
Cirrus by Veeam: A Service Provider Technologists View
Those that know me and have followed my career understand that I've lived and breathed the Cloud and Service Provider space for more than twenty years. In th...
Category
62 posts

Those that know me and have followed my career understand that I've lived and breathed the Cloud and Service Provider space for more than twenty years. In th...
Last week, with the release of the RTM of Veeam Backup & Replication v12 we also released Veeam Service Provider Console v7 (7.0.0.12777) . Veeam continues f...
Today, Veeam made available to our VCSP partners the RTM of Veeam Backup & Replication 12 (Build 12.0.0.1402). It actually feels like it's been a while betwe...

There has been a shift of late to bare-metal cloud. The amount of companies popping up and starting to offer specialised services has risen in recent years a...

While at AWS re:Invent 2022 I had some great conversations with a mix of old and new Managed Service Providers who are focusing on delivering services for wo...
NOTE: The following content was transcribed and modified from the Thoughts on X podcast embedded above... Click Play if you would like to listen. Last week, ...
Last year, I got myself a little more involved in the world of Red Hat and general Linux Kernel based Virtualization. It had been a space that I had basicall...
Disaster Recovery with Veeam Cloud Connect Replication (VCCR) has been a passion of mine since I first saw it demoed at VeeamON 2015 by Luca Dell'Oca back wh...

With the release of Veeam Backup for Microsoft 365 v6 , we brought to market one of the most heavily requested features across all products at Veeam. That is...

Great news this week, with the GA release of Veeam Backup for Microsoft 365 (VBM) version 6.0 ( 6.0.0.367 ). This new version again builds on the 5.0 release...
Cloud Field Day 12 has come and gone...and for the third time virtually, I had the pleasure of presenting to the delegates. This time around it was the first...

This week, with the release of Veeam Backup & Replication v11a we also released Veeam Service Provider Console v6 (Latest build 6.0.0.7739) . Veeam remains f...
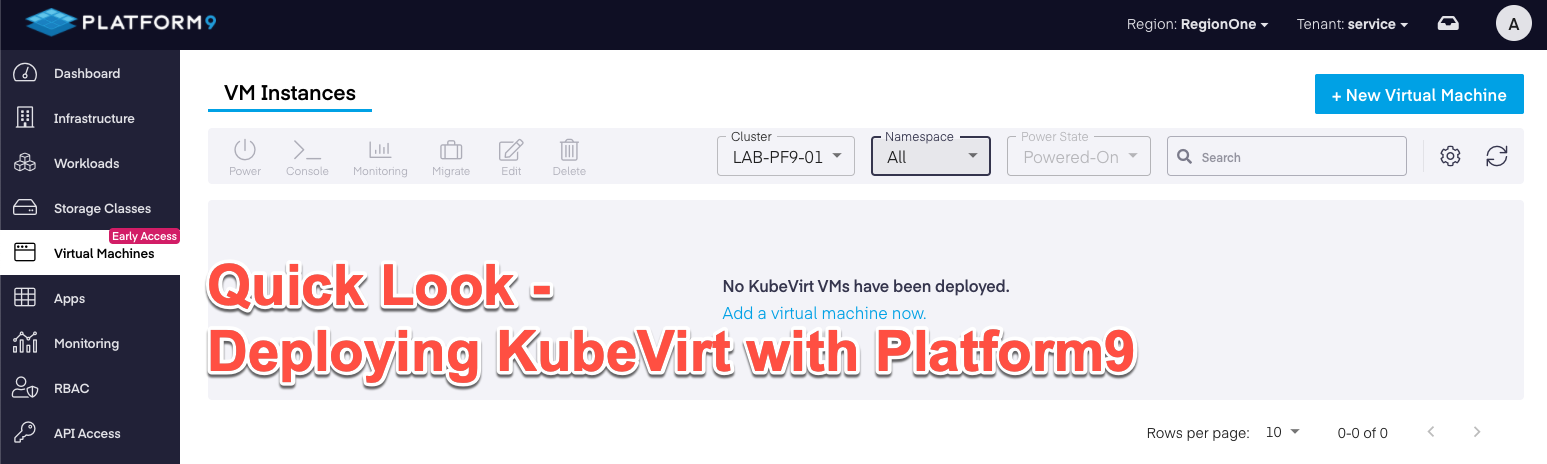
Last week I wrote an introductory post around KubeVirt giving some insight into were it sits in the current Kubernetes and Virtualization landscape. As menti...

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...
Though Kubernetes has made significant headways into being accepted as the way forward in terms of how modern applications are developed, deployed and manage...

At VeeamON 2021 we made a significant new product announcement which was the unveiling of Veeam Backup for Red Hat Virtualization. While this might not be th...

