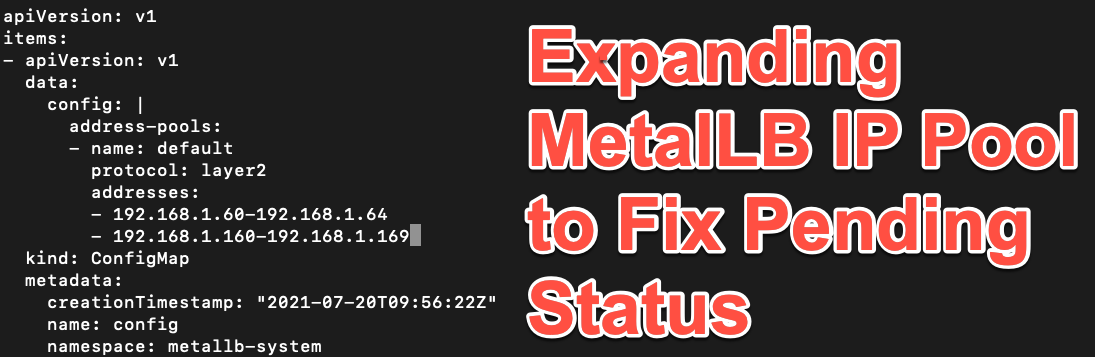
Quick Post: Quick Post: Expanding MetalLB IP Pool to Fix Pending Status
I've been using MetalLB for a while now in my Kubernetes Clusters and it's a great easy way to achieve high availability networking for service endpoints. Fo...
Category
13 posts
I've been using MetalLB for a while now in my Kubernetes Clusters and it's a great easy way to achieve high availability networking for service endpoints. Fo...
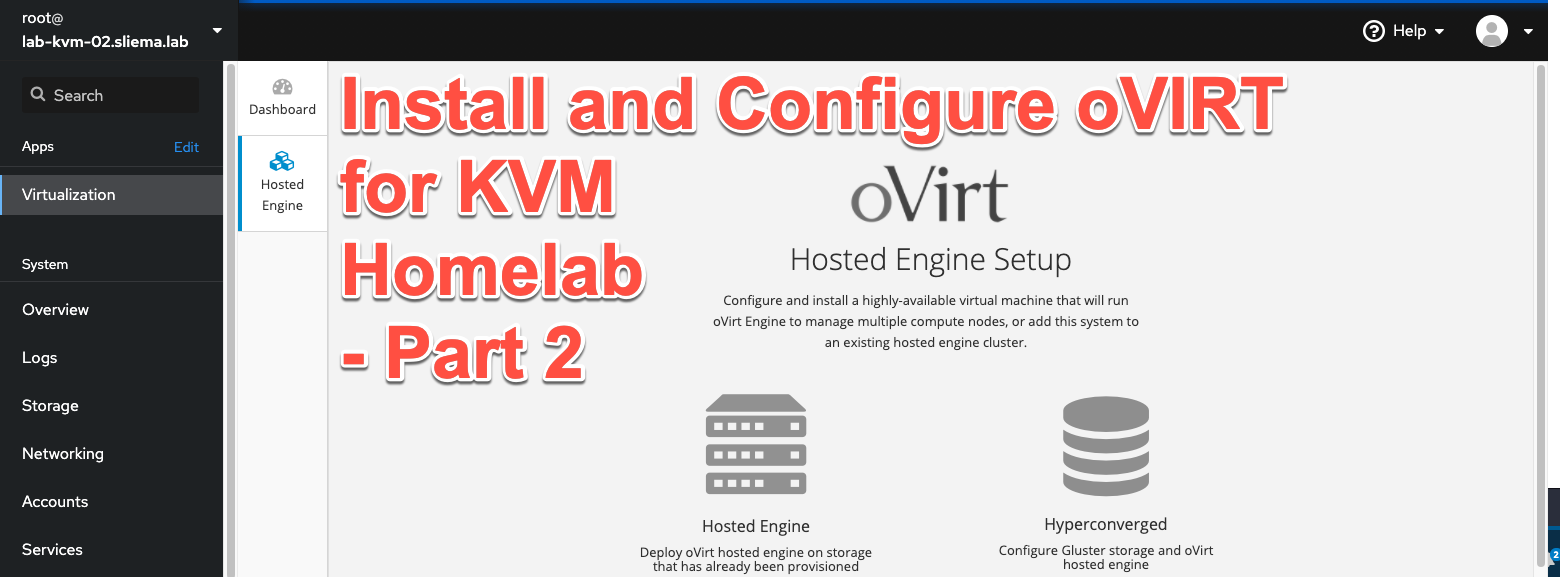
At VeeamON, we announced that Veeam would soon release Backup for RHV . In a subsequent post, I wrote down some of the observations I had seen over the past ...

