The Anatomy of a vBlog Part 1: Building a Blogging Platform
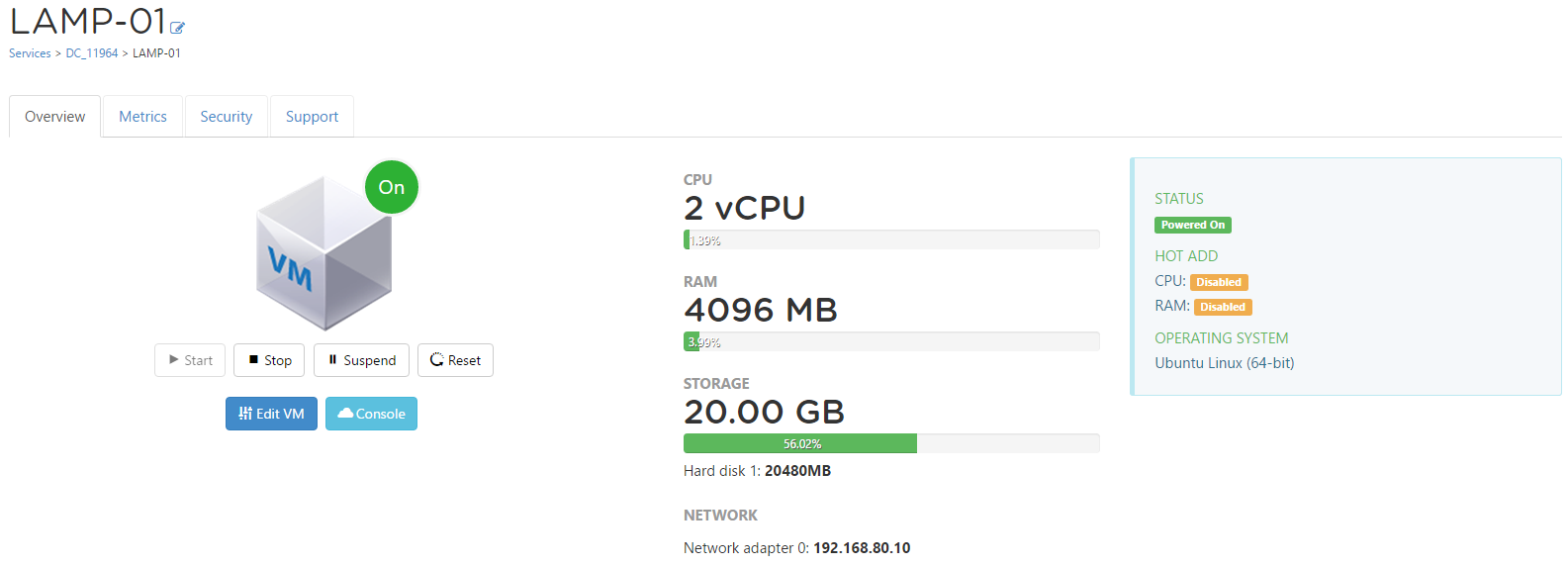
Earlier this week my good friend Matt Crape sent out a Tweet lamenting the fact that he was having issues uploading media to WordPress...shortly after that t...
Tag
8 posts
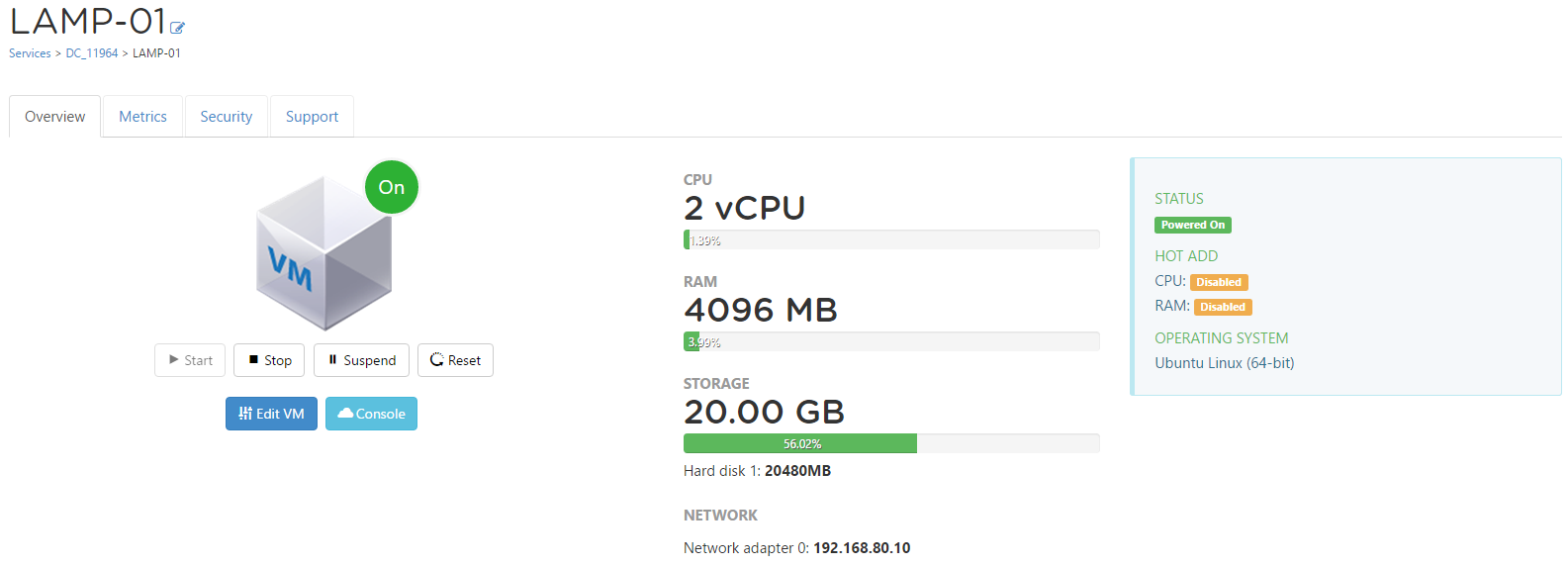