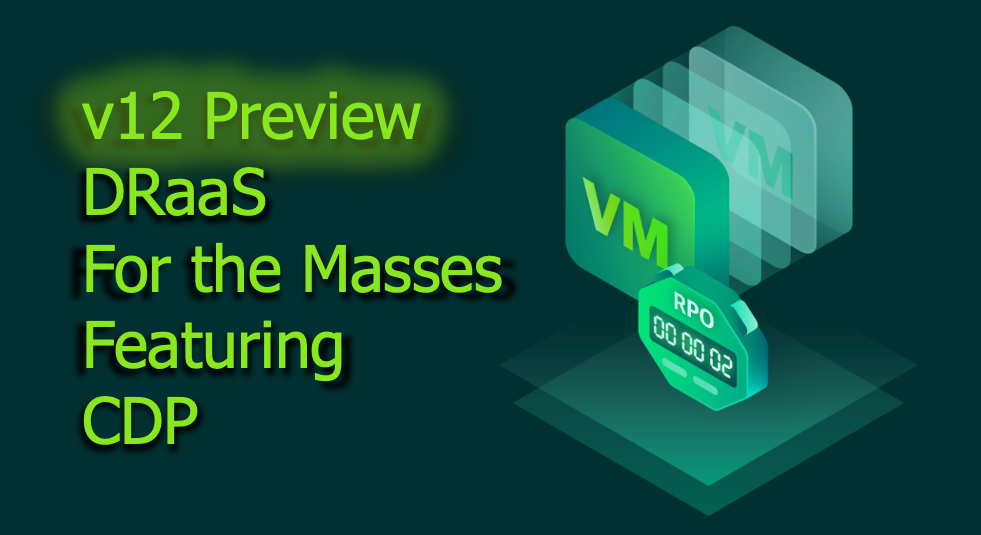
When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...
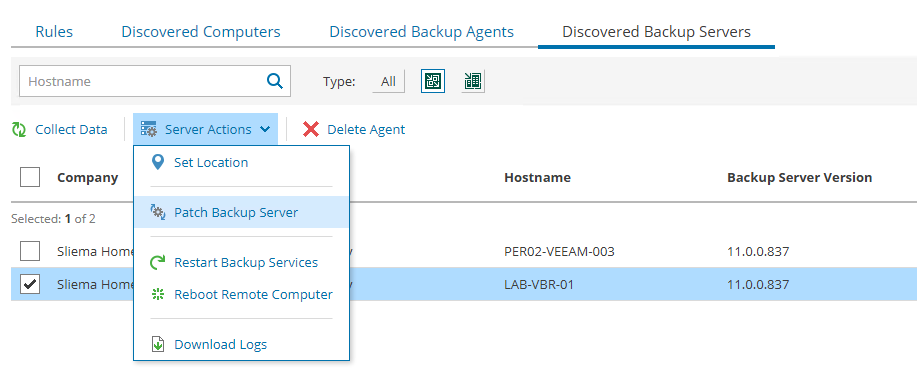
One of the cooler features to come out as part of the Veeam Service Provider Console (Console or VSPC) v5 is the ability to remotely patch Veeam Backup & Rep...

Before I joined Veeam I spent all my career working for service providers. I spent my first 7 years working for a hosting provider working on Windows and Lin...

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...

When Veeam Backup & Replication v11 went Generally Available on the 24th of February I posted the What’s in it for Service Providers blog. In that post I bri...
In early February we released the RTM Build of Backup & Replication v11 to our Cloud and Service Provider partners. This was to ensure that any keen early ad...
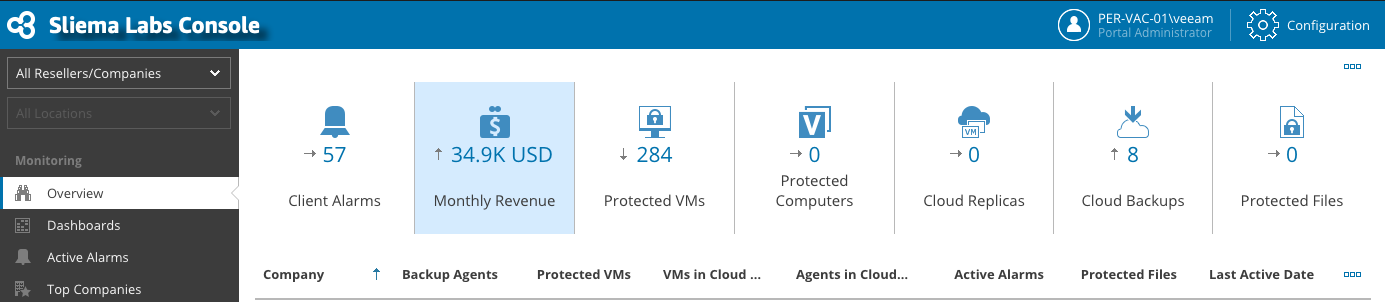
Last week, with the release of Veeam Backup & Replication v11 we also released Veeam Service Provider Console v5 (Latest build 5.0.0.6838) . Veeam remains fo...
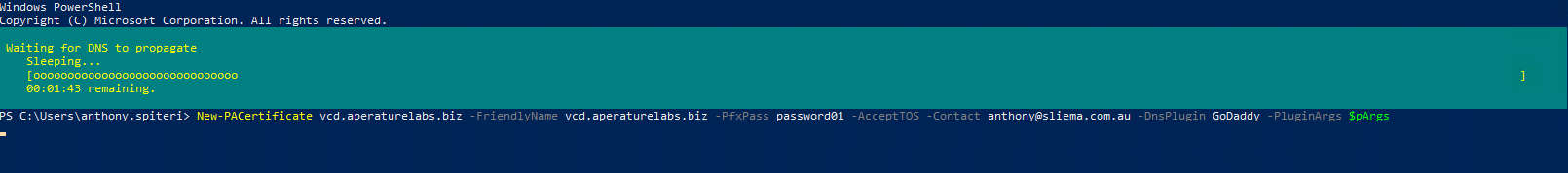
Lets Encrypt has issued over a billion SSL certificates since starting out and has all but ended any reason for not having trusted SSL certificates installed...