It might be a surprise to some, but I have a tendency to be a bit of a Luddite when it comes to adopting new technologies around the home and office. Such wa...
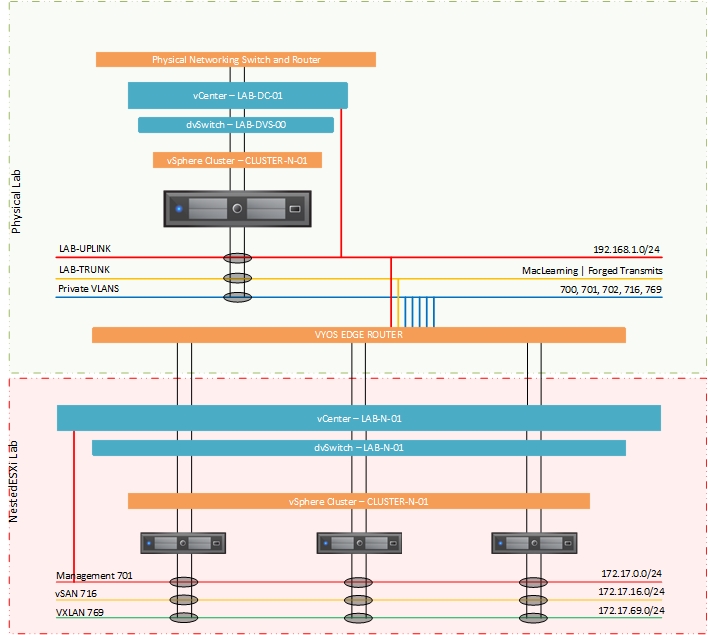
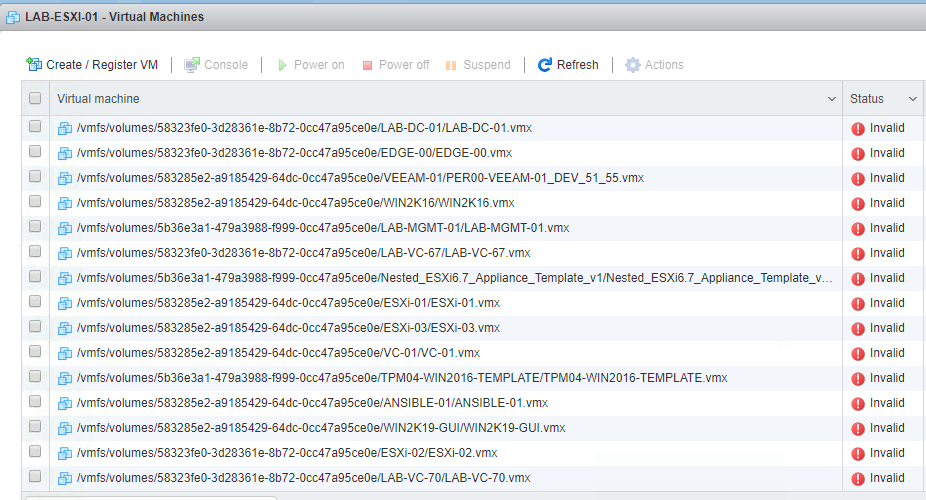
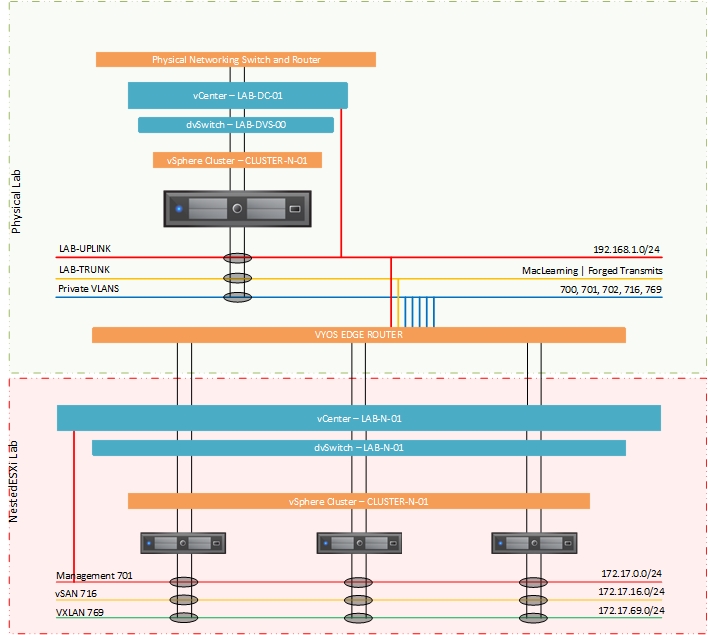
Back for part two of this look at how I went about configuring a single host for NestedESXi deployments. In the previous post I looks at the physical configu...
