
Real World Kubernetes - Working with .htaccess files for WordPress
Real word Kubernetes... that is a slightly tongue in cheek title however in reading through a lot of blogs and how-to's around Kubernetes, I never get a sens...
Tag
9 posts

Real word Kubernetes... that is a slightly tongue in cheek title however in reading through a lot of blogs and how-to's around Kubernetes, I never get a sens...
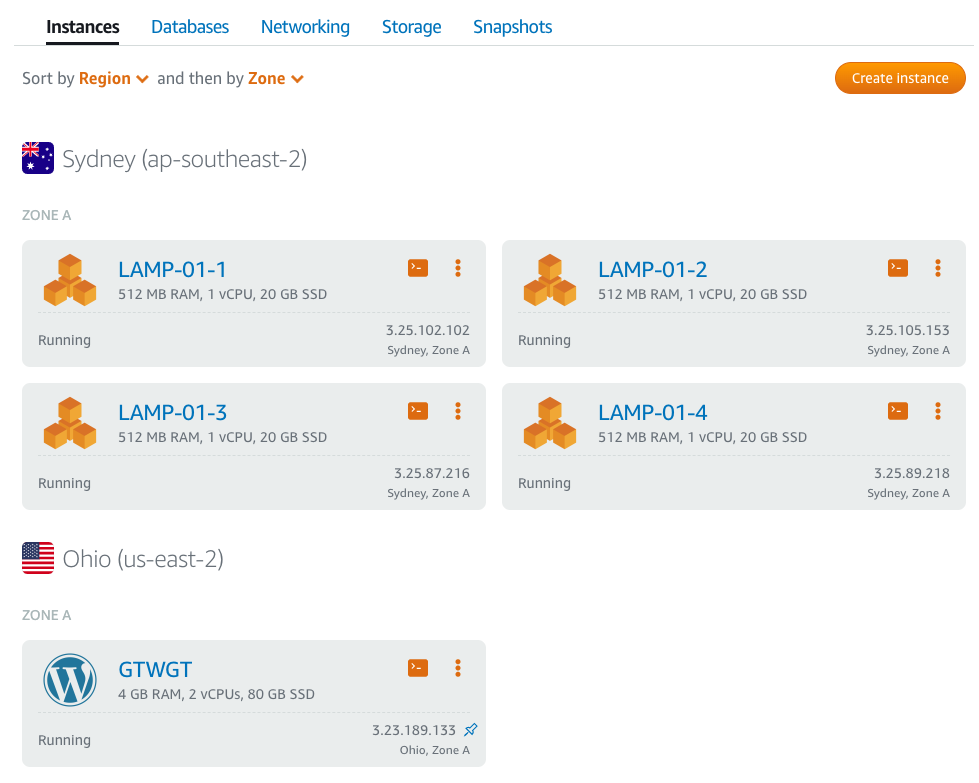
I've written before about how AWS offers complex simplicity when it comes to its plethora of service offerings. Without some education, the average user isn'...
I spent the last week on holiday in the Wine Region of Western Australia’s South West . I've been holidaying down south since I was a teenager and I've seen ...
During last weeks #APACVirtual Podcast ( Episode 70 – Engineers Anonymous pt1 – Engineer2PreSales ) the panelists (of which, I was one) where discussing...
Recently we have experienced a series of DDoS attacks against client hosted sites that resulted in varying level of service outages to hosted services across...
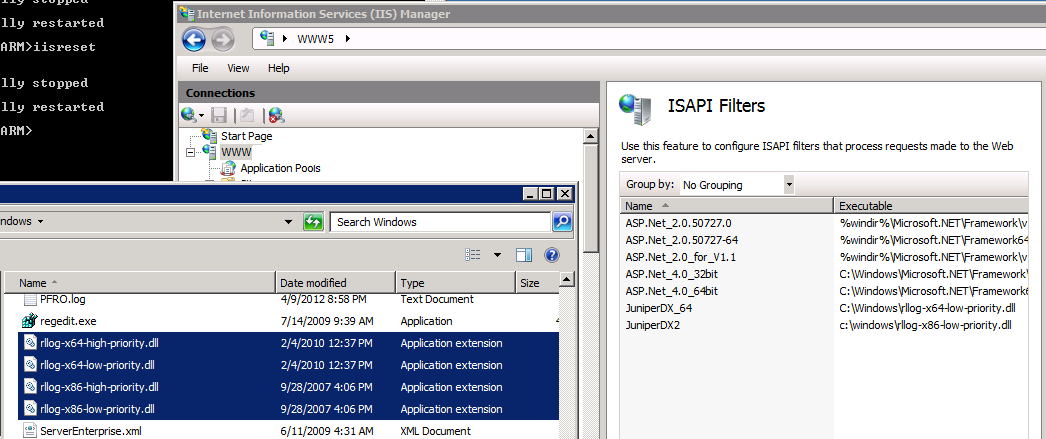
I had a request from a Hosting Client this week to look at options around blocking malicious users from causing trouble on a local Auction site. As the site ...
If you are NAT'ing public to private addresses with a load balancer in between your web server and your Gateway/FireWall device you might come across the sit...
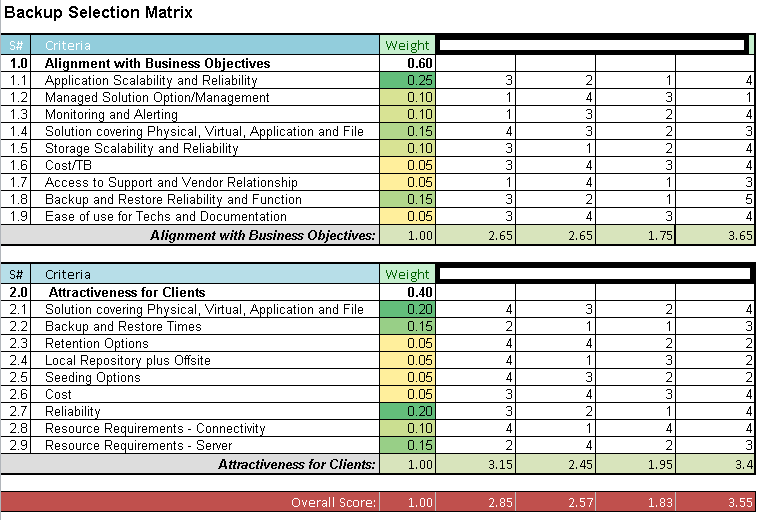
It's been a while since my first post on this topic, but there has certainly been a lot of thought and effort put into this subject since then. At first IÂ e...
If you had asked me 2 years ago that I'd be writing as a VMware vExpert I would have thought you were crazy. At that stage my only exposure to VMware was on ...