v11 was officially Launched and GA'ed last week meaning customers could get their hands on the next flagship release of Veeam Backup & Replication. Since the...
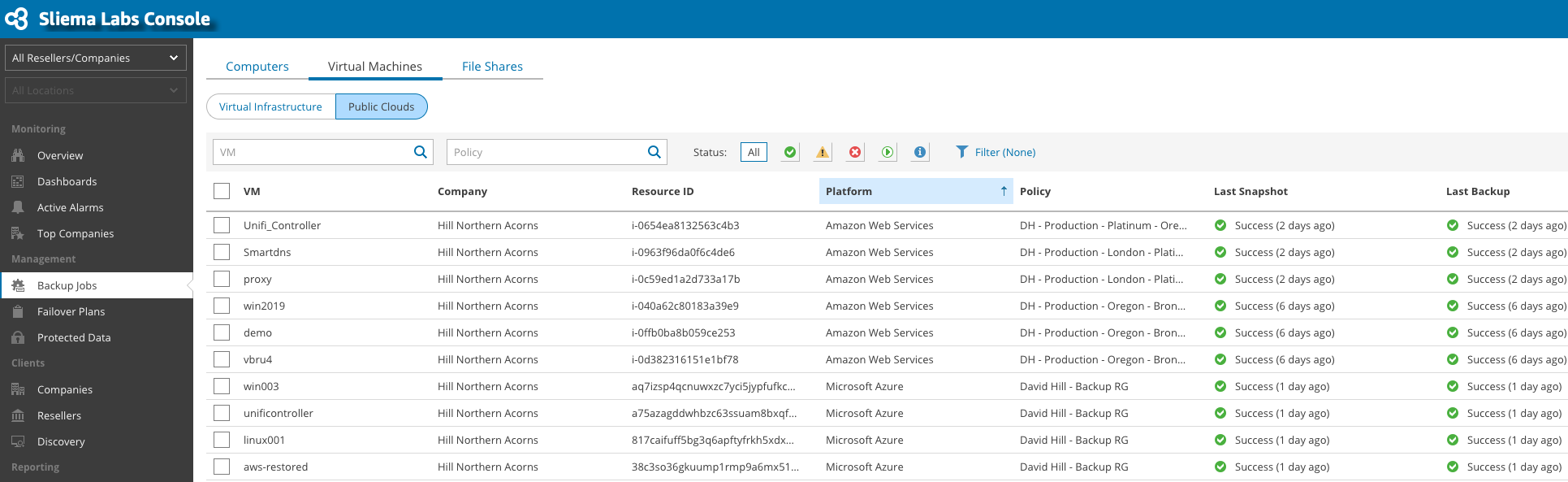
Last week the RTM of Veeam Backup & Replication v11 was released. With it also came the RTM of Veeam Service Provider Console v5. I wanted to give a quick ov...
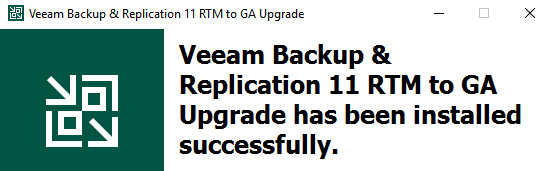
Overnight, Veeam made available to our VCSP partners the RTM of Veeam Backup & Replication 11 (Build 11.0.0.825). Seems like only yesterday v10 was released,...

It is crazy to think that we could celebrate (those of us brave enough to admit it) the birthday of the piece of software. Throughout modern history, softwar...
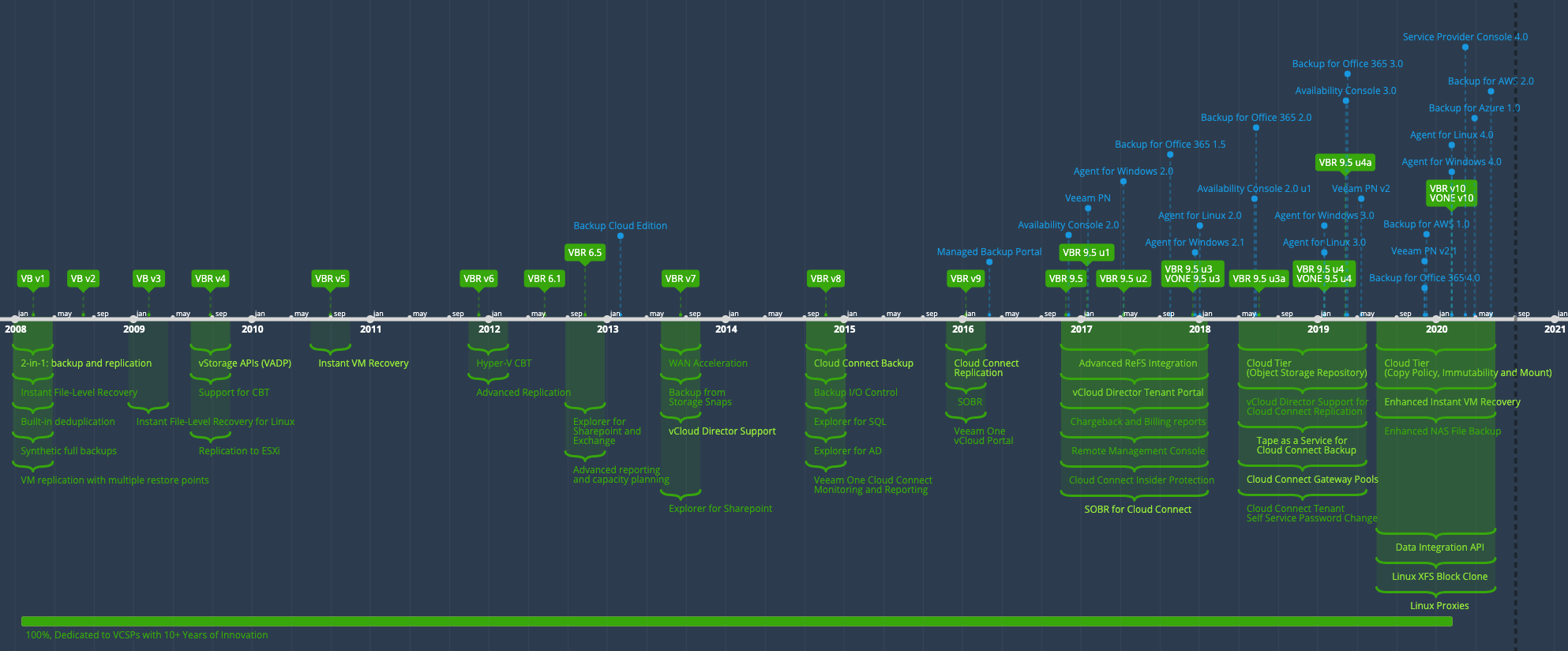
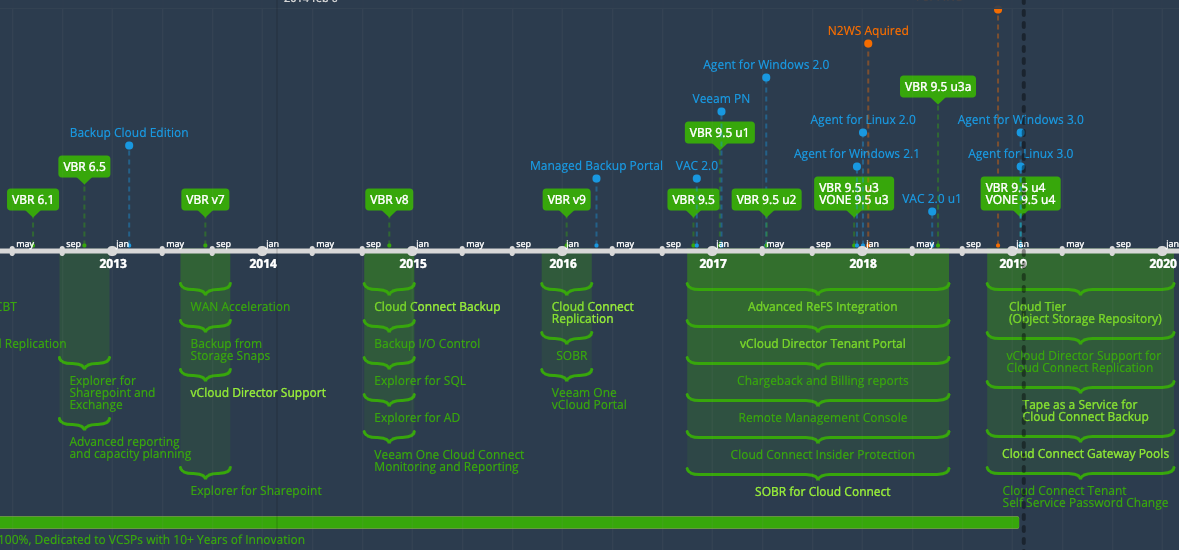
Hard to believe that I've been using Veeam for over ten years now! This blog has been testament to how Veeam has always been close to Cloud and Service Provi...
In todays application centric world, upgrading software has almost become a non-event. We have gotten used to instant upgrades that just work without having ...
Today, Veeam made available Patch 2 for Veeam Backup & Replication 10 ( Build 10.0.0.461 P2 ). This is the second cumulative patch for v10 and contains a num...
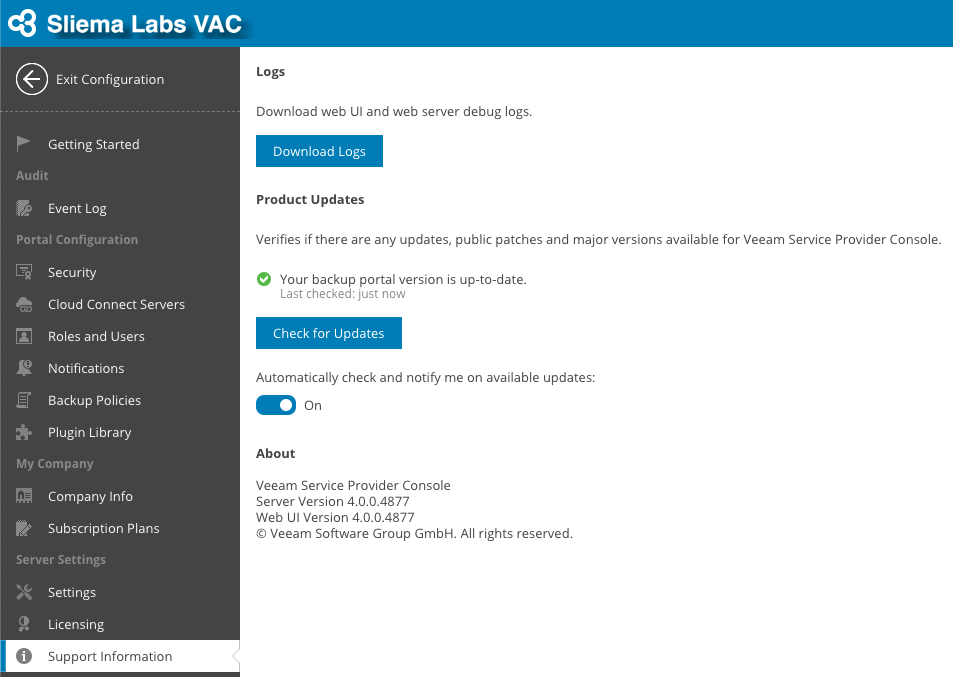
Last week, Veeam Availability Console v4 (4.0.0.4877) was released . With this major update, The Veeam Availability Console is now the Veeam Service Provider...