As usual, I like to jump right into software upgrades to test out new functionality (on none production systems of-course). With the GA of vSphere7 overnight...
I've should have written this article a long long time ago! In fact, i've been promising certain people that I would write this up for a number of years. The...

When it comes to connecting remote sites, branch offices or extending on-premises networks to the cloud that level of complexity has traditionally always bee...

For those that have been monitoring my Twitter posts over the past month of so, i've been hinting at some upcoming news around WireGuard and the research i'v...
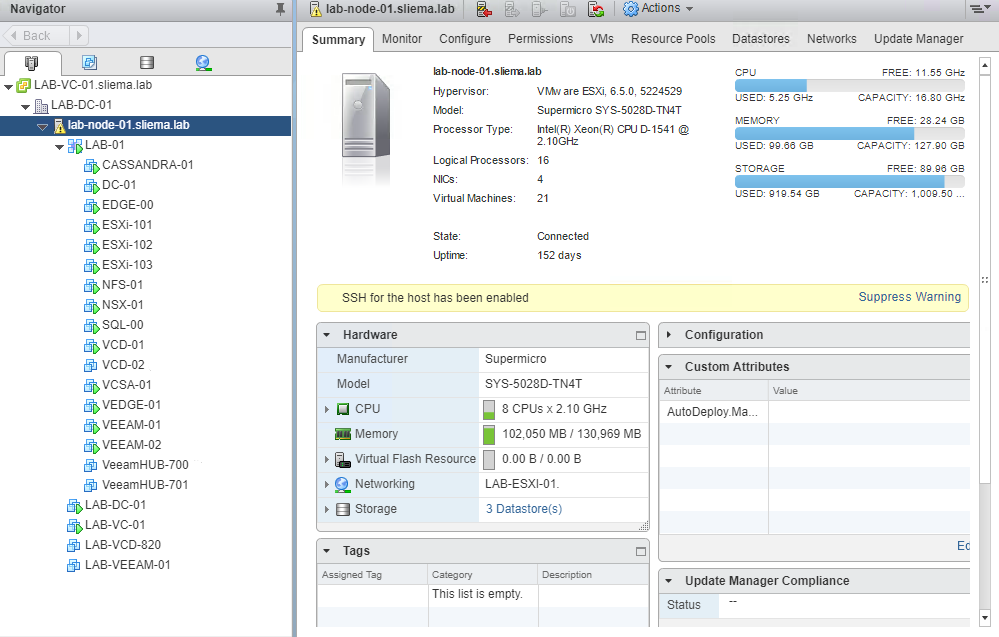
It's been just over a year since I unboxed my Supermicro 5028D-TNT4 and setup my new homelab. A year is a long time in computing so I though I would write up...
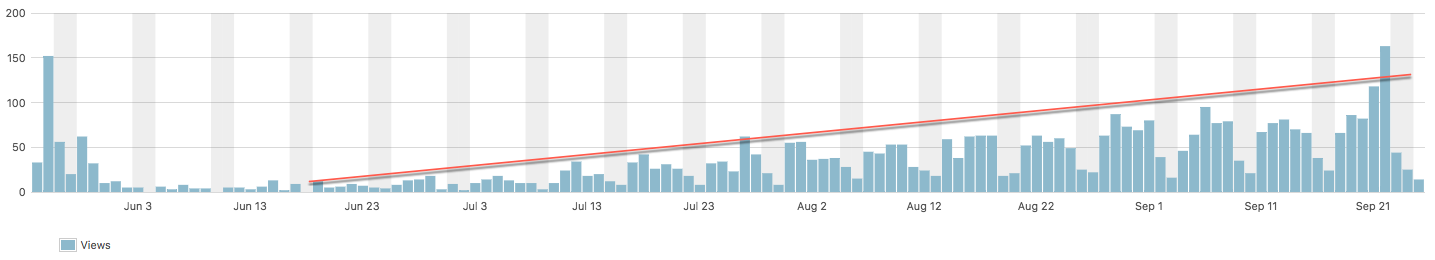
Over the past couple of months I noticed a trend in my top blog daily reporting...the Quick fix post on fixing a 503 Service Unavailable error was constantly...