Earlier this week my good friend Matt Crape sent out a Tweet lamenting the fact that he was having issues uploading media to WordPress...shortly after that t...
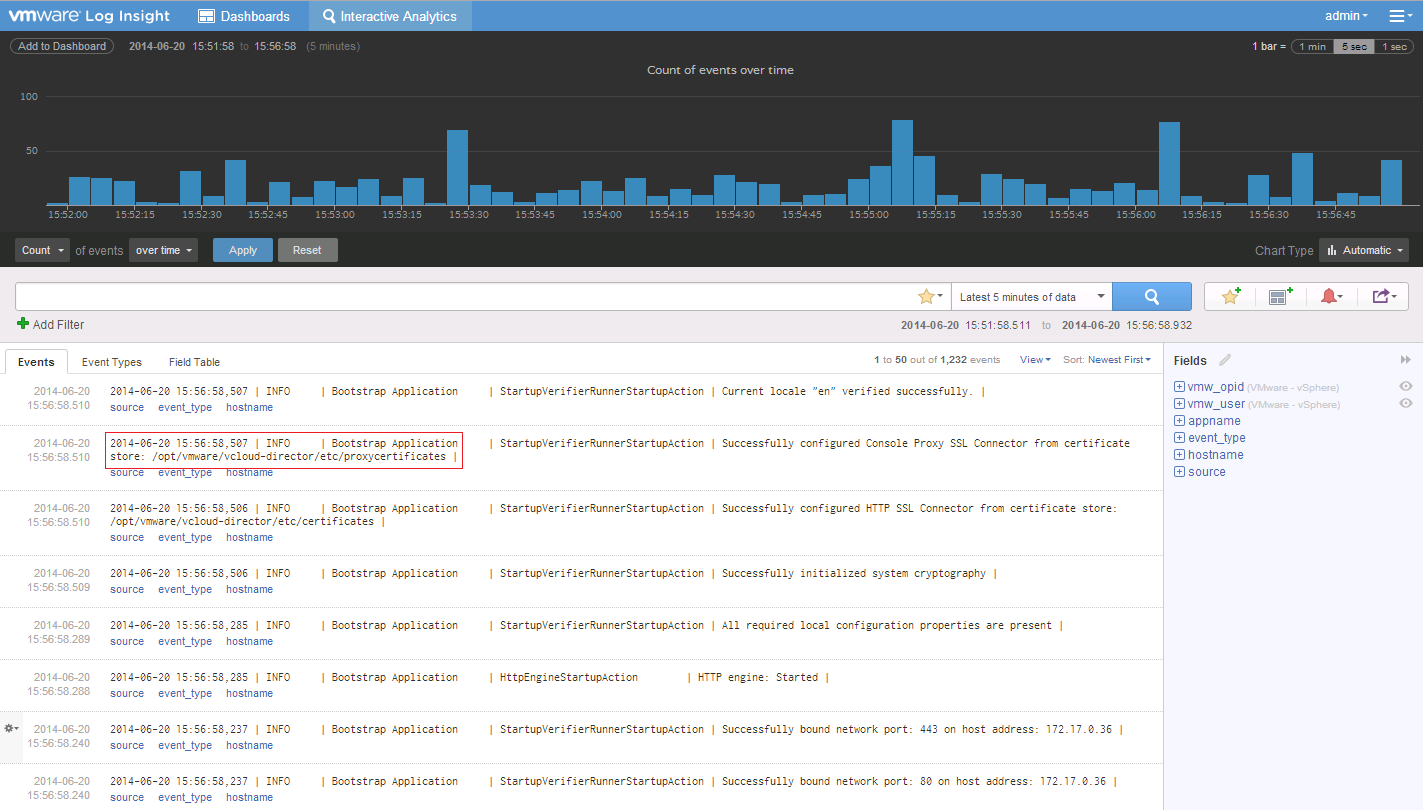
Recently v2.0 of VMware Log Insight became GA, and I've been playing around with it since it's release. Having been on the BETA of the 1.5 Version the 2.0 Ve...