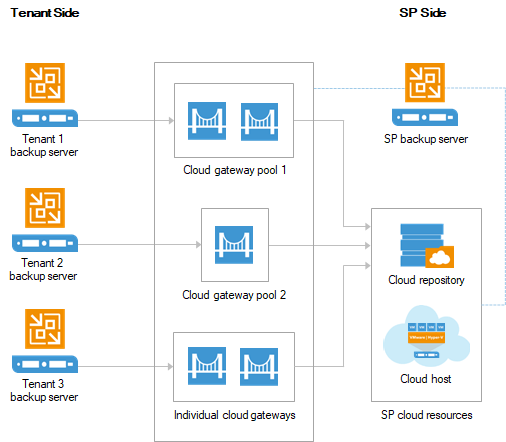
For more than ten years Veeam has supported our service provider partners by delivering industry-leading, innovative features that allows them to build servi...
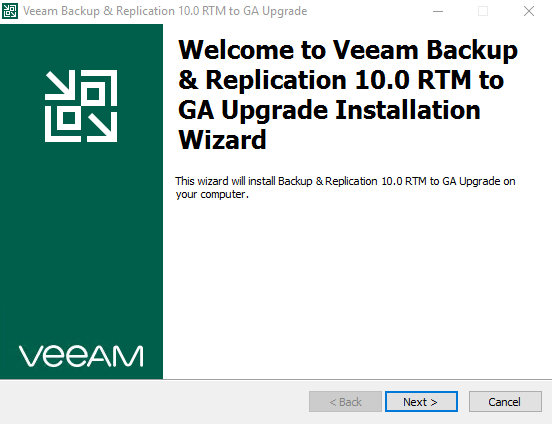
In early Feburary we released the RTM Build of Backup & Replication v10 to our Cloud and Service Provider partners. This was to ensure that any keen early ad...
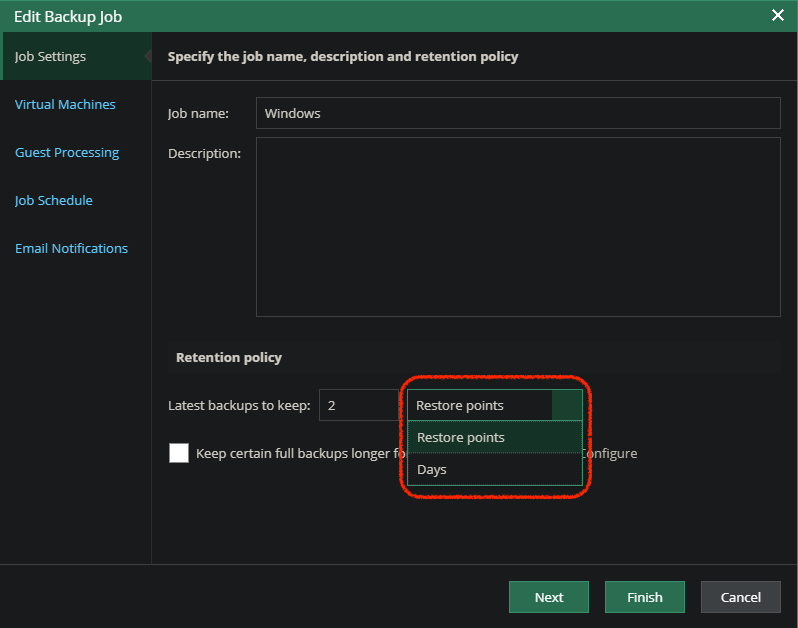
Version 10 of Veeam Backup & Replication right around the corner as we rapidly approach GA. The RTM has been out for our service provider partners for a coup...
Late last week, Veeam made available to our VCSP partners the RTM of Veeam Backup & Replication 10 ( Build 10.0.0.4442 ). This is a much awaited version of B...
Version 10 of Veeam Backup & Replication isn't too far away and we are currently in the middle of a second private BETA for our customers and partners. There...
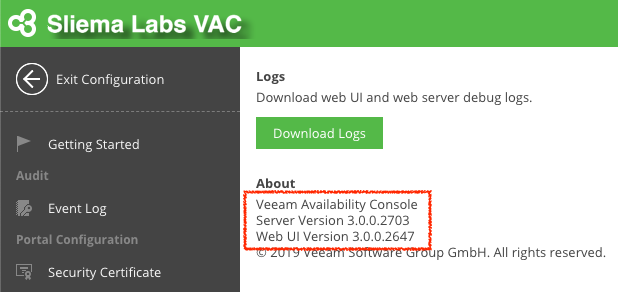
Today, a new patch was released for Veeam Availability Console v3 which brings the build to 3.0.0.2725 . Contained in this patch is a number of fixes that co...