A few weeks ago I wrote an article on how Veeam Powered Network can make accessing your homelab easy with it's straight forward approach to creating and conn...
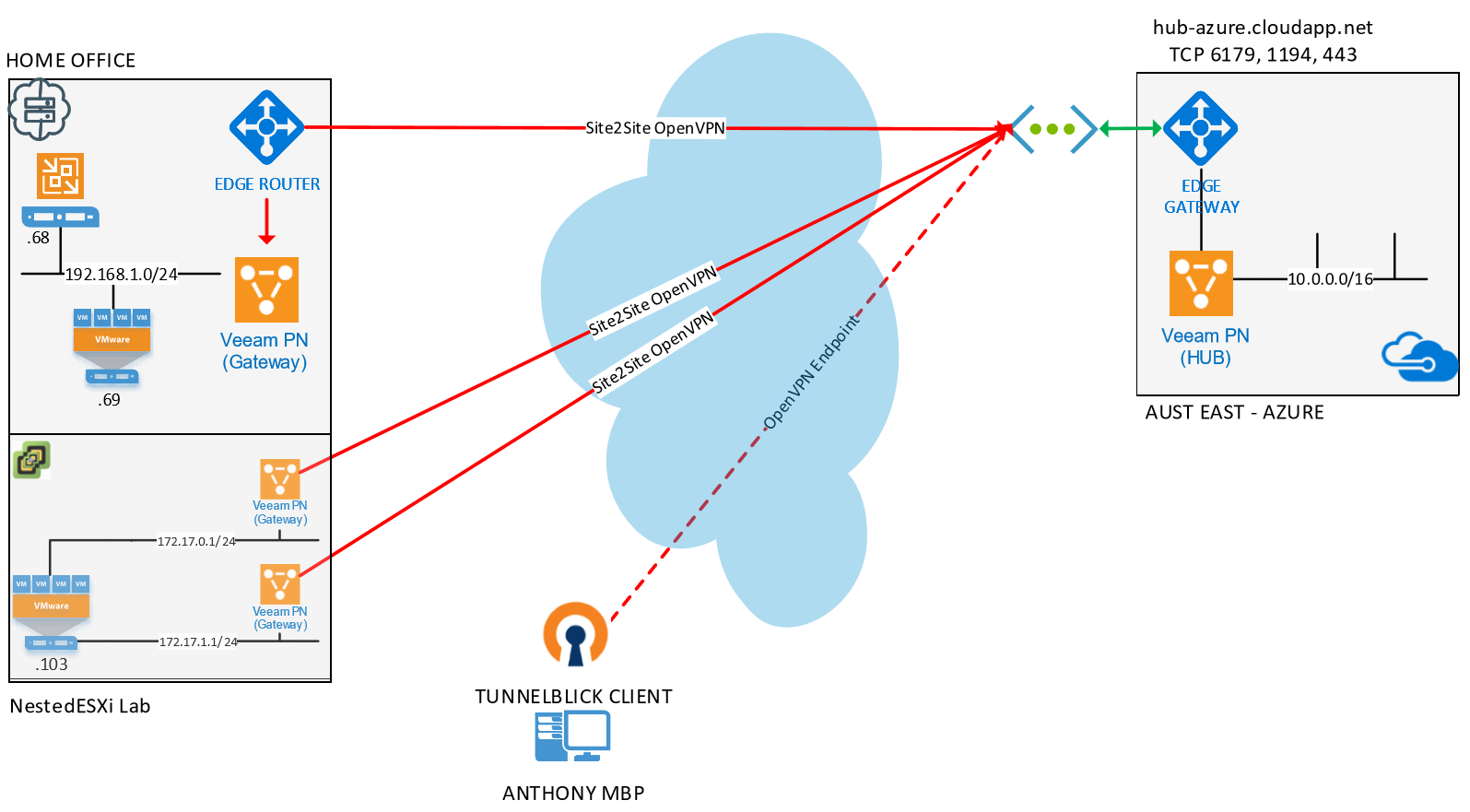
A couple of weeks ago at VeeamON we announced the RC of Veeam PN which is a lightweight SDN appliance that has been released for free . While the main messag...

While I was at Zettagrid I was lucky enough to have access to a couple of lab environments that where sourced from retired production components and I was ab...