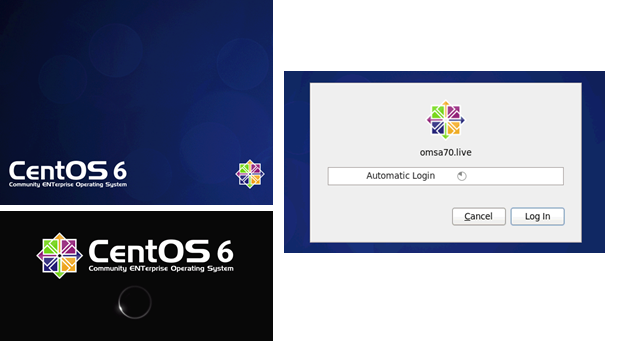
Here is a quick post on generating support logs for DELL cases if you are running VMware ESX(i) on any of the DELL server hardware. I had a CPU alert appear ...
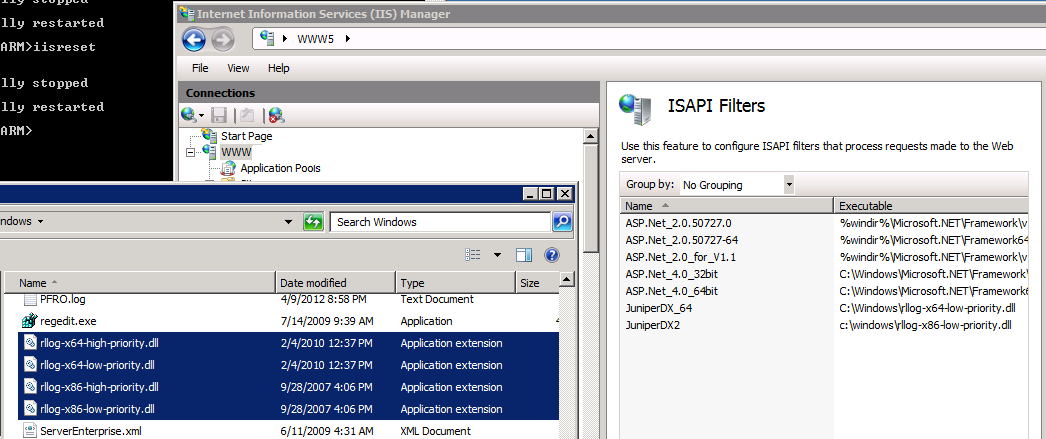
I had a request from a Hosting Client this week to look at options around blocking malicious users from causing trouble on a local Auction site. As the site ...
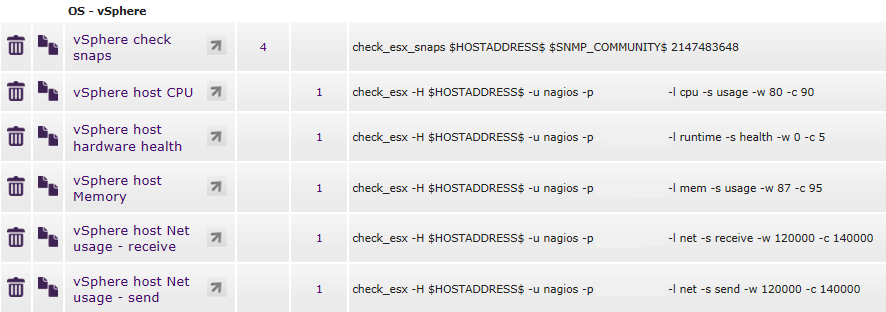
Unless my Google skills are seriously on the decline I wasn't able to find a definitive post on correctly setting up a nagios user to facilitate esx_chec...

The SSO Component of vCenter 5.1 throws a couple of spanners in the works with regards to a straight forward upgrade of an existing vCenter install. While no...
If you are NAT'ing public to private addresses with a load balancer in between your web server and your Gateway/FireWall device you might come across the sit...
A little after vCenter Operations Manager 5.0 went GA I posted this forum thread in regards to the default time-out value of the Web UI...Thanks to ILIO and ...