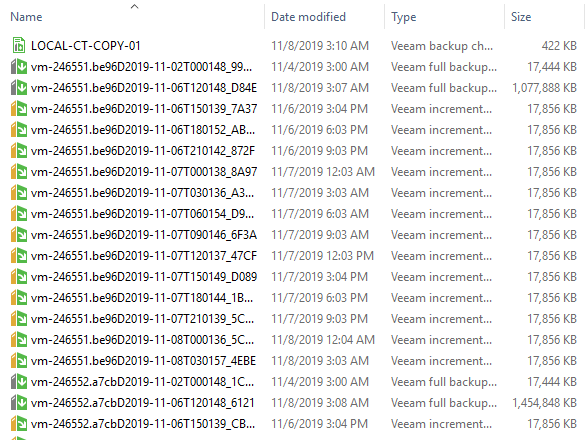
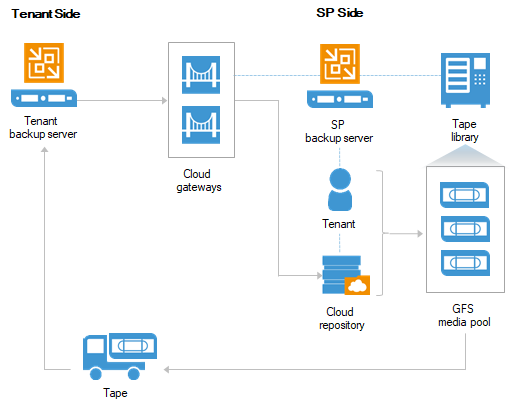
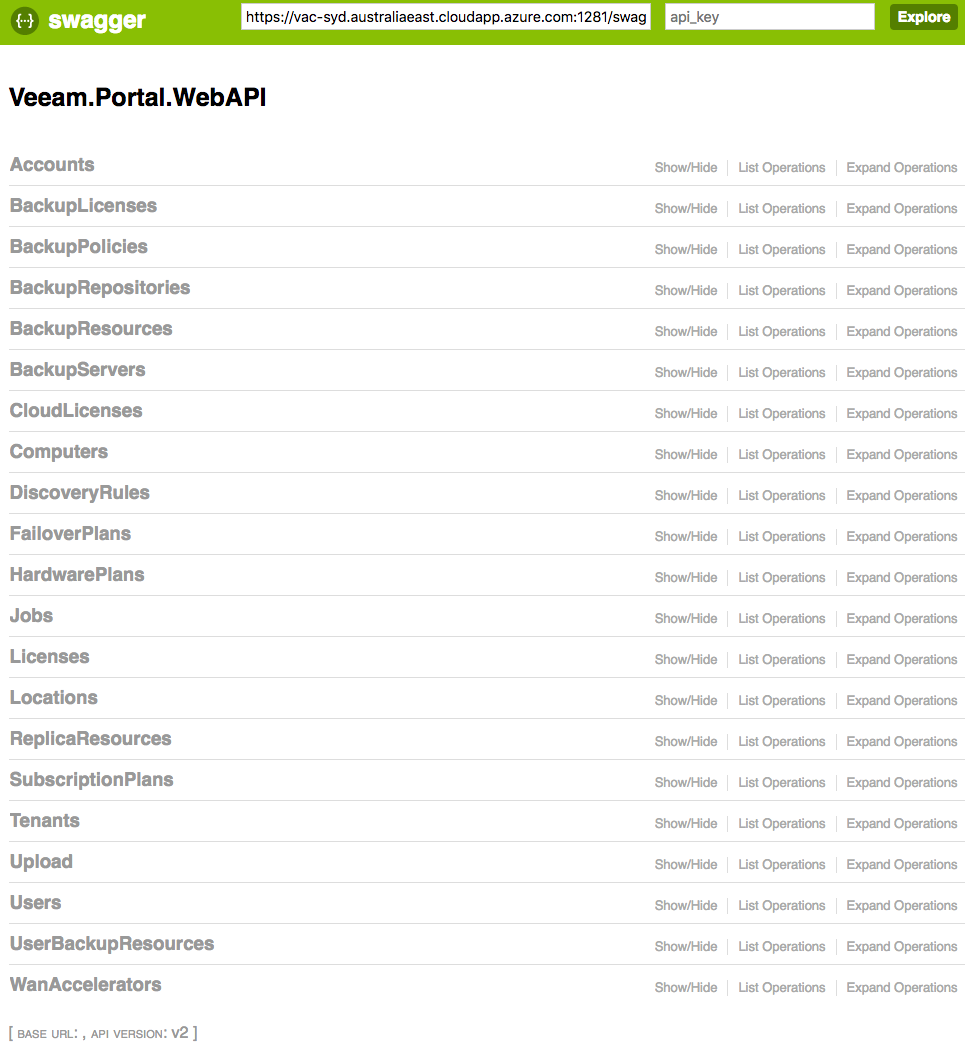
That is probably the longest title i've ever had on this blog, however I wanted to highlight everything that is contained in this solution. Everything above ...
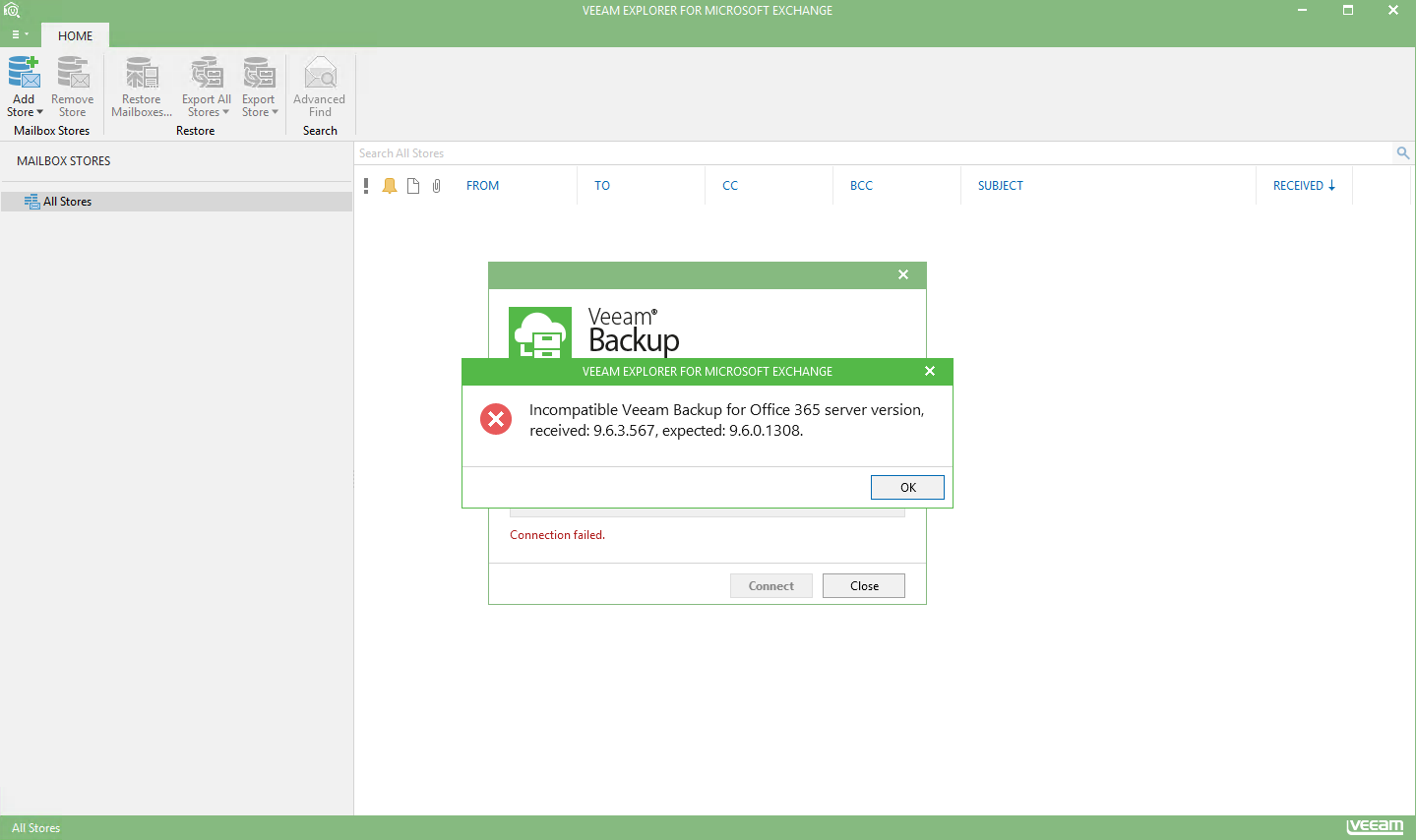
When Veeam Backup & Replication 9.5 Update 4 went Generally Available a couple of weeks ago I posted a What’s in it for Service Providers blog. In that post ...
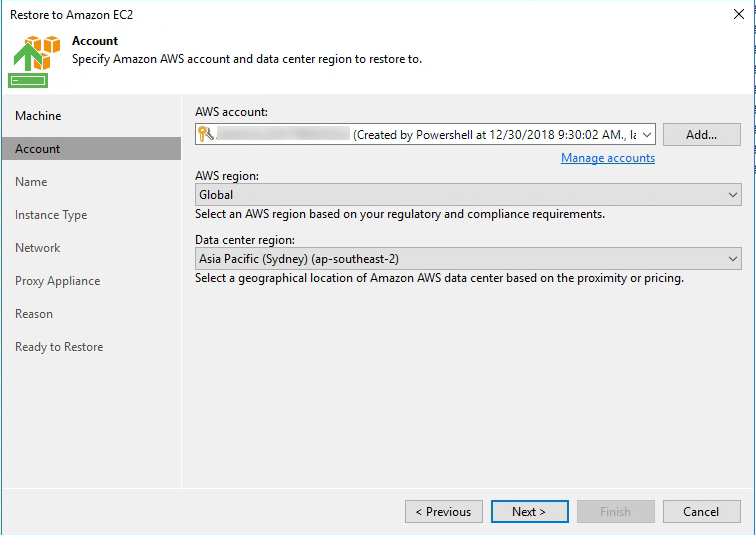
