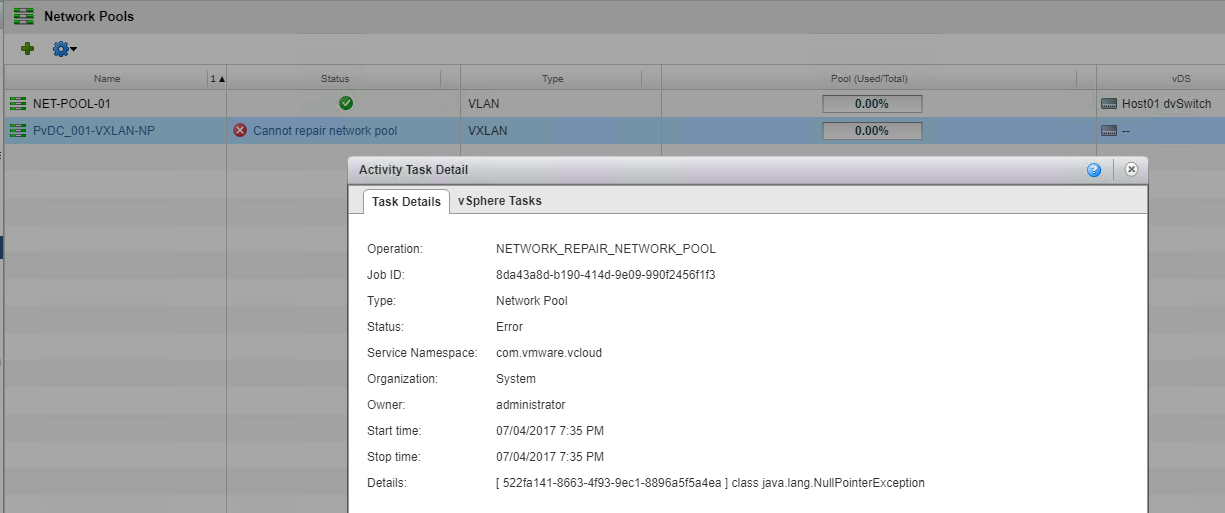
vCloud Director 9.0, released last week has a bunch of new enhancements and a lot of those are focused around it's integration with NSX. Tom Fojta has a what...
For the last couple of weeks we have had some intermittent issues where by ESXi network adapters have gone into a disconnected state requiring a host reboot ...
When working with NSX you have the option to create logical switches that are bound by Transport Zones...within those Transport Zones you could have a single...
This blog series extends my NSX Bytes Blog Posts to include a more detailed look at how to deploy NSX 6.1.x into an existing vCloud Director Environment. Ini...