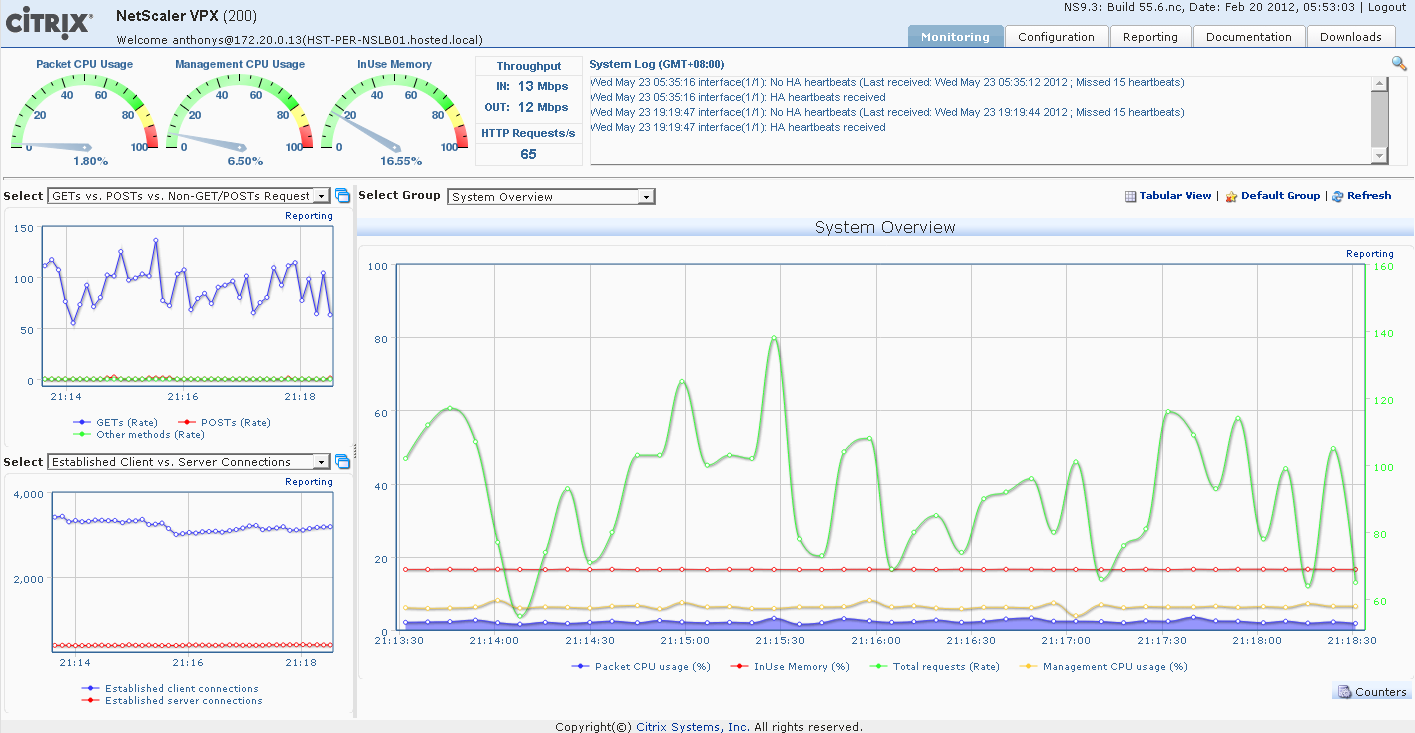
How-To: Citrix NetScaler GeoIP Restrictions
I had a request from a Hosting Client this week to look at options around blocking malicious users from causing trouble on a local Auction site. As the site ...
Tag
2 posts
I had a request from a Hosting Client this week to look at options around blocking malicious users from causing trouble on a local Auction site. As the site ...
Ive come across a couple of how-to's on configuring vCloud Cells in a highly available Load Balanced environment. There is a good overview here by @hany_mich...