When Veeam Backup & Replication 9.5 Update 4 went Generally Available a couple of weeks ago I posted a What's in it for Service Providers blog. In that post ...
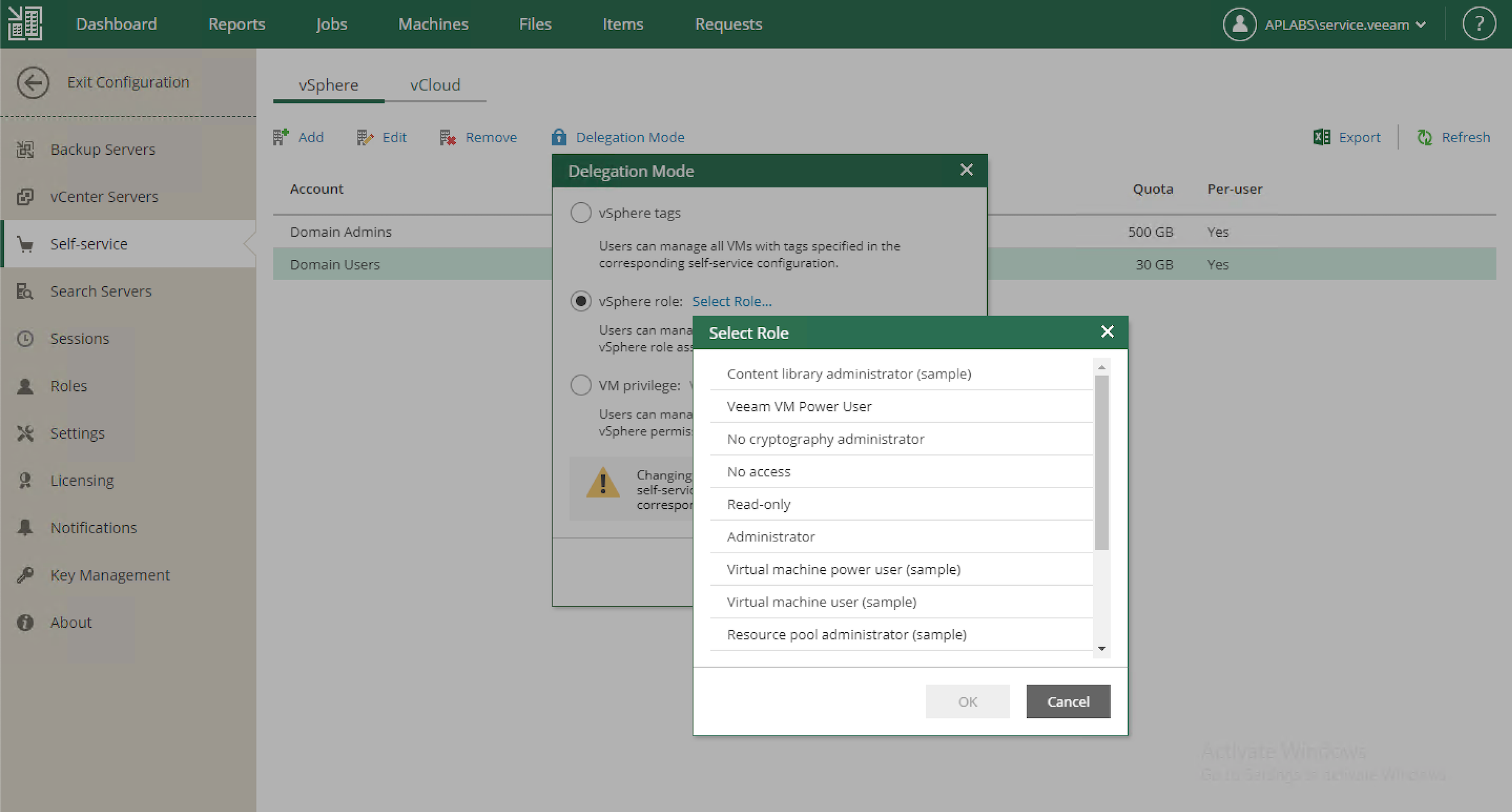
When Veeam Backup & Replication 9.5 Update 4 went Generally Available a couple of weeks ago I posted a What's in it for Service Providers blog. In that post ...
When Veeam Backup & Replication 9.5 Update 4 went Generally Available a couple of weeks ago I posted a What's in it for Service Providers blog. In that post ...

For ten plus years Veeam has continued to develop new innovative features and enhancements supporting our Cloud and Service Provider partners. As I posted ea...
I remember the day I first came across Veeam. It was mid 2010 and I was working for Anittel at the time. We had a large virtualisation platform that hosted a...
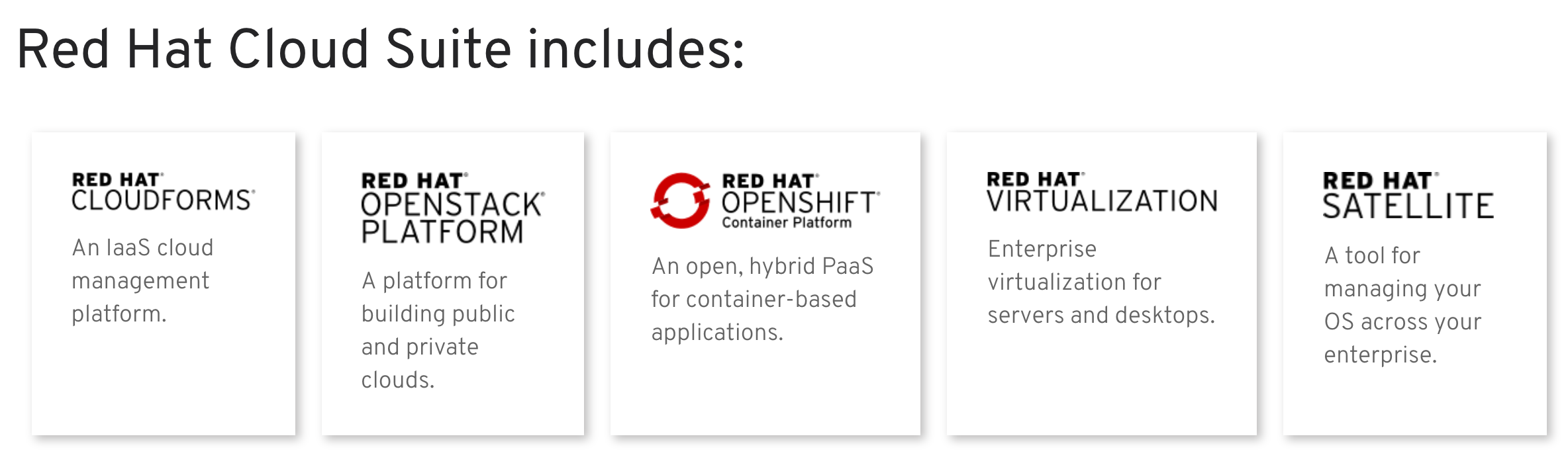
As Red October came to a close…at a time when US Tech stocks were taking their biggest battering in a long time the news came out over the weekend that IBM h...
A couple of weeks ago we released version 2.0 of Veeam Backup for Office 365 which added support for SharePoint and OneDrive. Earlier this year I wrote about...
Today, Veeam Availability Console Update 1 (Build 2.0.2.1750) was released . This update improves on our multi-tenant service provider management and reporti...

True innovation is solving a real problem ...and though for the most, it's startups and tech giants that are seen to be the innovators, their customers and p...
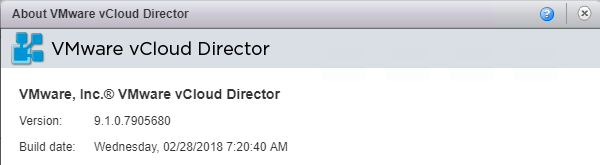
Overnight VMware released vCloud Director 9.1 ( build 7905680 ) which builds on the 9.0 release that came out last September. This continues to deliver on VM...

For a few years now i've been compiling features and throughput numbers for NSX Edge Services Gateways. This started off comparing features and performance m...
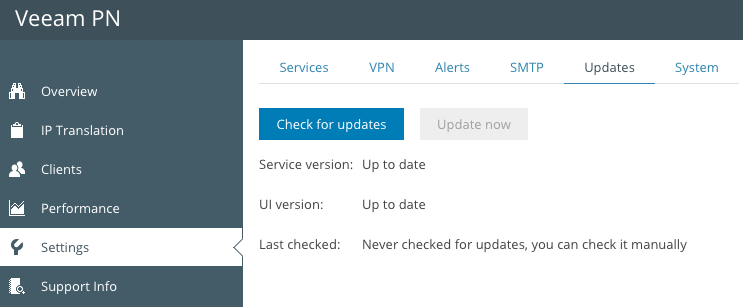
Last week, Veeam Powered Network ( Veeam PN ) was released to GA. As a quick reminder Veeam PN allows administrators to create, configure and connect site-to...

Today is the first day offical day of AWS re:Invent 2017 and things are kicking off with the global partner summit. Today also is my first day of AWS re:Inve...
Today is a good day! VMware have released to GA vCloud Director 9.0 ( build 6681978 ) and with it come the most significant feature and enhancements of any p...
Last week at VMworld 2017 in the US, VMware announced the initial availability of VMware Cloud on AWS . It was the focal point for VMware at the event and pr...
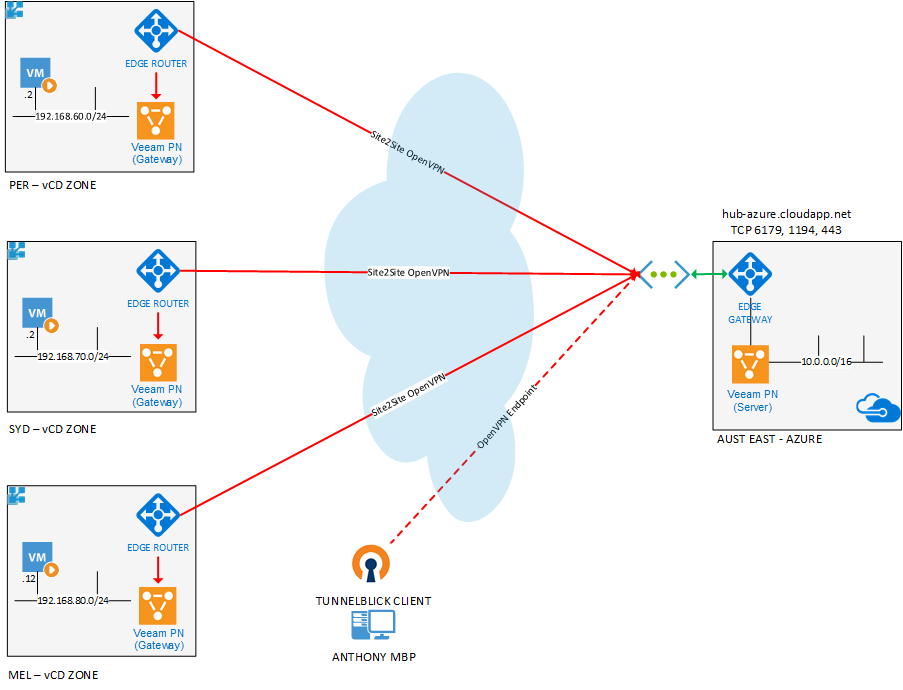
I've written a couple of posts on how Veeam Powered Network can make accessing your homelab easy with it's straight forward approach to creating and connecti...

In July of 2011, Distribute.IT, a domain registration and web hosting services provider in Australia was was hit with a targeted, malicious attack that resul...